A cyber threat group identified as Storm-2657 has been observed taking over employee accounts with the intent of redirecting salary payments to attacker-controlled bank accounts.
According to a report from the Microsoft Threat Intelligence team, “Storm-2657 is actively targeting various U.S.-based organizations, especially employees in sectors such as higher education, to infiltrate third-party Human Resources (HR) Software-as-a-Service (SaaS) platforms like Workday.”
However, Microsoft warned that this threat is not limited to Workday. Any SaaS platform handling HR, payroll, or banking details could become a target for similar financially driven attacks. This campaign, codenamed Payroll Pirates, has also been analyzed by cybersecurity firms such as Silent Push, Malwarebytes, and Hunt.io.
How the Attack Works
What makes these incidents alarming is that the attackers are not exploiting software vulnerabilities. Instead, they rely on social engineering and the absence of multi-factor authentication (MFA) to gain access. Once inside, they modify employee payment details to reroute funds to their own accounts.
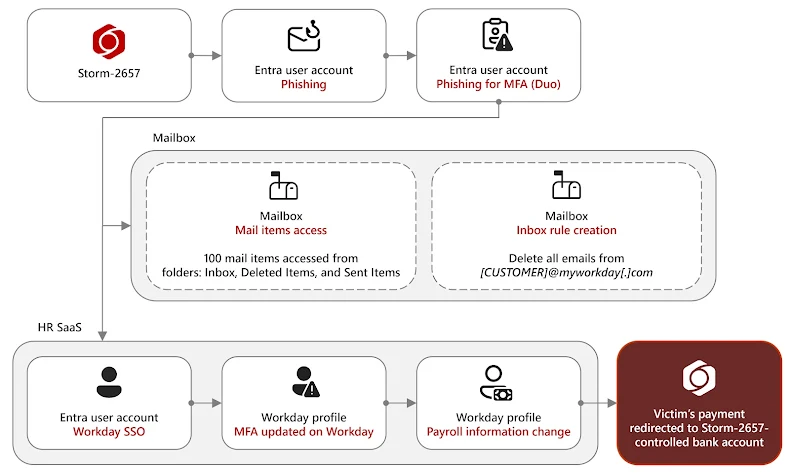
In one campaign detected by Microsoft during the first half of 2025, the attackers used phishing emails to steal employee credentials and MFA codes. The phishing messages contained adversary-in-the-middle (AitM) links designed to capture authentication data. Through this method, the attackers were able to access Exchange Online accounts and compromise Workday profiles via single sign-on (SSO).
Persistence and Evasion Tactics
After breaching the accounts, the attackers set up email inbox rules that automatically delete alert messages from Workday. This helps conceal unauthorized profile modifications, including salary redirections to attacker-controlled bank accounts.
To maintain ongoing access, the intruders also register their own phone numbers as MFA devices for the compromised accounts. In addition, these hijacked email accounts are used to spread phishing campaigns both internally and to other organizations.
Since March 2025, Microsoft has identified 11 compromised accounts across three U.S. universities. These accounts were leveraged to send nearly 6,000 phishing emails targeting staff and students at 25 different universities. The lures often referenced illness or misconduct notices, creating a false sense of urgency and prompting victims to click on malicious links.
Security Recommendations
To defend against Storm-2657 (Payroll Pirates), Microsoft recommends the following measures:
- Implement phishing-resistant MFA or passwordless authentication, such as FIDO2 security keys.
- Regularly audit accounts for suspicious indicators like unfamiliar MFA devices, unrecognized inbox rules, or unauthorized account changes.
- Educate employees about phishing awareness and enforce strong access control policies.
By strengthening MFA and monitoring unusual account behavior, organizations can significantly reduce the risk of payroll diversion attacks.


