Cybersecurity researchers have uncovered a new malware campaign involving three malicious npm packages that were used to distribute a previously undocumented remote access trojan named NodeCordRAT. The discovery highlights ongoing risks within open source ecosystems, particularly for developers working with cryptocurrency related libraries.
Malicious Packages Identified
The following npm packages were identified as part of the campaign and were removed from the registry by November 2025. All were uploaded by a user operating under the name wenmoonx.
- bitcoin-main-lib with approximately 2,300 downloads
- bitcoin-lib-js with around 193 downloads
- bip40 with nearly 970 downloads
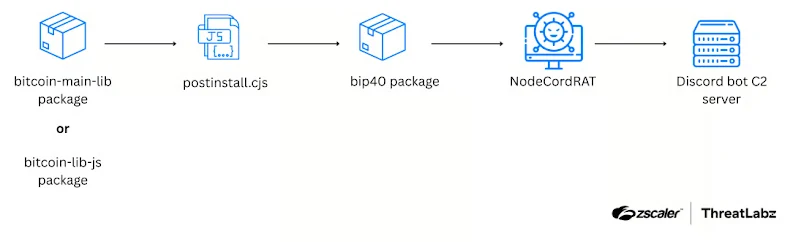
According to Zscaler ThreatLabz researchers Satyam Singh and Lakhan Parashar, the infection chain begins during installation. The bitcoin-main-lib and bitcoin-lib-js packages execute a postinstall.cjs script, which silently installs the bip40 package. This final component contains the NodeCordRAT malware payload.
How NodeCordRAT Operates
NodeCordRAT derives its name from two key elements of its operation. It uses npm packages as a delivery mechanism and relies on Discord servers for command and control communication. Once deployed, the malware is capable of stealing sensitive data, including Google Chrome credentials, API tokens, and cryptocurrency wallet seed phrases from extensions such as MetaMask.
Researchers noted that the threat actor deliberately named the malicious packages to closely resemble legitimate repositories from the bitcoinjs project. Examples include bitcoinjs-lib, bip32, bip38, and similar libraries. This naming strategy increased the likelihood of accidental installation by unsuspecting developers.
Both bitcoin-main-lib and bitcoin-lib-js contain a package.json file that specifies postinstall.cjs as a post installation script. This script ultimately triggers the execution of the bip40 package, activating the NodeCordRAT payload.
Command and Control via Discord
Beyond credential theft, NodeCordRAT fingerprints infected systems to generate a unique identifier across Windows, Linux, and macOS environments. It then establishes a covert communication channel using a hard coded Discord server.
Through this channel, attackers can issue several commands, including executing arbitrary shell commands via Node.js, capturing full desktop screenshots, and exfiltrating files from the compromised system. All stolen data is transmitted using Discord’s API with a hard coded authentication token and uploaded as message attachments to a private Discord channel.
Security Implications
This campaign underscores the growing trend of attackers abusing trusted developer platforms and popular communication services to evade detection. Developers are strongly advised to verify package authenticity, monitor post installation scripts, and use security scanning tools when working with third party dependencies, especially those related to cryptocurrency functionality.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


