Cybersecurity researchers have uncovered a new backdoor called AkdoorTea, linked to North Korean threat actors involved in the Contagious Interview campaign. This operation, also known by names such as DEV#POPPER, Famous Chollima, Gwisin Gang, Tenacious Pungsan, UNC5342, and Void Dokkaebi, primarily targets developers working on cryptocurrency and Web3 projects across Windows, Linux, and macOS.
According to Slovak cybersecurity firm ESET, which tracks the activity under the name DeceptiveDevelopment, the attackers use multi-platform tools that include obfuscated malicious scripts in Python and JavaScript, lightweight backdoors in Python and Go, and even dark web projects built in .NET.
Social Engineering Tactics
The campaign operates by impersonating recruiters on platforms like LinkedIn, Upwork, Freelancer, and Crypto Jobs List. Victims are lured with fake job opportunities and asked to either complete a coding assignment or undergo a video interview.
- Coding Assignments: Developers are tricked into cloning GitHub repositories that silently install malware.
- Video Assessments: Victims encounter fake technical errors, prompting them to run malicious commands in the terminal or command prompt under the guise of fixing microphone or camera access issues.
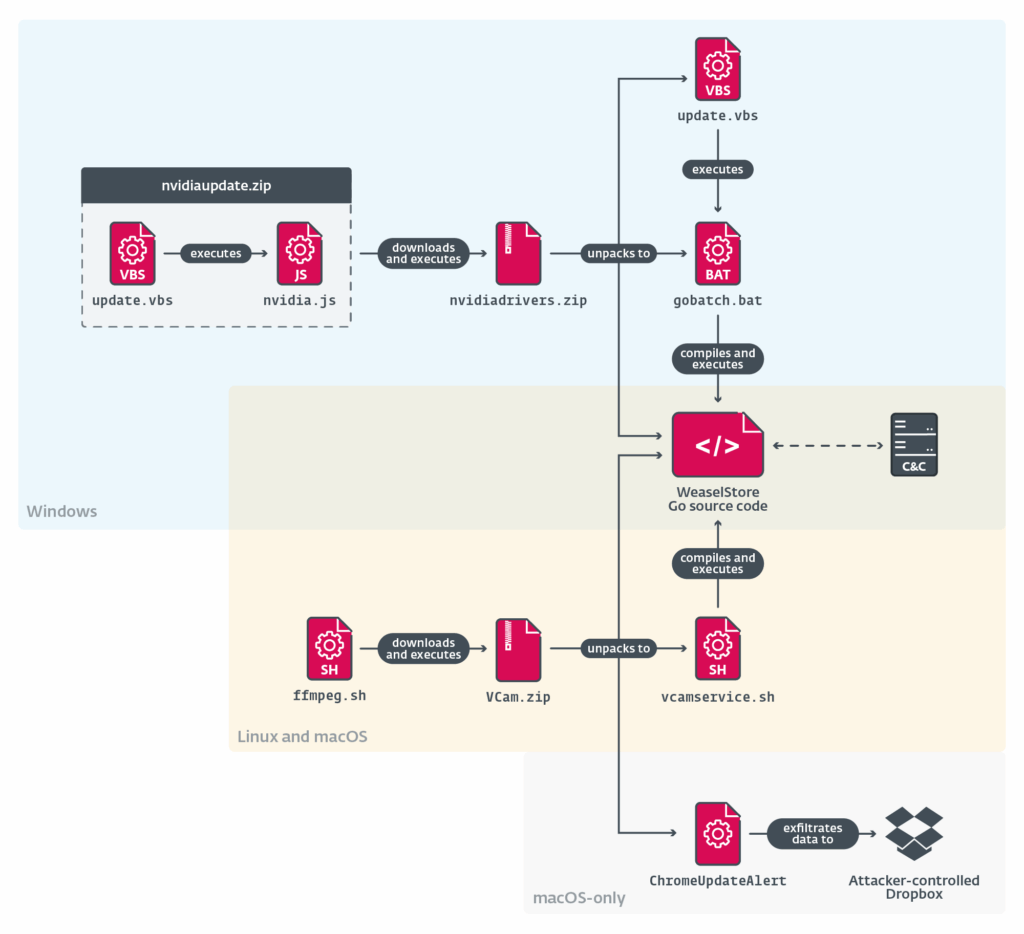
These methods deliver multiple malware families, including BeaverTail, InvisibleFerret, OtterCookie, GolangGhost (FlexibleFerret or WeaselStore), and PylangGhost. Among them, WeaselStore is particularly dangerous, as it not only steals sensitive browser and cryptocurrency wallet data but also functions as a remote access trojan (RAT).
