Ukraine’s Computer Emergency Response Team (CERT-UA) has revealed details of a recent cyber espionage campaign targeting Ukrainian defense forces using a malware strain known as PLUGGYAPE. The attacks were observed between October and December 2025.
CERT-UA has attributed the activity with medium confidence to a Russia aligned threat group tracked as Void Blizzard, also known as Laundry Bear or UAC-0190. The group is believed to have been active since at least April 2024.
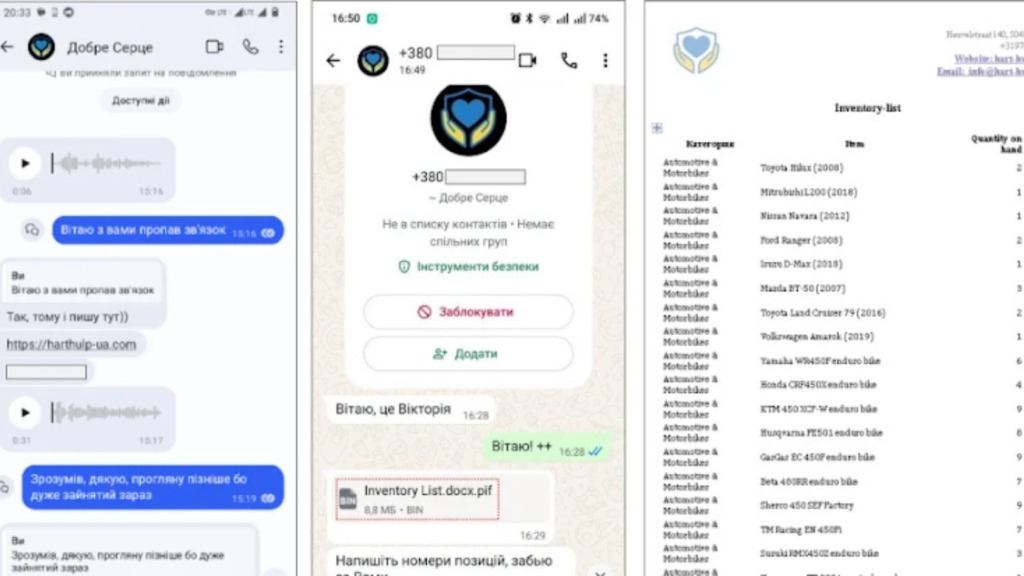
Messaging Apps Used as Initial Attack Vector
According to investigators, the attackers relied on popular instant messaging platforms, including Signal and WhatsApp, to initiate contact with victims. The threat actors impersonated charitable organizations and used social engineering techniques to persuade targets to click on seemingly legitimate links such as harthulp-ua[.]com and solidarity-help[.]org.
These websites mimicked humanitarian foundations and hosted password protected archives. Once downloaded and opened, the archives executed a malicious payload that led to the deployment of PLUGGYAPE.
Malware Delivery and Technical Capabilities
The malicious executable inside the archive was built using PyInstaller. CERT-UA noted that newer versions of the malware incorporate additional obfuscation and anti analysis mechanisms designed to prevent execution in virtualized or sandboxed environments.
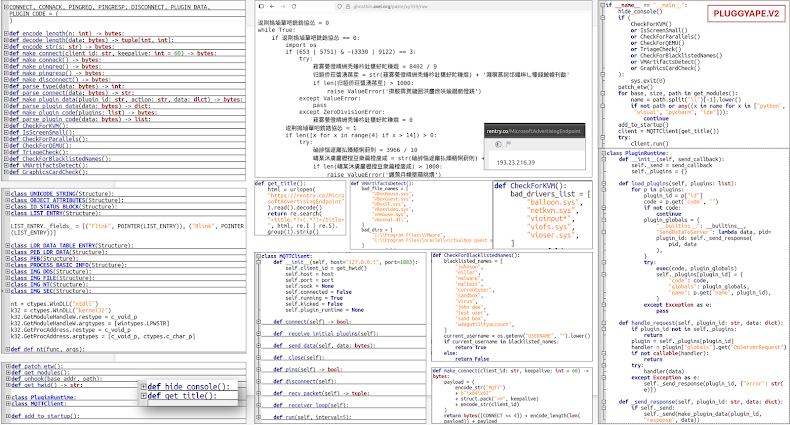
PLUGGYAPE is written in Python and establishes command and control communication using WebSocket or Message Queuing Telemetry Transport (MQTT). Support for MQTT based communication was introduced in December 2025, expanding the malware’s flexibility and resilience.
Rather than hard coding command and control servers, the malware retrieves C2 addresses from public paste services such as rentry[.]co and pastebin[.]com. These addresses are stored in Base64 encoded form, allowing attackers to rapidly update infrastructure if existing servers are disrupted or taken down.
This approach improves operational security and enables near real time infrastructure rotation.
Highly Targeted Social Engineering Tactics
CERT-UA emphasized that attackers increasingly rely on legitimate Ukrainian phone numbers and accounts when contacting targets. Communications are conducted in the Ukrainian language and may include voice and video calls. In some cases, attackers demonstrate detailed knowledge of the target’s role, organization, and internal operations.
The agency warned that widely used messaging applications on mobile devices and personal computers have become one of the most common channels for malware delivery in modern cyber attacks.
Related Campaigns Targeting Ukraine
In separate disclosures, CERT-UA highlighted additional threat activity targeting Ukrainian entities. A cluster tracked as UAC-0239 was observed sending phishing emails from UKR[.]net and Gmail accounts. These emails contained links or attachments to VHD files that delivered a Go based information stealer called FILEMESS, which collects specific file types and exfiltrates them to Telegram.
The same campaign also deployed an open source command and control framework known as OrcaC2, capable of system manipulation, file transfer, keylogging, and remote command execution.
Another threat group, UAC-0241, targeted Ukrainian educational institutions and government bodies using ZIP archives containing Windows shortcut files. Opening the shortcut triggered execution of an HTML Application via mshta.exe, which ultimately delivered the LaZagne password recovery tool and a Go backdoor known as GAMYBEAR. This backdoor supports remote command execution and data exfiltration over HTTP using Base64 encoding.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.