Over 1,000 N-able N-central Servers Exposed to Critical Zero-Day Vulnerabilities
More than 1,000 exposed and unpatched N-able N-central Remote Monitoring and Management (RMM) servers are at risk due to two newly identified zero-day vulnerabilities (CVE-2025-8875 and CVE-2025-8876).
According to data confirmed on August 15, 2025, 1,077 unique IPs were detected running outdated N-central versions. This presents a major security risk for managed service providers (MSPs) and their clients.
Both flaws have now been added to the CISA Known Exploited Vulnerabilities (KEV) catalog, highlighting their critical severity.
Key Insights
1. 1,077 vulnerable N-central RMM servers exposed to CVE-2025-8875 and CVE-2025-8876.
2. Classified as Remote Code Execution (RCE) flaws, these issues can allow attackers to gain control of MSP environments.
3. Immediate patching to version 2025.3.1 is required.Geographic Distribution of Affected Servers
Research by the Shadowserver Foundation shows that most unpatched servers are concentrated in:
- United States: 440 IPs
- Canada: 112 IPs
- Netherlands: 110 IPs
- United Kingdom: 98 IPs
- Additional exposures were also found in Australia and South Africa.
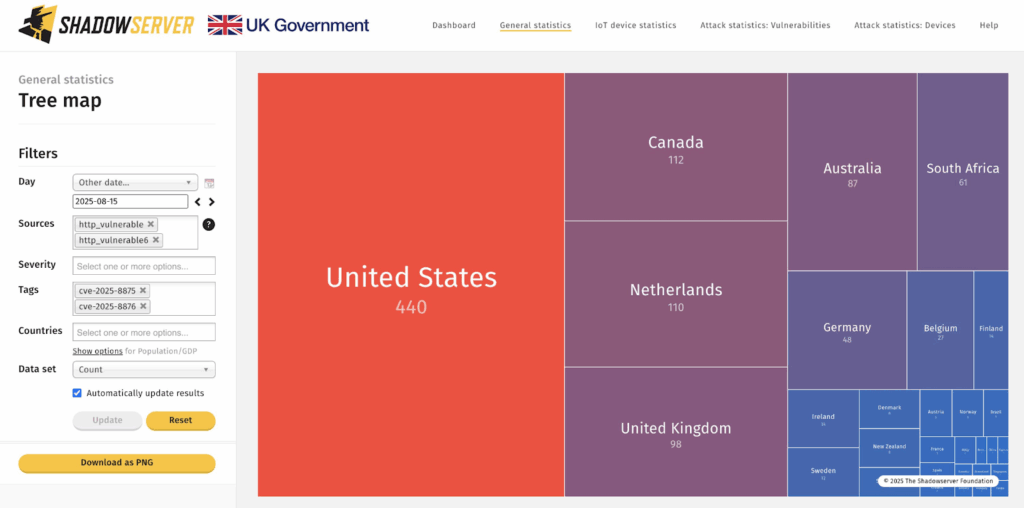
Top Affected countries
Understanding the N-able N-central Vulnerabilities
The two vulnerabilities target HTTP-accessible N-central deployments and remain exploitable until administrators apply the 2025.3.1 security patch.
Both CVE-2025-8875 and CVE-2025-8876 are authentication-required RCE vulnerabilities. While authentication provides some initial barrier, threat actors who steal or phish credentials can exploit these flaws to:
- Execute arbitrary commands
- Escalate privileges
- Move laterally within MSP-managed environments
N-able strongly advises administrators:
“Upgrade on-premises N-central to 2025.3.1 immediately. Full technical details of the CVEs will be released three weeks post-update, as part of our standard security disclosure process.”
What the Update Provides
The 2025.3.1 patch not only fixes these vulnerabilities but also introduces:
- Audit Logging Enhancements: Tracks critical events such as SSH logins, scheduled task edits, and script deletions.
- Syslog Export Support for improved compliance and monitoring.
Configuration Example
Navigate to Administration > Audit > Configure Syslog Export
Set Syslog Server IP and Port
Select relevant events (e.g., SSH Login, Script Created)
Enable automatic exportImproved Device Management API
The update also strengthens automation capabilities within N-central’s Device Management API:
POST /api/device enables bulk onboarding of endpoints.
GET /api/device/[deviceid}/asset retrieves application details.These enhancements allow defenders to better monitor user activity and accelerate endpoint onboarding, but require timely patching to ensure security.
Immediate Action Required
MSPs running outdated versions must immediately review any Shadowserver alerts for compromise and apply the official N-able 2025.3.1 update without delay.


