A major security vulnerability was discovered in the Microsoft Events platform, which could have allowed unauthorized access to personal information stored in two separate databases — the event registration list and the waitlist database.
Discovery of the Flaw
The issue was identified by a 15-year-old bug bounty researcher, known as Faav, who uncovered that the flaw exposed sensitive personal details including full names, email addresses, phone numbers, and in certain cases, physical addresses.
The vulnerability was responsibly disclosed to Microsoft, and the company has since patched the issue to secure its systems.
The researcher began the investigation by exploring the events.microsoft.com subdomain. This analysis led to the discovery of several API endpoints hosted under msevents.microsoft.com, which became the key to finding the data exposure

Testing the Endpoints
Initial vulnerability tests on multiple endpoints did not yield any sensitive information. The first hint of weakness appeared when an OData injection flaw was found in the /api/GetEvents endpoint.
However, this particular endpoint was limited, as it only returned public event information. Attempts to query other data tables such as accounts or contacts resulted in errors, suggesting restricted access.
A similar injection vulnerability was then identified in another endpoint, /api/GetEventCustomRegistrationFields, which allowed the enumeration of all Microsoft events. Even so, this still did not reveal any private or user-specific data.
The Key Vulnerability
The real breakthrough came when the researcher examined the /api/CheckEventRegistration POST endpoint. This API function was meant to verify whether a user’s email address was already registered for an event.
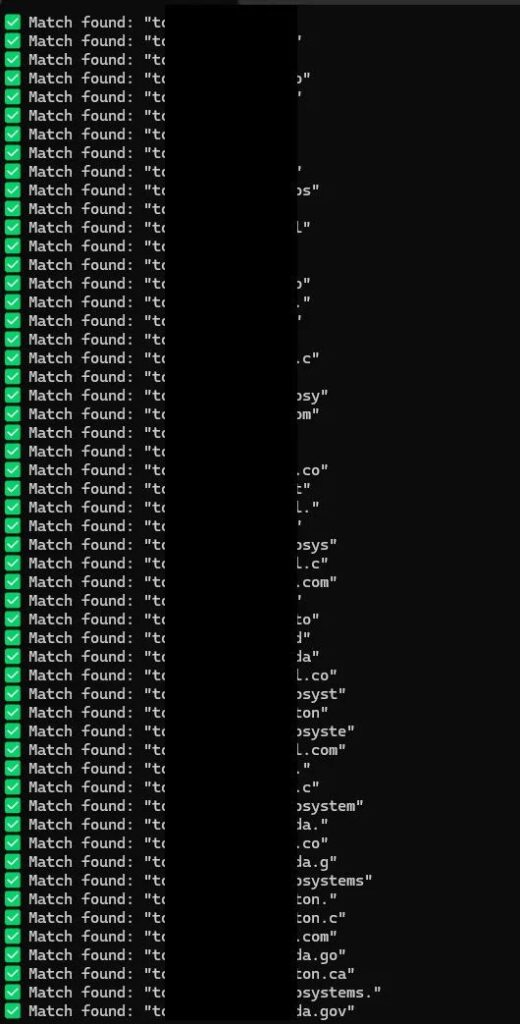
By injecting malicious payloads into the email and eventId fields, the researcher discovered a way to manipulate the system’s database queries.
Using a precise OData injection technique, Faav determined that the endpoint sent two separate requests to two distinct databases. This allowed him to carefully target each one individually.
One crafted injection made it possible to enumerate the entire Waitlist database, revealing fields such as:
- fullname
- telephone1
- address1_line1
- company
- email addresses (including government and corporate domains)
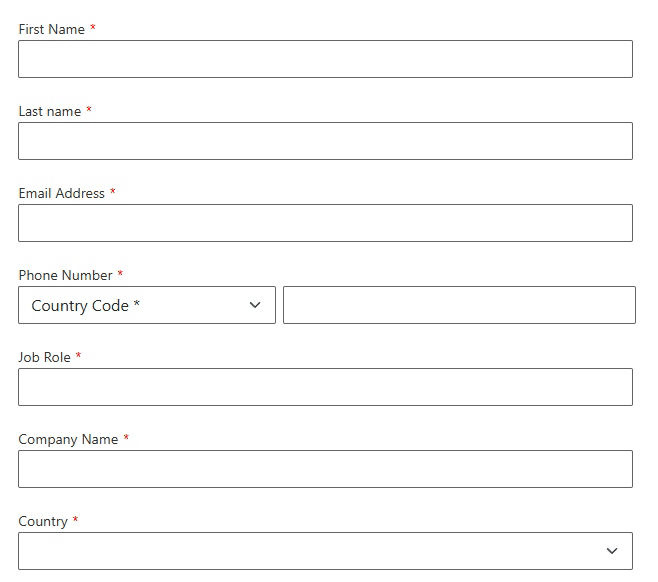
Contact form
By reversing the injection method, the researcher gained access to the second database — the Event Registration List. This dataset contained:
- first name
- last name
- phone number
- company name
- country
Some event entries also stored Partner IDs and Tenant IDs, adding to the sensitivity of the exposed data.
Lack of Rate Limiting and Reporting
The researcher noted that there were no rate-limiting controls in place. This meant that a threat actor could have automated the data extraction process to harvest all user information from both databases.
After confirming the vulnerability and demonstrating its potential impact, Faav immediately reported the findings to the Microsoft Security Response Center (MSRC) on July 23, 2025.
According to the official timeline, Microsoft acknowledged and fixed the vulnerability by August 26, 2025, closing off the risk before it could be exploited in the wild.


