A newly uncovered backdoor malware known as MystRodX has raised alarms in the cybersecurity community. Operating silently for more than 20 months, this advanced threat has been able to exfiltrate sensitive information using covert communication techniques that bypass standard defenses.
Initially mistaken for a Mirai botnet variant, MystRodX is far more dangerous. Instead of relying on traditional command-and-control (C2) mechanisms, it leverages DNS queries and ICMP packets as hidden channels to interact with its operators. This dual-mode design makes it extremely difficult for defenders to detect and block.
Discovery and Initial Confusion
The malware was first observed on June 6, 2025, when suspicious activity originated from IP address 139.84.156.79. The server distributed an ELF binary file named dst86.bin. At first, antivirus engines flagged it as Mirai with a very low detection ratio (4/65 on VirusTotal). However, in-depth analysis by XLab’s Cyber Threat Insight and Analysis System revealed that the threat was in fact a C++ backdoor equipped with stealth techniques far beyond Mirai.
Passive Stealth Mode
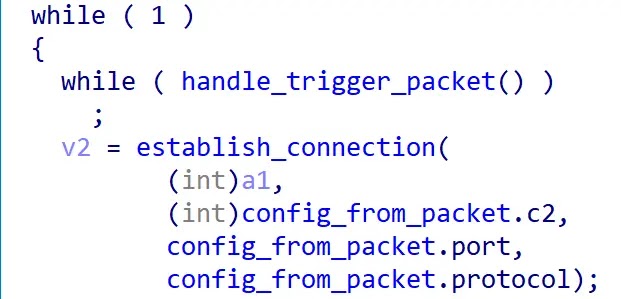
One of the features that makes MystRodX so elusive is its passive operational mode. Unlike traditional malware that binds to ports or constantly communicates with its C2, MystRodX can remain completely silent on the network. This allows it to avoid detection by intrusion detection systems (IDS) and traditional monitoring tools.
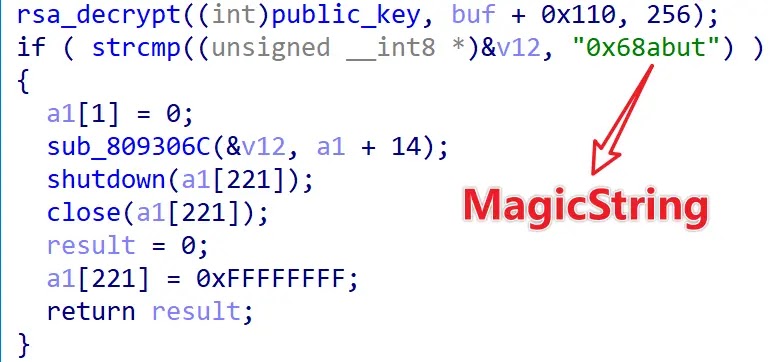
Triple-Layered Encryption
To protect its components, the malware uses a multi-tier encryption strategy:
- Single-byte XOR encoding for virtual machine (VM) detection strings
- Custom transform algorithms to generate AES keys and trigger packets
- AES-CBC encryption for its configuration files
This design ensures that even if security researchers capture parts of the malware, the critical sections remain hidden. Configuration logs show activation timestamps as early as January 7, 2024, indicating widespread deployment.
Command-and-Control Infrastructure
So far, analysts have identified three active C2 servers linked to MystRodX. Each server uses distinct RSA key pairs, suggesting that multiple campaigns are running in parallel. Researchers believe more undiscovered infrastructure may exist.
DNS-Based Activation
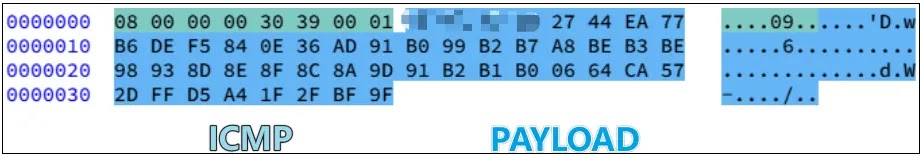
The most innovative aspect of MystRodX lies in its DNS-triggered activation system. The malware monitors all incoming traffic using raw sockets. When it detects a specially crafted DNS query, it interprets it as a command.
A typical trigger follows the format www.DomainName.com, where the domain name encodes activation instructions.
For example:www.UBw98KzOQyRpoSgk5+ViISKmpC6ubi7vao=.com
This domain contains a Base64-encoded string. Once decoded, it produces a 32-byte ciphertext containing hidden activation parameters.
Using a custom transform algorithm with predefined values (0x0d and 0xaa), the malware decrypts the payload to reveal critical data such as:
- A magic identifier (“CAT”)
- Protocol specifications (TCP/HTTP)
- Target port number
- IP address of the C2 server
# Transform algorithm implementation
def transform(magic, magic2, buf, key):
buf_len = len(buf) - 1
key_len = len(key)
key1 = magic ^ calc_sum(key)
key2 = (key[(key1^buf_len)%key_len]) ^ magic2 ^ buf_len
out = bytearray()
for i, value in enumerate(buf):
out.append((key[(i^key1)%key_len] ^ key2 ^ value ^ i) & 0xff)
return out
Active Backdoor Capabilities
Once activated, MystRodX transitions from passive surveillance to an active backdoor. It supports:
- File management (upload, download, delete)
- Reverse shell access
- SOCKS proxy setup
- Port forwarding for lateral movement
This broad range of functions gives attackers complete control over compromised machines, enabling both espionage and long-term persistence.