A highly advanced phishing campaign managed to stay undetected for more than three years while operating through Google Cloud and Cloudflare services. The attackers impersonated leading corporations, including major defense contractor Lockheed Martin, raising concerns about the detection gaps in two of the world’s most trusted internet infrastructure providers.
How the Campaign Worked
The operation started when cybercriminals purchased expired domains that once belonged to genuine organizations. These domains were then repurposed to host cloned websites of Fortune 500 companies. By targeting high-profile domains with established credibility and active social media presence, the attackers successfully deceived unsuspecting users.
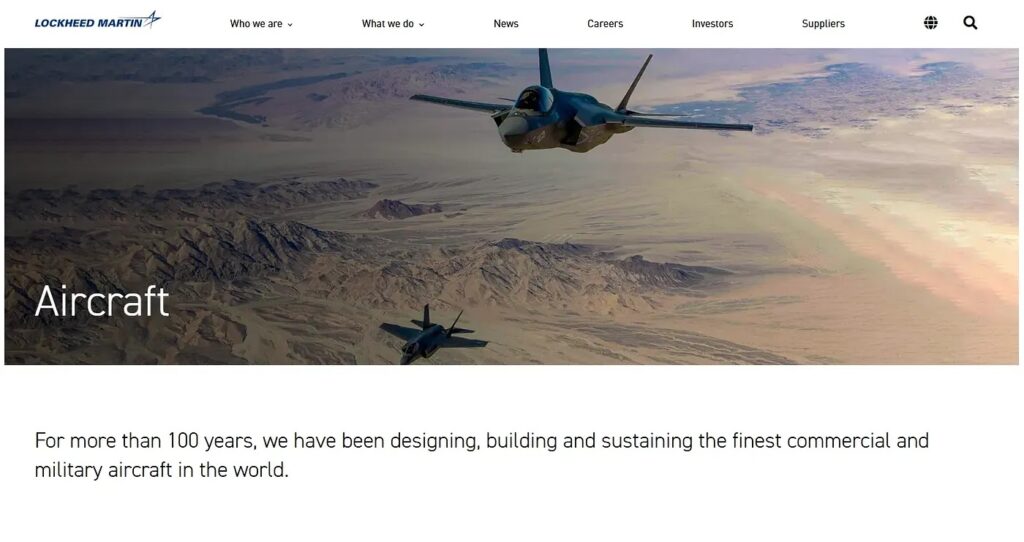
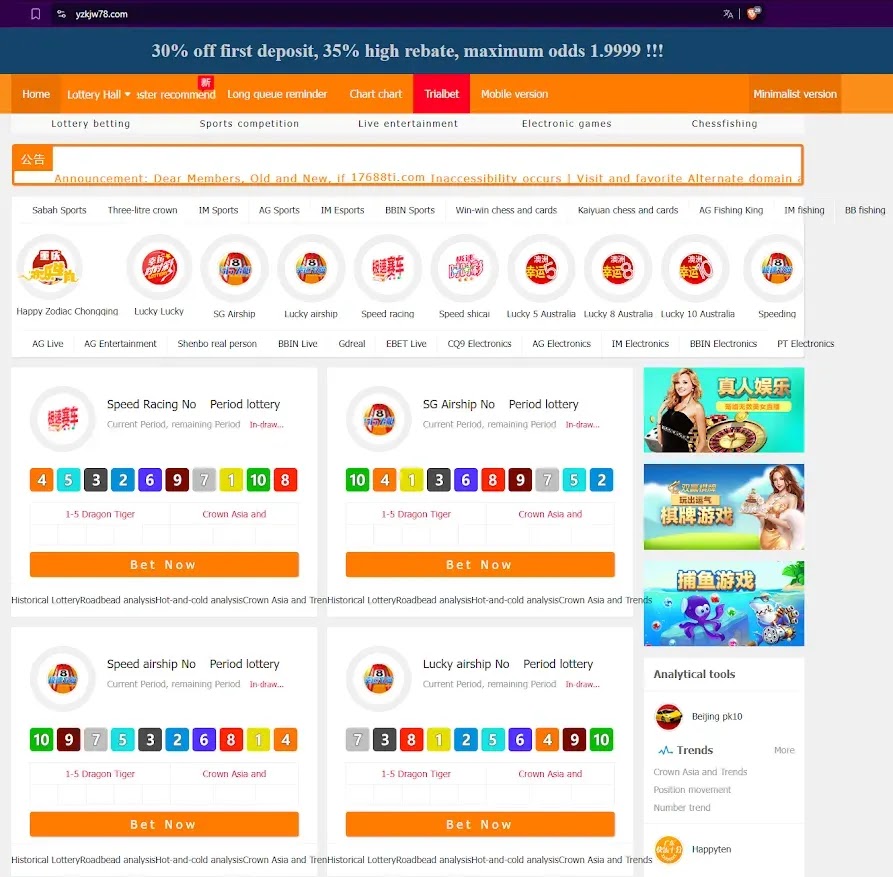
One striking case involved the domain militaryfighterjet.com. Originally created to share information about military aircraft, it was later turned into a gambling website while simultaneously functioning as a pixel-perfect clone of Lockheed Martin’s corporate site.
Cloaking Technology and Dual Content Delivery
The attackers relied on advanced cloaking methods to bypass detection. Depending on the visitor’s browser, device, or geographic location, the site would deliver different content.
- Search engine crawlers and automated scanners were shown convincing corporate website clones.
- Direct visitors using browsers were redirected to gambling platforms or malicious content.
This dual-purpose setup allowed the campaign to maintain high rankings in Google search results while quietly distributing illicit content and potential malware to real users.
Discovery by Deep Specter Research
Cybersecurity analysts at Deep Specter Research uncovered this large-scale operation while investigating the transformation of the militaryfighterjet.com domain. Their study revealed that the infrastructure involved:
- More than 48,000 active virtual hosts
- Spread across 86 distinct clusters
- Primarily hosted on Google Cloud platforms in Hong Kong and Taiwan
Evidence shows the campaign has been active since 2021, with rapid expansions observed during periods of global cybersecurity incidents and data breaches.
Technical Infrastructure and Methodology
The campaign’s technical depth highlights the professionalism of its operators. Investigators discovered that attackers used HTTrack Website Copier, a legitimate tool, to create pixel-perfect replicas of corporate websites. HTML comments even contained timestamps revealing when specific sites were copied.
The cloaking system analyzed:
- HTTP headers
- User agent strings
- IP geolocation data
This allowed the system to distinguish between genuine users, search engine bots, and security researchers, ensuring that malicious activity stayed hidden from automated detection systems.
Scale and Organization
The infrastructure showcased both resilience and scalability:
- Over 200 cloned brands spanning industries like defense, healthcare, and manufacturing
- The largest cluster alone hosted nearly 6,000 cloned sites of one organization
- Eight upper-tier management servers controlled 78 cluster managers, reflecting a hierarchical command structure seen in organized cybercriminal groups
By exploiting the trusted reputation of Google Cloud and Cloudflare, the attackers bypassed many security checks and maintained persistence across thousands of compromised domains.
Key Takeaways
This campaign exposes critical weaknesses in cloud-based security monitoring. Despite the reputation of Google and Cloudflare, cybercriminals successfully built and operated an expansive phishing infrastructure for over three years without being stopped.
The incident highlights the urgent need for:
- Stronger domain monitoring and vetting processes
- Improved detection of cloaking techniques
- Enhanced collaboration between cloud providers and cybersecurity researchers