Cybersecurity experts have revealed a sophisticated dual-phase phishing campaign that uses stolen login credentials to install legitimate Remote Monitoring and Management (RMM) software, giving attackers long-term control over compromised systems.
According to researchers at KnowBe4 Threat Labs, Jeewan Singh Jalal, Prabhakaran Ravichandhiran, and Anand Bodke, attackers are now bypassing traditional security defenses by leveraging trusted IT tools rather than relying on custom malware. By obtaining a “skeleton key” to victim systems, they convert legitimate RMM platforms into persistent backdoors.
How the Attack Works
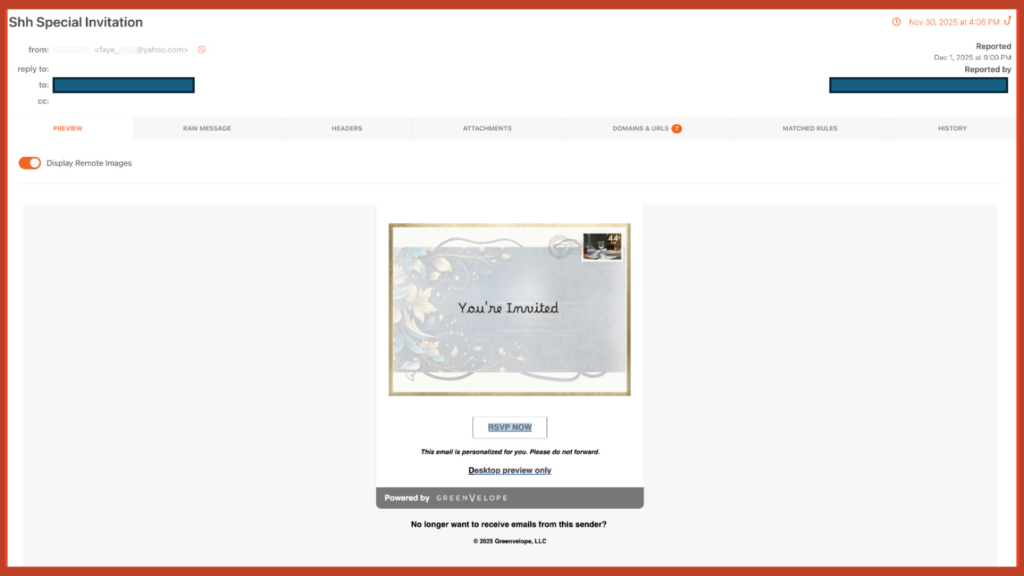
The operation occurs in two main stages. Initially, threat actors send fake invitation notifications that trick recipients into revealing their login credentials. The emails appear to come from a legitimate platform called Greenvelope and include phishing links designed to capture Microsoft Outlook, Yahoo!, and AOL.com account information.
Once credentials are stolen, attackers use them to register on LogMeIn, generating RMM access tokens. These tokens are then embedded in an executable named GreenVelopeCard.exe, which silently installs LogMeIn Resolve (formerly GoTo Resolve) on the target system.
The malicious binary, digitally signed with a valid certificate, contains a JSON configuration that connects to attacker-controlled servers without alerting the victim. With RMM access in place, attackers adjust service settings for unrestricted control on Windows devices and create hidden scheduled tasks to ensure the software persists even if terminated manually.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.