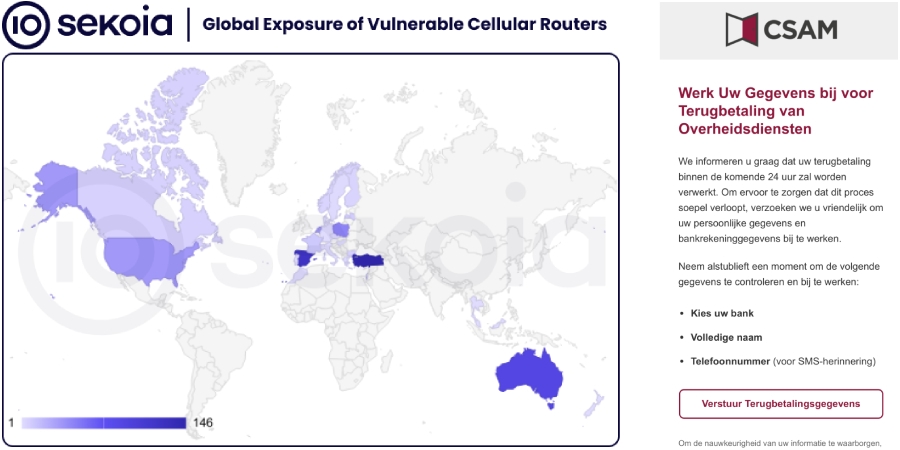
Unknown threat actors have abused Milesight industrial cellular routers to send phishing SMS messages, or smishing, targeting users across several European countries since at least February 2022. French cybersecurity firm SEKOIA reports that attackers leveraged exposed router APIs to distribute malicious links, with a focus on Sweden, Italy, and Belgium. The campaigns impersonated government services, banks, postal and telecom providers, using typosquatted domains to deceive victims.
What happened, and why it matters
Security researchers found that some Milesight industrial cellular routers expose SMS-related application programming interfaces, or APIs, without requiring authentication. Attackers abused these APIs to send phishing URLs by SMS, enabling a decentralised and hard-to-takedown delivery mechanism. The technique lets threat actors push malicious content across multiple countries while complicating detection and remediation efforts.
Scope and scale, exposed devices and locations
Of roughly 18,000 Milesight routers reachable on the public internet, SEKOIA assessed that at least 572 devices were potentially vulnerable because they exposed inbox and outbox SMS APIs. Around half of those identified vulnerable routers are located in Europe, and the campaigns primarily targeted Sweden, Italy, and Belgium. The exposed APIs also allow retrieval of incoming and outgoing SMS messages, which indicates the vulnerability was not just theoretical, but actively exploited in smishing operations.
Vulnerability used, CVE and timeline
Researchers believe the attackers relied on an information disclosure vulnerability in Milesight routers, tracked as CVE-2023-43261, with a CVSS score of 7.5. That flaw, disclosed by researcher Bipin Jitiya two years ago, was patched by the vendor, but evidence suggests weaponization followed soon after public disclosure. SEKOIA notes however that some vulnerable routers are running newer firmware that should not be susceptible, implying that public exposure may sometimes be due to misconfiguration rather than an unpatched firmware alone.
How the smishing campaigns operated, technical details
The campaigns used SMS messages that pointed recipients to typosquatted domains impersonating government platforms, such as CSAM reporting portals and eBox, as well as banking, postal, and telecom services. The phishing pages often contained JavaScript that first verified whether the visitor was on a mobile device, before delivering the malicious content designed to trick users into updating banking or personal information under false pretenses.
Between January and April 2025, at least one domain used in these campaigns, jnsi[.]xyz, included JavaScript to disable right-click and browser debugging tools, attempting to hinder analysis. Some pages logged visitor details to a Telegram bot named GroozaBot, which appears linked to an operator using the handle “Gro_oza,” who communicates in Arabic and French.
Threat actors appear to have validated routers before large-scale use, sending test SMS messages to phone numbers they control to confirm the device could send messages. The absence of signs indicating backdoors or other post-exploitation activity suggests the attackers focused narrowly on SMS delivery for their smishing campaigns.
Why industrial routers are attractive to attackers
Industrial cellular routers, such as those from Milesight, are often deployed across many sites and countries for remote telemetry, automation, and connectivity. Their distribution, combined with SMS-capable firmware, makes them useful platforms for decentralised message delivery. When APIs are left exposed, or devices are misconfigured, attackers can weaponize them as anonymous SMS gateways, helping bypass conventional email and web-based filters.
Indicators of compromise and notable artefacts
Key indicators include:
- Routers exposing inbox/outbox SMS APIs to the internet,
- SMS messages containing typosquatted domains that mimic government or financial services,
- Phishing pages that check for mobile user agents before showing malicious content,
- JavaScript that disables right-click and debugging consoles,
- Logging to Telegram bots, specifically GroozaBot, linked to an operator named “Gro_oza.”
Mitigation, defensive recommendations for organisations and operators
If you manage Milesight routers, industrial cellular gateways, or similar devices, take these steps immediately, especially if devices are internet-facing:
- Verify firmware, and update to the latest vendor-recommended version that patches CVE-2023-43261, or any subsequent security fixes.
- Restrict access to device management interfaces and APIs, using firewalls, VPNs, and network segmentation to prevent public exposure.
- Disable SMS-related administrative APIs unless they are strictly required for operations.
- Rotate default credentials, enforce strong passwords, and enable any available multi-factor authentication for device management.
- Monitor outbound SMS activity logs for unusual volumes or destinations, and investigate any tests to unknown phone numbers.
- Block or monitor known malicious domains and typosquatted variants at DNS and web gateway layers.
- Share indicators, such as malicious domains and Telegram bot handles, with your incident response and threat intelligence teams to enable proactive blocking and takedown efforts.