Over the past two and a half years, a China-linked, state-aligned cyber espionage group, known as Phantom Taurus, has been observed targeting government and telecommunications organizations across Africa, the Middle East, and Asia. The group focuses on intelligence collection, aiming to obtain sensitive diplomatic and defense-related data, often aligning its operations with major geopolitical events and regional security developments.
Who is Phantom Taurus, and what do they target?
Security researchers at Palo Alto Networks Unit 42 attribute a persistent, stealthy campaign to Phantom Taurus, which pursues long-term data collection from ministries of foreign affairs, embassies, actors involved in geopolitical events, and military-related organizations. According to Unit 42, the group’s objective is primarily espionage, shown by targeted intrusions, long-term persistence, and rapid adaptation of tactics, techniques, and procedures, TTPs.
Unit 42 first discussed this cluster in June 2023 under the tracking name CL-STA-0043, and later upgraded the classification as their monitoring revealed sustained operations affecting government entities since late 2022, part of what they called Operation Diplomatic Specter. Continued monitoring provided enough evidence to treat Phantom Taurus as a distinct threat actor focused on strategic intelligence collection tied to Chinese interests, both economic and geopolitical.
Timing, targets, and geopolitical context
Phantom Taurus frequently times its activity to coincide with high-profile diplomatic or security events. This behavior mirrors other China-associated groups, such as the adversary tracked by Recorded Future as RedNovember, which reportedly targeted entities in Taiwan and Panama around key geopolitical moments. The alignment of malware campaigns with real-world events suggests the actor seeks timely intelligence that supports national strategic goals.
Unique tooling, and NET-STAR
What sets Phantom Taurus apart is its use of bespoke tooling and novel techniques. Unit 42 identified a .NET-based malware suite, NET-STAR, specifically engineered to compromise Internet Information Services, IIS, web servers. NET-STAR includes multiple web-based backdoors designed to maintain stealthy, persistent access to compromised IIS environments.
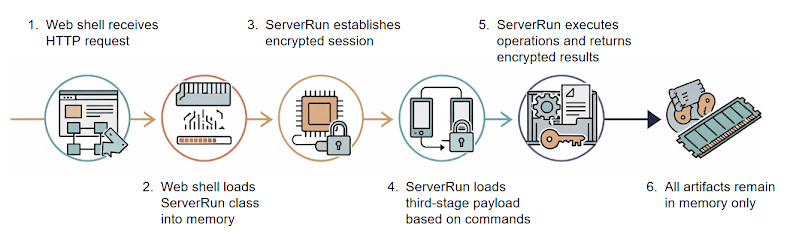
NET-STAR’s components include, but are not limited to, the following,
- IIServerCore, a fileless, modular backdoor loaded through an ASPX web shell, capable of executing in-memory commands and payloads, returning results over an encrypted command-and-control, C2, channel,
- AssemblyExecuter V1, which loads and runs additional .NET payloads entirely in memory,
- AssemblyExecuter V2, an improved variant that adds capabilities to evade the Antimalware Scan Interface, AMSI, and Event Tracing for Windows, ETW.
IIServerCore also supports a changeLastModified command, indicating timestomping capabilities intended to hinder forensic analysis. This level of .NET-native, fileless sophistication demonstrates a deep understanding of .NET internals and server-side evasion techniques, posing a severe risk to internet-facing IIS servers.
Shared infrastructure, compartmentalization
Phantom Taurus has reused some operational infrastructure previously associated with groups like AT27 (Iron Taurus), APT41 (Winnti, Starchy Taurus), and Mustang Panda (Stately Taurus). However, analysts note that many infrastructure elements are unique to Phantom Taurus operations, indicating operational compartmentalization inside a shared ecosystem. This mixed use of shared and exclusive infrastructure complicates attribution and defensive measures.
Initial access and exploitation methods
While the precise initial access vector varies, prior intrusions by Phantom Taurus weaponized vulnerable on-premises IIS and Microsoft Exchange servers. Observed exploitation included known flaws such as ProxyLogon and ProxyShell, long-used by other sophisticated actors to gain footholds in enterprise networks. Security researchers emphasize that although current intrusions leverage these known vulnerabilities, the threat actor is resourceful and likely to adopt new vectors as defensive measures close existing gaps.
Shift from email harvesting to direct database targeting
A notable evolution in Phantom Taurus operations is the move from capturing email content to directly exfiltrating databases. The group has been observed using batch scripts that connect to Microsoft SQL Server instances, export query results to CSV files, and then close the connection. These scripts are executed through Windows Management Instrumentation (WMI) allowing for stealthy, automated extraction of targeted documents and country-specific intelligence, including material related to Afghanistan and Pakistan.
Operational impact, recommendations
The combination of bespoke server-side backdoors, fileless execution, timestomping, and direct database targeting makes Phantom Taurus a significant espionage threat for governments and telecommunications providers. Organizations that operate internet-facing IIS or Exchange servers, and those involved in diplomacy or defense, should assume heightened risk and take the following steps,
- Patch and harden, prioritize applying vendor fixes for ProxyLogon, ProxyShell, and other known server vulnerabilities immediately,
- Monitor for abnormal WMI activity and large, unexpected SQL exports, especially CSV file generation and off-hour connections,
- Inspect IIS logs for signs of ASPX web shells, in-memory payload execution, and unusual changes to file modification timestamps,
- Enable endpoint telemetry that can detect AMSI and ETW bypass attempts, and enrich detection rules to capture AssemblyExecuter-like behaviors,
- Segment critical database servers and apply strict access controls, least privilege, and multi-factor authentication for administrative access,
- Exercise proactive threat hunting around diplomatic email stores and databases, looking for indicators of long-term, low-noise exfiltration.