Microsoft has successfully taken legal measures in the U.S. and U.K. to dismantle RedVDS, a subscription-based cybercrime service that enabled criminals to carry out widespread online fraud. The action included seizing domains redvds[.]com, redvds[.]pro, and vdspanel[.]space, effectively taking the illegal service offline.
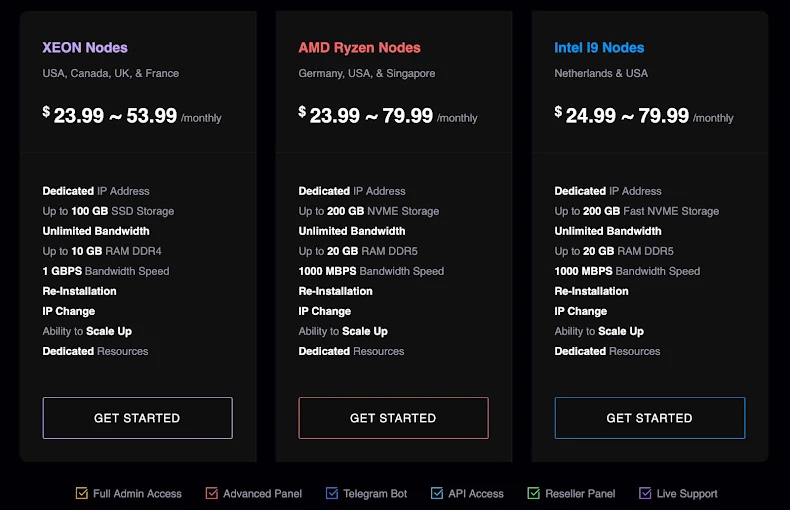
RedVDS allowed threat actors to access cheap, disposable virtual computers for as little as $24 per month, providing a scalable and hard-to-trace platform for malicious activity. Microsoft estimates that RedVDS-driven operations caused roughly $40 million in reported fraud losses in the U.S. alone since March 2025.

How RedVDS Operated
RedVDS functioned as a crimeware-as-a-service (CaaS) platform, offering virtual machines (VMs) running unlicensed Windows with full administrator access. Features included:
- Subscription-based RDP servers located in multiple countries including the U.S., Canada, U.K., Germany, France, the Netherlands, and Singapore
- Reseller panels to create sub-users without sharing main access
- Integration with Telegram bots for remote server management
- No activity logging, making it attractive for illicit operations
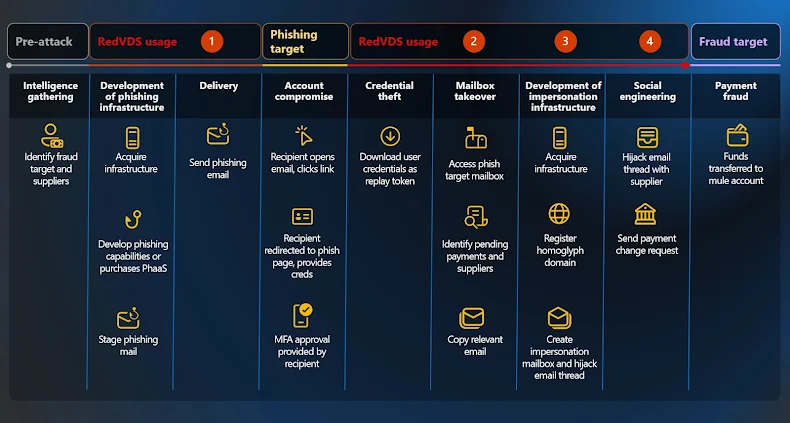
The platform facilitated a variety of criminal activities, including phishing campaigns, business email compromise (BEC), account takeovers, and financial fraud.
RedVDS servers were frequently paired with generative AI tools to identify high-value targets, craft realistic phishing emails, and even employ face-swapping, video manipulation, and voice-cloning techniques to impersonate individuals convincingly.
Scope of the Attacks
Since September 2025, RedVDS-powered attacks impacted over 191,000 organizations globally, spanning sectors like legal, construction, healthcare, education, manufacturing, and real estate. Threat actors primarily operated under monikers like Storm-2470, with collaborators such as Storm-2227, Storm-1575, and Storm-1747, leveraging the infrastructure for phishing and fraud.
Some notable techniques included:
- Mass email spam using tools like SuperMailer, UltraMailer, and BlueMail
- Harvesting email addresses using tools like Sky Email Extractor
- Using VPNs, secure browsers, and remote access tools (e.g., AnyDesk) for anonymity
- Leveraging AI tools (ChatGPT, OpenAI) to craft lures and automate attacks
Technical Details of RedVDS Infrastructure
RedVDS operated by cloning a single Windows Server 2022 evaluation image. All virtual machines used the same computer name (WIN-BUNS25TD77J) and were provisioned through Quick Emulator (QEMU) with VirtIO drivers.
This setup allowed Storm-2470 to rapidly deploy new RDP hosts on demand, scaling operations within minutes and enabling threat actors to:
- Stage phishing infrastructure
- Steal credentials
- Hijack email accounts
- Conduct impersonation-based BEC fraud
The cloned hosts were deliberately designed to offer a low-cost, resilient, and permissive environment, making it simple for criminals to launch multi-stage operations with minimal friction.
Impact and Significance
RedVDS demonstrates the growing sophistication of CaaS models in cybercrime, turning complex attacks into accessible operations for less technically skilled actors. By combining low-cost disposable infrastructure, AI-assisted deception, and cloned Windows VMs, RedVDS enabled highly scalable and persistent online fraud campaigns.
Microsoft’s legal action, combined with global law enforcement cooperation, disrupted the infrastructure and prevented continued misuse of the service, signaling a strong precedent against subscription-based cybercrime operations.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


