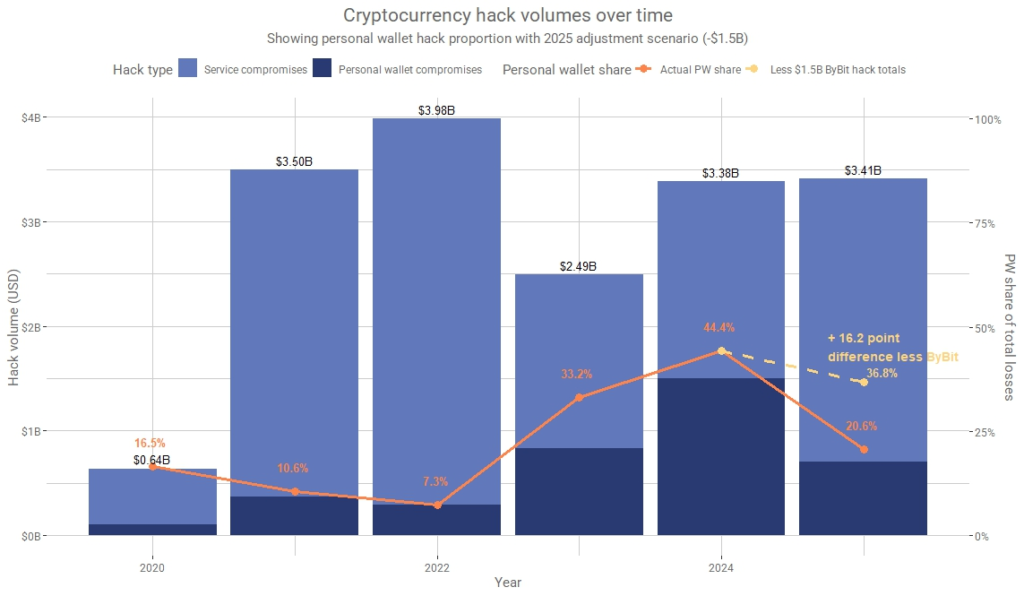
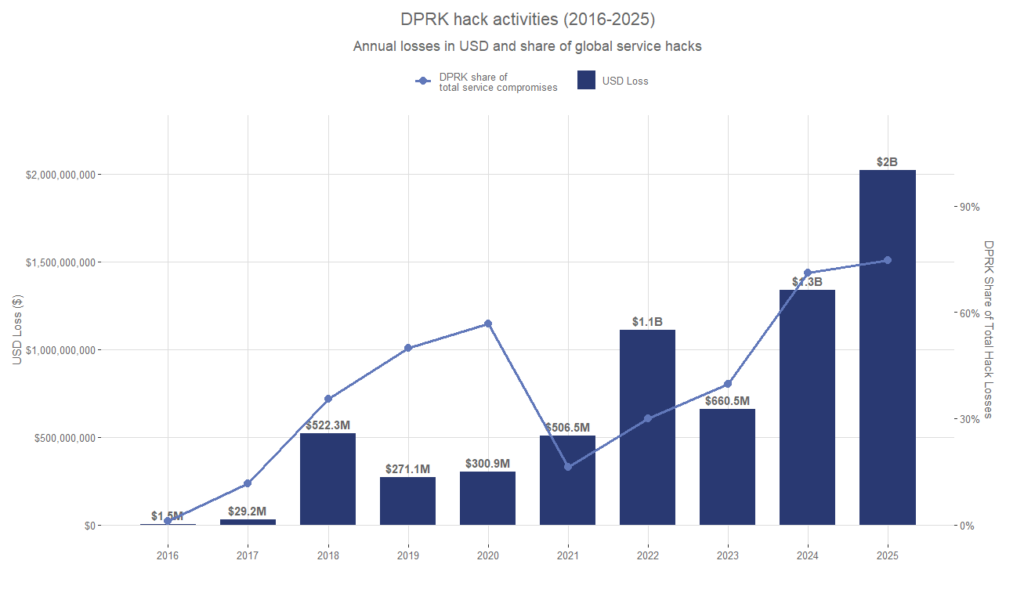
Threat actors associated with the Democratic People’s Republic of Korea, also known as North Korea, have emerged as the leading force behind global cryptocurrency theft in 2025. According to a new report released by blockchain intelligence firm Chainalysis, North Korea linked groups are responsible for stealing at least 2.02 billion dollars out of more than 3.4 billion dollars in total crypto losses recorded between January and early December 2025.
