Microsoft has issued a security warning about ongoing phishing campaigns that misuse OAuth URL redirection mechanisms to bypass traditional email and browser based phishing defenses.
According to the Microsoft Defender Security Research Team, the attacks primarily target government and public sector organizations. Instead of stealing authentication tokens or exploiting software vulnerabilities, the campaigns manipulate legitimate OAuth functionality to redirect victims to attacker controlled infrastructure.
Abuse of Legitimate OAuth Redirection
OAuth includes a built in feature that allows identity providers to redirect users to designated landing pages during certain authentication flows, particularly in error scenarios. Microsoft explained that threat actors are taking advantage of this intended behavior.
Attackers craft malicious URLs using trusted identity platforms such as Entra ID and Google Workspace. By modifying specific parameters or linking the URL to rogue applications under their control, they create links that appear legitimate but ultimately redirect users to harmful destinations.
This tactic represents an identity based attack technique rather than a direct exploit of security flaws.
How the Attack Chain Works
The campaign begins with the creation of a malicious OAuth application inside an attacker controlled tenant environment. The rogue app is configured with a redirect URL that points to a domain hosting malware.
Phishing emails are then distributed to targets, urging them to authenticate to the malicious application. The authentication request contains an intentionally invalid scope parameter. When the process fails, OAuth’s redirection mechanism sends the user to the attacker specified landing page.
As a result, victims are unknowingly prompted to download a malicious ZIP archive.
Malware Delivery and Execution Techniques
Once downloaded and extracted, the ZIP file reveals a Windows shortcut file, LNK, that immediately executes a PowerShell command when opened.
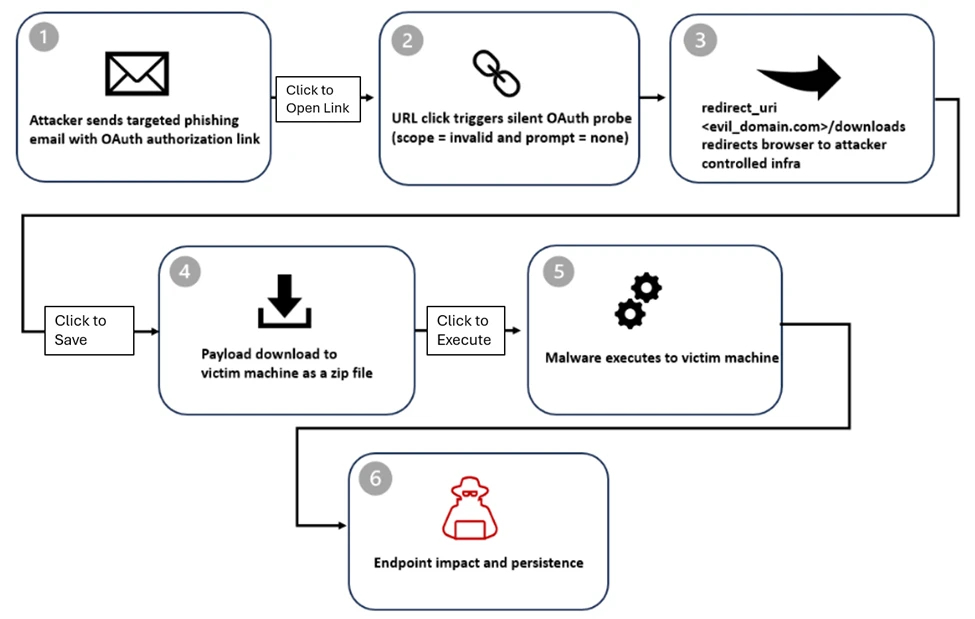
The PowerShell script performs reconnaissance on the compromised system by running discovery commands. The LNK file also extracts an MSI installer, which drops a decoy document to distract the victim.
Meanwhile, a malicious dynamic link library file named crashhandler.dll is side loaded using a legitimate binary called steam_monitor.exe. The DLL decrypts an additional file, crashlog.dat, and executes the final payload directly in memory.
This last stage establishes communication with an external command and control server, enabling further malicious activity such as pre ransomware operations or hands on keyboard attacks.
Sophisticated Phishing Themes and Delivery Methods
Microsoft reported that the phishing emails used persuasive themes including e signature requests, Microsoft Teams recordings, social security notifications, financial alerts, and political topics.
The emails were distributed using mass mailing tools and custom scripts developed in Python and Node.js. Malicious links were either embedded directly in the email body or placed within attached PDF files.
To increase credibility, attackers encoded the target’s email address into the OAuth state parameter. While the state parameter is designed to correlate authentication requests and responses securely, it was repurposed to automatically populate the victim’s email address on the phishing page.
Use of Adversary in the Middle Frameworks
In some cases, the OAuth redirection technique was used purely for malware delivery. In others, victims were redirected to credential harvesting pages hosted on adversary in the middle frameworks such as EvilProxy.
These platforms intercept login credentials and session cookies, allowing attackers to bypass multi factor authentication and gain unauthorized access to accounts.
Mitigation and Security Recommendations
Microsoft confirmed that several malicious OAuth applications identified during the investigation have been removed.
Organizations are strongly advised to restrict user consent for third party applications, conduct regular audits of application permissions, and eliminate unused or excessively privileged apps.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.