Iranian-affiliated cyber group MuddyWater has launched a large-scale espionage campaign targeting more than 100 organizations, mainly across the Middle East and North Africa (MENA) region. The group has reportedly used a compromised email account to distribute a backdoor malware called Phoenix, aiming to infiltrate high-value targets and gather intelligence, according to a technical report by Singapore-based cybersecurity firm Group-IB.
Over three-quarters of the targeted entities are embassies, diplomatic missions, foreign ministries, and consulates. Other targets include international organizations and telecom companies.
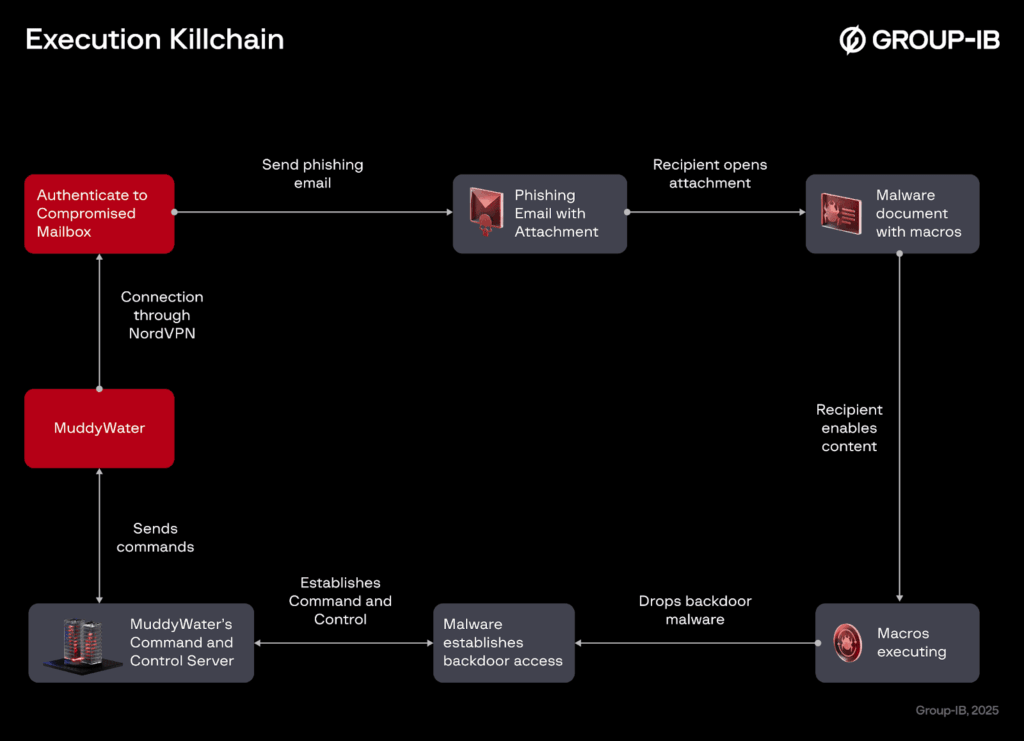
Researchers Mahmoud Zohdy and Mansour Alhmoud explained that MuddyWater exploited NordVPN, a legitimate service, to access the compromised mailbox and send phishing emails that looked authentic. This approach increased the likelihood that recipients would open the malicious attachments.
The attack works through weaponized Microsoft Word documents. When recipients open these files, they are prompted to enable macros to view the content. Enabling macros triggers malicious VBA code, which installs version 4 of the Phoenix backdoor. The backdoor is deployed using a loader called FakeUpdate, which decodes the AES-encrypted Phoenix payload and writes it to disk.
MuddyWater, also known under names such as Boggy Serpens, Cobalt Ulster, Earth Vetala, Mango Sandstorm, Seedworm, Static Kitten, TA450, TEMP.Zagros, and Yellow Nix, is believed to be linked to Iran’s Ministry of Intelligence and Security (MOIS). The group has been active since at least 2017.
Group-IB first reported the use of Phoenix last month, noting it as a lightweight version of BugSleep, a Python-based implant associated with MuddyWater. Two Phoenix variants, Version 3 and Version 4, have been observed in attacks.
The attackers’ command-and-control (C2) server, 159.198.36[.]115, has been found hosting remote monitoring and management (RMM) tools and a custom browser credential stealer targeting Brave, Chrome, Edge, and Opera. MuddyWater has a history of using phishing campaigns to distribute remote access software.
By combining Phoenix v4, the FakeUpdate loader, custom credential-stealing tools, and legitimate RMM utilities like PDQ and Action1, MuddyWater has enhanced its ability to remain stealthy and persistent in targeted networks.