<–image import–01image–>
Malware Arsenal: TsunamiKit and Tropidoor
ESET’s findings show that TsunamiKit and Tropidoor are commonly deployed in these attacks.
- TsunamiKit: First identified in November 2024, it includes several components such as TsunamiLoader, TsunamiInjector, and TsunamiHardener. It installs spyware, sets persistence, and even deploys cryptocurrency miners like XMRig and NBMiner. Evidence suggests it is adapted from existing dark web projects dating back to 2021.
- Tropidoor: A sophisticated malware overlapping with tools from the Lazarus Group. It has been discovered in multiple countries, including Kenya, Colombia, and Canada, and is capable of extensive system manipulation, stealth commands, and surveillance.
Emergence of AkdoorTea
The newest weapon, AkdoorTea, is delivered through a Windows batch script disguised as an NVIDIA driver update. The script downloads a ZIP file (nvidiaRelease.zip) containing payloads that activate both BeaverTail and AkdoorTea. The malware shares characteristics with Akdoor, a variant of the NukeSped (Manuscrypt) implant, further linking the group to the Lazarus Group umbrella.
ESET researchers note that while the tools may not always be technically advanced, the attackers excel at scaling operations, reusing dark web malware, and exploiting human trust through creative social engineering techniques.
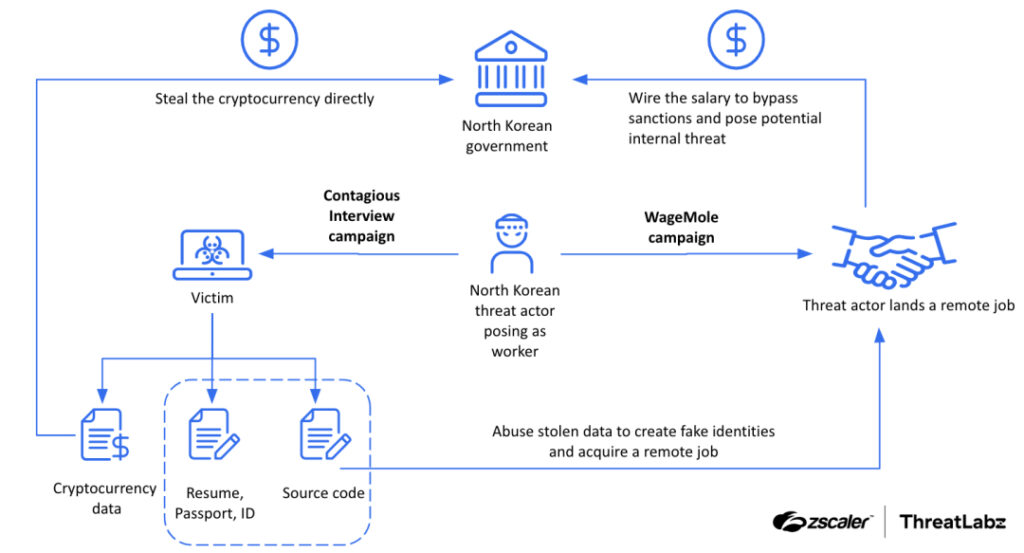
Overlap with North Korean IT Worker Fraud
The Contagious Interview campaign also aligns with North Korea’s fraudulent IT worker scheme, known as WageMole. Intelligence from these cyber campaigns is reportedly leveraged to secure legitimate employment for North Korean operatives, who then funnel profits and intelligence back to Pyongyang.
A recent case uncovered by Trellix highlighted an operative applying for a Principal Software Engineer role at a U.S. healthcare company under the alias Kyle Lankford. Although the applicant appeared legitimate, deeper investigation revealed strong ties to North Korea’s IT worker network.
Conclusion
The use of AkdoorTea reinforces how North Korean groups continue to evolve their methods, blending malware development, open-source tool adaptation, and large-scale social engineering campaigns. This hybrid model, combining cybercrime with fraudulent employment, represents an ongoing global security threat that targets both organizations and individuals.


