Cybersecurity researchers have uncovered a sophisticated attack by the Chinese threat actor Mustang Panda, which utilized a previously unknown kernel-mode rootkit driver to deploy the TONESHELL backdoor. The campaign, detected in mid-2025, primarily targeted government organizations in Southeast and East Asia, including Myanmar and Thailand.
According to Kaspersky, the malicious driver, named ProjectConfiguration.sys, is digitally signed using a certificate from Guangzhou Kingteller Technology Co., Ltd., likely obtained through theft or leakage. This kernel-mode minifilter driver is designed to inject backdoor code into system processes while protecting both malicious files and user-mode processes from detection or deletion.
Attack Methodology and TONESHELL Deployment
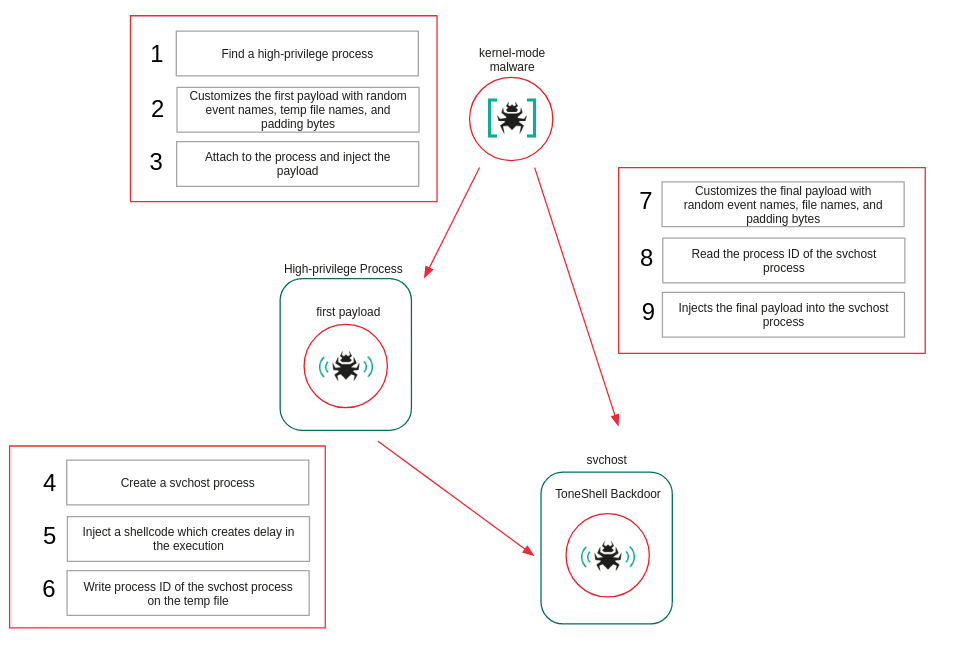
The rootkit carries two embedded user-mode shellcodes executed as separate threads. The first payload spawns an svchost.exe process and injects a delay-inducing shellcode, while the second delivers the TONESHELL backdoor into the same process. Once active, TONESHELL establishes a TCP connection over port 443 to its command-and-control (C2) servers, including avocadomechanism[.]com and potherbreference[.]com. The malware allows operators to download, upload, cancel transfers, establish a remote shell, and execute commands, all while remaining stealthy.
Advanced Rootkit Capabilities
Kaspersky highlights that the driver employs advanced techniques to evade detection:
- Dynamic resolution of kernel APIs using hashed addresses
- Monitoring and preventing file deletion or renaming
- Blocking access to protected registry keys via a RegistryCallback at altitude 330024+
- Altering Microsoft Defender driver altitudes to bypass security filters
- Intercepting process operations for protected process IDs, removing protections post-execution
These methods ensure the malicious driver operates below legitimate antivirus and security layers, making detection extremely challenging.
Significance of Kernel-Mode Delivery
The deployment of TONESHELL through a signed kernel-mode loader marks a notable escalation in Mustang Panda’s operations. Memory forensics is critical for identifying the injected shellcode, as the backdoor executes entirely in memory. Researchers emphasize that the combination of kernel-mode protection, obfuscation, and multi-stage injection significantly enhances the stealth and resilience of the malware, allowing prolonged persistence in targeted systems.
Kaspersky concludes that Mustang Panda’s 2025 campaigns demonstrate a clear evolution toward using kernel-mode injectors for backdoor deployment, signaling increased sophistication in cyber espionage tools.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