The findings, shared with The Hacker News, show a sharp 51 percent year over year increase in crypto theft activity. This figure is also 681 million dollars higher than 2024, when North Korean threat actors stole approximately 1.3 billion dollars. Chainalysis described 2025 as the most severe year on record for DPRK related cryptocurrency theft, with these actors accounting for nearly 76 percent of all service related compromises. The cumulative lower bound estimate of crypto funds stolen by DPRK linked groups has now reached 6.75 billion dollars.
A major portion of the losses can be traced to the February 2025 compromise of cryptocurrency exchange Bybit, which alone resulted in losses of 1.5 billion dollars. The attack was attributed to a North Korea linked threat cluster tracked as TraderTraitor, also known as Jade Sleet and Slow Pisces. Separate analysis by Hudson Rock connected the breach to a system infected with Lumma Stealer that was linked to Bybit related infrastructure.
These cryptocurrency thefts form part of a broader campaign conducted over the past decade by the notorious Lazarus Group. The group is also believed to be behind the theft of 36 million dollars from South Korea’s largest cryptocurrency exchange Upbit in late 2025. Lazarus Group is affiliated with Pyongyang’s Reconnaissance General Bureau and is estimated to have stolen at least 200 million dollars from more than 25 cryptocurrency heists between 2020 and 2023.
Beyond direct theft, the group has maintained long running social engineering campaigns such as Operation Dream Job. In these operations, victims working in defense, aerospace, manufacturing, chemical, and technology sectors are contacted through platforms like LinkedIn and WhatsApp with fake job offers. These interactions ultimately lead to the deployment of malware families including BURNBOOK, MISTPEN, and BADCALL, including Linux variants. The dual objective of these campaigns is intelligence collection and illicit revenue generation in violation of international sanctions.
Another major tactic involves embedding North Korean IT workers inside global companies using false identities. These operations are sometimes conducted through front companies such as DredSoftLabs and Metamint Studio. The scheme, commonly referred to as Wagemole, enables attackers to gain privileged access to cryptocurrency services and Web3 firms, significantly increasing the impact of subsequent breaches. Chainalysis noted that the expansion of this tactic has likely accelerated initial access and lateral movement prior to large scale theft.
Regardless of the entry method, stolen assets are laundered through Chinese language money movement networks, over the counter traders, cross chain bridges, and mixing services. Specialized marketplaces such as Huione are also used to obscure transaction trails. The laundering process typically unfolds over a structured 45 day period, starting with immediate layering through DeFi services, followed by integration via exchanges and cross chain bridges, and concluding with conversion into fiat currency or alternative assets.
The report also coincides with recent legal action in the United States. U.S. Department of Justice announced that Minh Phuong Ngoc Vong, a Maryland resident, was sentenced to 15 months in prison for participating in the IT worker infiltration scheme. Between 2021 and 2024, he enabled North Korean nationals based in Shenyang, China, to secure remote jobs at multiple U.S. companies and government agencies, including the Federal Aviation Administration.
Investigations further suggest that DPRK linked actors are now shifting strategy by acting as recruiters on freelance platforms such as Upwork and Freelancer. According to a report by Security Alliance, these recruiters guide collaborators through account creation, identity verification, and credential sharing, allowing attackers to operate under legitimate identities and evade detection.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


