A China linked cyber espionage group tracked as Lotus Blossom has been attributed with medium confidence to the recent compromise of infrastructure used to host the Notepad++ project. The attribution comes from new technical findings released by cybersecurity firm Rapid7.
According to the investigation, the intrusion allowed the state sponsored threat actor to deliver a previously undocumented backdoor named Chrysalis to a limited number of Notepad++ users. The activity appears to be part of a targeted campaign rather than a widespread attack.
The disclosure follows earlier statements from Notepad++ maintainer Don Ho, who confirmed that attackers compromised the hosting provider’s environment, enabling them to intercept and redirect update traffic starting in June 2025. The redirections selectively affected specific users and delivered tampered update files by abusing weak update verification mechanisms present in older versions of the software.
The vulnerability was addressed in December 2025 with the release of Notepad++ version 8.8.9. Further investigation revealed that the hosting provider remained compromised until December 2, 2025, when attacker access was finally revoked. Since then, Notepad++ has migrated to a new hosting provider, strengthened its security controls, and rotated all credentials.
Rapid7’s analysis did not uncover evidence that the official updater mechanism itself was directly abused to distribute malware at scale. Instead, researchers observed a specific execution chain in affected environments.
Security researcher Ivan Feigl noted that execution of notepad++.exe, followed by GUP.exe, preceded the launch of a suspicious binary named update.exe, which was downloaded from the IP address 95.179.213.0.
The file update.exe was identified as a Nullsoft Scriptable Install System installer containing several components. These included an NSIS installation script, a renamed Bitdefender Submission Wizard binary called BluetoothService.exe, encrypted shellcode referred to as Chrysalis, and a malicious DLL named log.dll. The legitimate executable was used to sideload the malicious DLL, a technique frequently associated with China aligned threat groups.
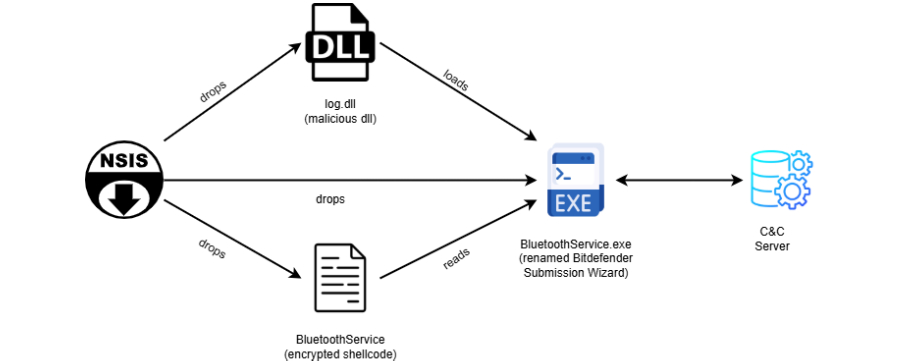
Chrysalis itself is described as a custom, feature rich implant capable of collecting detailed system information. It communicates with an external server at api.skycloudcenter[.]com to receive commands. Although the command and control server is currently offline, analysis of the obfuscated payload indicates advanced capabilities.
The backdoor can process HTTP responses to launch an interactive shell, create and manage processes, perform file operations, upload and download data, and remove itself from infected systems.
Rapid7 also identified a file named conf.c, designed to retrieve a Cobalt Strike beacon using a custom loader that embeds Metasploit block API shellcode. Another loader, ConsoleApplication2.exe, stands out for leveraging Microsoft Warbird, an undocumented internal code protection and obfuscation framework, to execute shellcode.
Researchers found that the threat actor adapted an existing proof of concept published by German cybersecurity firm Cirosec in September 2024, modifying it for operational use.
Based on infrastructure, tooling, and tradecraft overlaps, Rapid7 attributed Chrysalis to the Lotus Blossom threat group, also known as Billbug, Bronze Elgin, Raspberry Typhoon, Spring Dragon, and Thrip. The attribution aligns with previous campaigns, including activity documented by Symantec in April 2025 that involved DLL sideloading through legitimate Trend Micro and Bitdefender executables.
Rapid7 emphasized that while the group continues to rely on established techniques such as DLL sideloading and persistent services, the use of layered shellcode loaders and undocumented system calls like NtQuerySystemInformation signals a move toward more stealthy and resilient operations.
The combination of custom malware, commodity frameworks such as Metasploit and Cobalt Strike, and rapid adoption of public research highlights how Lotus Blossom is actively evolving its tactics to evade modern detection mechanisms.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


