A sophisticated cyber espionage campaign, dubbed Operation SkyCloak, is using weaponized phishing emails to deploy a highly stealthy backdoor on target systems. The malware establishes persistent remote access by combining a customized OpenSSH server with a Tor hidden service, creating a covert channel that is extremely difficult to trace.
The Lure: Phishing with Military Documents
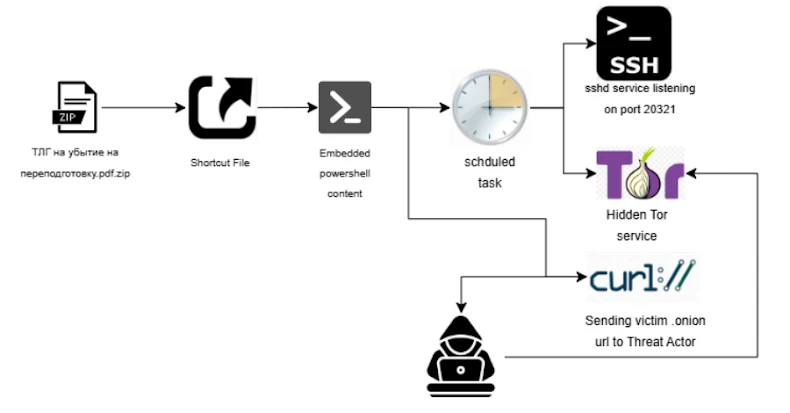
The attack begins with targeted phishing emails containing lures related to military documents. These emails trick recipients into opening a malicious ZIP file attachment. Inside the archive, victims find:
- A Windows Shortcut (LNK) file.
- A hidden folder containing a second, nested archive file.
This structure is deliberately designed to bypass automated security scanners and encourage manual execution by the user.
A Multi-Stage and Evasive Infection Chain
When the victim double-clicks the LNK file, it triggers a multi-stage infection process:
- PowerShell Dropper: The LNK file executes PowerShell commands that act as the initial dropper.
- Anti-Analysis Checks: An intermediate PowerShell module performs critical environmental checks to avoid sandbox detection. It verifies:
- At least 10 recently used LNK files exist on the system.
- The number of running processes is 50 or higher.
These conditions are typical of a real user’s workstation but rare in sterile analysis environments. If the checks fail, the malware aborts.
- Decoy and Persistence: If the checks pass, the script opens a decoy PDF document to maintain the illusion of legitimacy. Simultaneously, it establishes persistence by creating a scheduled task named
githubdesktopMaintenance. This task is configured to run at user logon and daily at 10:21 AM UTC.
The Core Payload: OpenSSH and Tor for Covert Control
The scheduled task launches the core backdoor components from a dedicated directory (C:\Users\<Username>\AppData\Roaming\logicpro\).
The backdoor consists of two main parts:
- OpenSSH Backdoor (
githubdesktop.exe): This is a renamed, legitimatesshd.exe(OpenSSH for Windows) binary. It runs an SSH server on the victim’s machine, configured to only accept connections from cryptographic keys that the attacker pre-placed in thelogicprofolder. This provides secure, authenticated remote access. - Tor Hidden Service (
pinterest.exe): This is a customized Tor client binary. It creates a hidden service (onion service) using obfs4 obfuscation to disguise its traffic, making it look like random internet data. This service acts as a relay, allowing the attacker to connect to the internal SSH server from anywhere in the world without revealing their own IP address.

The malware also sets up port forwarding for critical services like RDP, SSH, and SMB, giving the attacker comprehensive control over the system and its resources through the anonymous Tor network.
Exfiltration and Full System Takeover
Once the Tor hidden service is active, the malware executes a final step:
- It collects system information and a unique .onion URL that identifies the compromised host.
- It exfiltrates this data to the attacker’s command-and-control server using a
curlcommand.
Upon receiving this data, the threat actor gains the information needed to establish a full, anonymous remote connection to the victim’s machine via the Tor network, achieving complete and untraceable control.
Attribution and Connection to Known Threats
While definitive attribution is not available, the tactics and targets point to Eastern European cyber espionage groups. Cybersecurity firm Cyble has assessed with medium confidence that the campaign shares overlaps with UAC-0125, a threat actor previously tracked by Ukraine’s CERT for targeting defense and government sectors.
“Attackers access SSH, RDP, SFTP, and SMB via concealed Tor services, enabling full system control while preserving anonymity,” Cyble noted.


