Cybersecurity researchers have uncovered several malicious packages in the npm, Python (PyPI), and RubyGems ecosystems that are exfiltrating sensitive developer data using Discord webhooks as their command-and-control (C2) channels. These compromised packages allow attackers to send stolen information directly to Discord channels they control.
Discord Webhooks Used as a Stealthy Data Channel
Discord webhooks provide a way to post messages to specific channels without authentication or a bot user, making them a convenient method for threat actors. This mechanism allows attackers to transmit sensitive data such as API keys, configuration files, and environment variables directly to a remote server controlled via Discord.
According to Socket researcher Olivia Brown, “Webhook URLs are effectively write-only. They don’t reveal previous messages, and defenders cannot access channel history just by knowing the URL.”
This limitation gives cybercriminals an advantage, as defenders cannot easily review the data being sent or monitor webhook misuse.
Identified Malicious Packages
Security researchers identified multiple packages across different ecosystems that abuse Discord webhooks in distinct ways:
- mysql-dumpdiscord (npm): Extracts the contents of developer configuration files like config.json, .env, ayarlar.js, and ayarlar.json and sends them to a Discord webhook.
- nodejs.discord (npm): Uses a webhook for logging purposes, which is not inherently malicious but could be abused.
- malinssx, malicus, and maliinn (PyPI): Trigger HTTP requests to Discord channels every time they are installed via pip install, effectively using Discord as a C2 server.
- sqlcommenter_rails (RubyGems): Collects host system data and sensitive files such as /etc/passwd and /etc/resolv.conf and forwards them to a hardcoded Discord webhook.
Olivia Brown emphasized that Discord’s webhook abuse is changing the landscape of software supply chain attacks. Since the service is free, fast, and easy to integrate, attackers can avoid maintaining their own infrastructure. Moreover, the malicious code often blends with legitimate traffic, making detection by firewalls or security tools more difficult.
North Korean Campaign Floods npm With Fake Packages
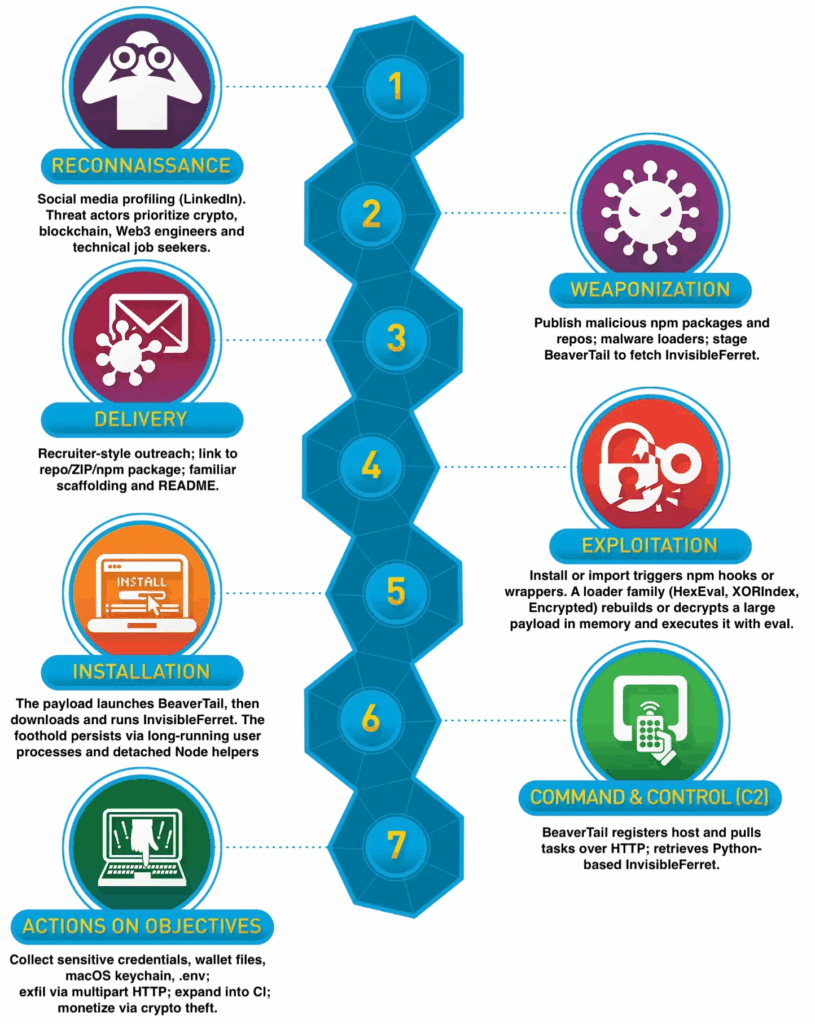
In a related disclosure, researchers revealed that North Korean threat actors linked to the Contagious Interview campaign published over 338 malicious npm packages. These packages were used to deliver malware families such as HexEval, XORIndex, and BeaverTail, collectively surpassing 50,000 downloads.
Security researcher Kirill Boychenko explained that attackers used over 180 fake personas and multiple C2 endpoints to disguise their activity. Their primary targets were Web3, blockchain, and cryptocurrency developers, as well as technical job seekers. Victims were often contacted via LinkedIn and encouraged to complete coding assignments by cloning repositories containing booby-trapped npm packages like eslint-detector.
Once executed, these malicious packages operated as stealers, gathering browser credentials, cryptocurrency wallet data, macOS Keychain information, keystrokes, clipboard contents, and screenshots. The malware also deployed a cross-platform Python backdoor called InvisibleFerret for further exploitation.
Persistent Supply Chain Threat
Many of these malicious packages were found to be typosquats of legitimate ones, such as dotevn instead of dotenv or ethrs.js instead of ethers.js, particularly targeting Node.js, Express, and React developers.
Boychenko highlighted that Contagious Interview is a state-sponsored, factory-style operation, not a small cybercrime project. “It operates like a production line with assigned quotas and long-term resourcing,” he said. “Removing individual packages is not enough unless the associated publisher accounts are deactivated.”
The campaign demonstrates that the npm ecosystem remains a preferred initial access vector for persistent and organized cyber operations.


