A persistent North Korean cyber campaign, known as Operation Dream Job, has resurfaced with a focused wave of attacks against European companies in the defense and aerospace sectors. ESET researchers Peter Kálnai and Alexis Rapin report the activity appears aimed at harvesting proprietary data and manufacturing know-how, especially tied to unmanned aerial vehicle, UAV, development.
Attack overview
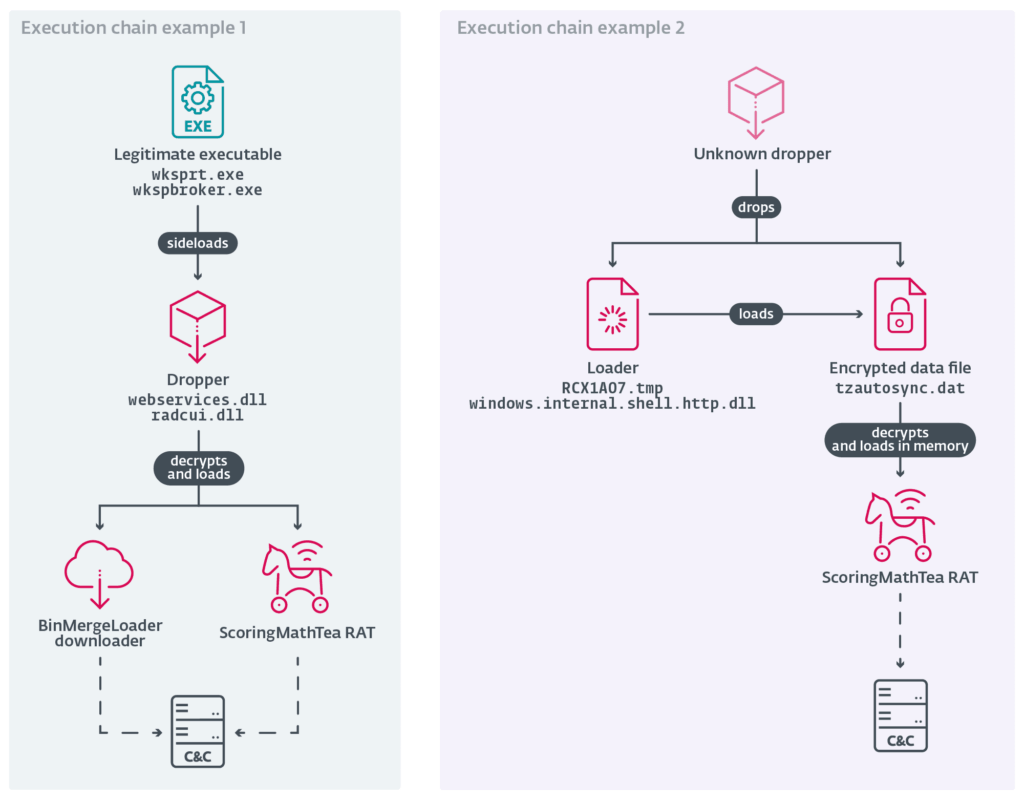
The campaign uses sophisticated social engineering, offering fake, lucrative job opportunities to entice engineers and employees. Targets receive a decoy job description, accompanied by a trojanized PDF reader or similar application, which when opened, launches an infection chain. The attackers then execute a binary that sideloads a malicious DLL, ultimately delivering the ScoringMathTea remote access trojan, and a downloader called BinMergeLoader that retrieves further payloads via Microsoft Graph API and access tokens.
Malware and history
ScoringMathTea, also tracked as ForestTiger, has been linked to prior Lazarus activity as early as October 2022, and resurfaced in attacks observed in early 2023. MISTPEN, first documented by Google Mandiant in September 2024, has been associated with intrusions against energy and aerospace firms. ESET observed this particular wave beginning in late March 2025, noting overlaps with other clusters and campaigns, including Contagious Interview, DeathNote, NukeSped, Operation In(ter)ception, and Operation North Star.
Targets and impact
Documented targets include a metal engineering firm in Southeastern Europe, an aircraft component manufacturer in Central Europe, and a defense company in Central Europe. The attackers aim to plunder intellectual property and manufacturing processes, which could accelerate efforts to expand North Korea’s drone program, according to ESET. ScoringMathTea is capable of around 40 commands, enabling full control of compromised systems, data exfiltration, and persistence.
Tactics and persistence
Lazarus Group, the threat actor attributed to Operation Dream Job, is a prolific North Korean-linked group, tracked under many names including APT-Q-1, Black Artemis, Diamond Sleet, Hidden Cobra, TEMP.Hermit, and UNC2970, and active since at least 2009. The group uses predictable, repeatable methods, such as trojanizing open-source applications and delivering polymorphic payloads, which help evade detection while still enabling attribution.


