More than 900 internet facing FreePBX systems from Sangoma Technologies remain compromised with web shells following exploitation of a serious command injection vulnerability, according to findings released by Shadowserver Foundation.
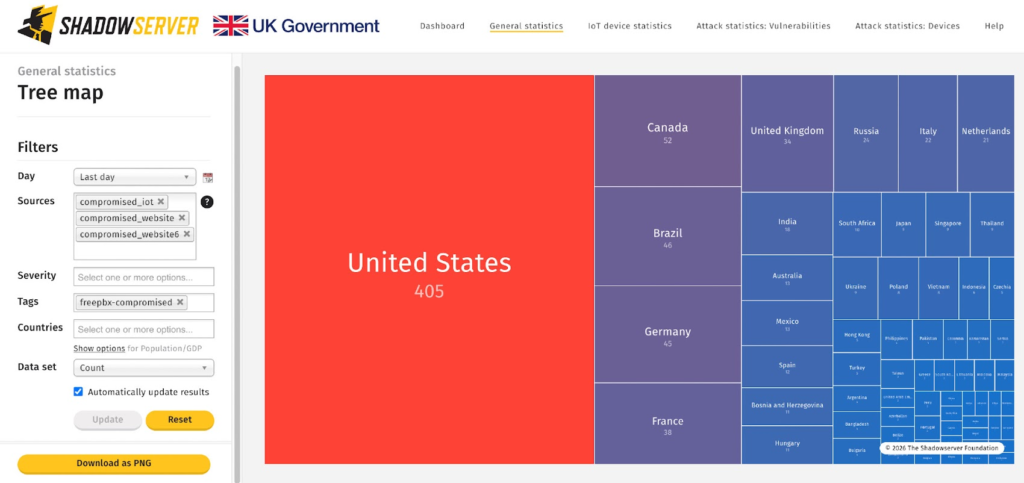
The large scale compromise began in December 2025 and continues to impact organizations worldwide. Of the affected instances, 401 are located in the United States, 51 in Brazil, 43 in Canada, 40 in Germany, and 36 in France, indicating widespread global exposure.
Vulnerability Behind the Breach
The attacks are believed to exploit CVE 2025 64328, a high severity flaw with a CVSS score of 8.6. The vulnerability enables post authentication command injection, allowing authenticated users with administrative panel access to execute arbitrary shell commands on the underlying host system.
According to FreePBX advisories released in November 2025, any user with access to the Administrator Control Panel could potentially leverage the flaw to gain remote shell access under the asterisk user account. Such access provides attackers with significant control over PBX operations and the host server.
The issue affects FreePBX versions 17.0.2.36 and later. It was patched in version 17.0.3, and administrators were urged to upgrade immediately.
Active Exploitation and Web Shell Deployment
The vulnerability has since been actively exploited in real world attacks. Earlier this month, Cybersecurity and Infrastructure Security Agency (CISA) added the flaw to its Known Exploited Vulnerabilities catalog, highlighting the urgency of remediation.
In a separate analysis published by Fortinet FortiGuard Labs, researchers linked the exploitation to a cyber fraud campaign tracked as INJ3CTOR3. Threat actors reportedly began abusing the vulnerability in early December 2025 to deploy a malicious web shell dubbed EncystPHP.
By leveraging administrative contexts within Elastix and FreePBX environments, the web shell operates with elevated privileges. This enables attackers to execute commands remotely, manipulate PBX configurations, and in some cases initiate outbound call activity directly through compromised systems.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


