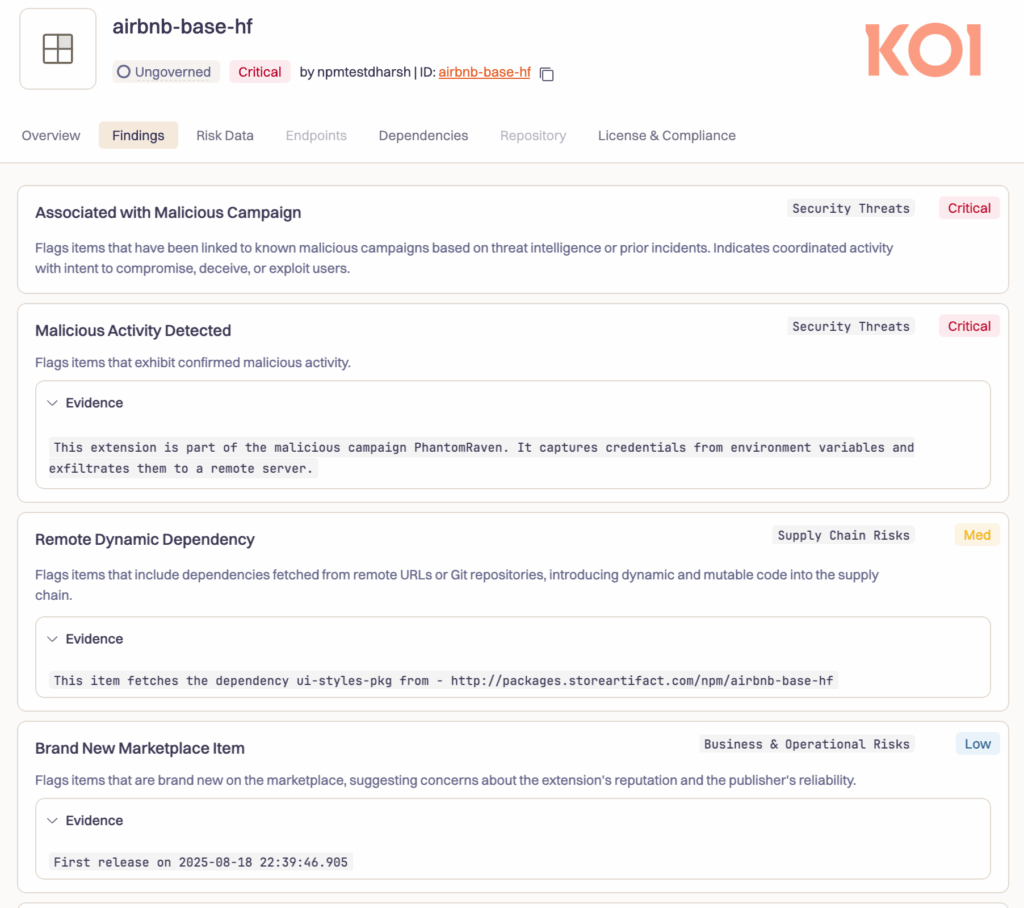
A sophisticated software supply chain attack, dubbed “PhantomRaven,” has infiltrated the npm registry with 126 malicious packages designed to secretly steal sensitive developer credentials. This campaign specifically targets authentication tokens, CI/CD secrets, and GitHub credentials directly from developers’ machines, posing a severe threat to software development integrity.
The Scale and Stealth of the PhantomRaven Campaign
Discovered by Koi Security, this malicious activity is believed to have commenced in August 2025. It has since expanded dramatically, with the malicious libraries collectively accumulating over 86,000 installations. Several of these packages were also identified by the DevSecOps firm DCODX, including:
op-cli-installer(486 Downloads)unused-imports(1,350 Downloads)badgekit-api-client(483 Downloads)polyfill-corejs3(475 Downloads)eslint-comments(936 Downloads)
The Core Deception: Remote Dynamic Dependencies (RDD)
The attack’s ingenuity lies in its method of hiding malicious code. Instead of bundling the harmful payload directly within the package, the attacker points the package’s dependency to a custom, external HTTP URL (packages.storeartifact[.]com).
This means that every time a developer installs one of these packages, npm fetches the dependency from this untrusted, attacker-controlled server instead of the official npmjs[.]com registry.
“As npmjs[.]com doesn’t follow those URLs, automated security systems are effectively blinded,” explained Oren Yomtov, a security researcher at Koi Security. “Security scanners don’t fetch them. Dependency analysis tools ignore them. To every automated security system, these packages deceptively show ‘0 Dependencies.'”
A Dynamic and Evolving Threat
The use of a remote, attacker-controlled server makes the threat highly adaptive. The attacker can:
- Tailor Payloads: Serve specific malware based on the victim’s environment.
- Gain Trust: Initially deliver harmless code to avoid detection, only pushing the malicious payload after the package has gained widespread adoption and trust.
- Remain Stealthy: Change the payload at any time without needing to update the package on the npm registry.
The Attack Chain: From Installation to Data Theft
The compromise begins the moment a developer installs a seemingly harmless package. The attack unfolds automatically through a pre-configured preinstall hook.
- Installation: A developer runs
npm installon a malicious package. - Trigger: The
preinstallhook automatically executes. - Payload Retrieval: The hook fetches the remote dynamic dependency from the malicious server.
- Data Harvesting: The delivered payload scans the developer’s system to:
- Collect email addresses and GitHub tokens.
- Gather information about the CI/CD environment.
- Create a system fingerprint, including the public IP address.
- Exfiltration: All stolen data is sent to a remote command-and-control server.
Exploiting AI Hallucinations through “Slopsquatting”
The attacker strategically selected package names to maximize their success. They employed a technique called slopsquatting, which involves registering package names that large language models (LLMs) might “hallucinate” or generate—names that sound plausible and correct but don’t actually exist. This tricks developers who trust these AI-generated recommendations into installing the malicious package.
“PhantomRaven demonstrates how sophisticated attackers are getting better at exploiting blind spots in traditional security tooling,” Yomtov noted. “Remote Dynamic Dependencies aren’t visible to static analysis. AI hallucinations create plausible-sounding package names that developers trust. And lifecycle scripts execute automatically, without any user interaction.”