Cybersecurity experts have uncovered a highly sophisticated social engineering campaign that is deploying MixShell, a stealthy in-memory malware, against key manufacturing companies vital to the global supply chain.
This malicious operation, tracked by Check Point Research under the name ZipLine, takes an unusual approach to infiltration.
A Shift from Traditional Phishing
Instead of relying on spam emails, the attackers start by reaching out through a company’s official Contact Us page. Employees are lured into what appears to be a professional exchange that can last several weeks. These conversations often involve fake Non-Disclosure Agreements (NDAs) and eventually lead to the delivery of a weaponized ZIP file carrying the MixShell malware.
The attackers have cast a wide net, targeting multiple industries and regions, but with a particular focus on U.S.-based manufacturing firms. The primary victims include companies in industrial machinery, metalwork, engineered systems, semiconductors, biotechnology, consumer goods, and pharmaceuticals. Other countries affected include Singapore, Japan, and Switzerland.
Advanced Social Engineering
Unlike many phishing operations that use scare tactics or urgency, ZipLine attackers rely on patience and credibility. Some victims are drawn into multi-week discussions before receiving the malware-laced ZIP files.
In recent cases, attackers even posed as partners offering AI-driven solutions to cut costs and boost efficiency, exploiting the ongoing global interest in artificial intelligence.

Technical Breakdown of the Attack Chain
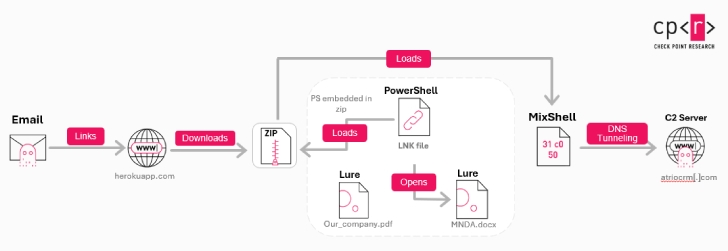
The malicious ZIP archives are equipped with a Windows shortcut (LNK) file that launches a PowerShell loader. This loader deploys the MixShell implant directly in memory, avoiding traditional detection methods.
Key technical features include:
- DNS tunneling and HTTP fallback C2 channels for command-and-control
- Remote command execution, file operations, and reverse proxying
- Stealth persistence mechanisms for deeper infiltration
- A PowerShell variant with advanced anti-debugging, sandbox evasion, and scheduled task persistence
The malware is often hosted on subdomains of herokuapp[.]com, a legitimate PaaS provider. By blending malicious traffic with normal enterprise activity, attackers make detection far more difficult.
Check Point also noted that the attackers use fake LLC domains and cloned business websites to appear authentic, reinforcing the illusion of legitimacy.
Potential Impact
The consequences of such attacks are severe and far-reaching. Successful infections could result in:
- Theft of intellectual property
- Business email compromise and account takeovers
- Financial fraud and ransomware deployment
- Disruption of supply chains with cascading global effects
Expert Warning
According to Sergey Shykevich, Threat Intelligence Group Manager at Check Point Research:
“The ZipLine campaign is a wake-up call for organizations that still think phishing only comes in the form of suspicious email links. Attackers are now blending human psychology, trusted communication channels, and AI-themed lures to bypass defenses. Companies must prioritize prevention-first strategies and build a culture of vigilance.”


