A major cyber incident has struck South Korea’s financial sector after a sophisticated supply chain attack enabled the deployment of Qilin ransomware. The intrusion unfolded through a compromised Managed Service Provider, allowing attackers to infiltrate multiple organizations simultaneously.
Cybersecurity company Bitdefender reported that this operation blended the expertise of the notorious Ransomware as a Service group Qilin with possible support from North Korean state aligned threat actors known as Moonstone Sleet. The compromise of the MSP served as the attackers primary access point, triggering a wide scale ransomware outbreak.
Qilin has rapidly become one of the most active ransomware operations of the year, accounting for nearly a third of all reported attacks. The group demonstrated remarkable growth in October 2025 alone, claiming more than 180 victims across global sectors.
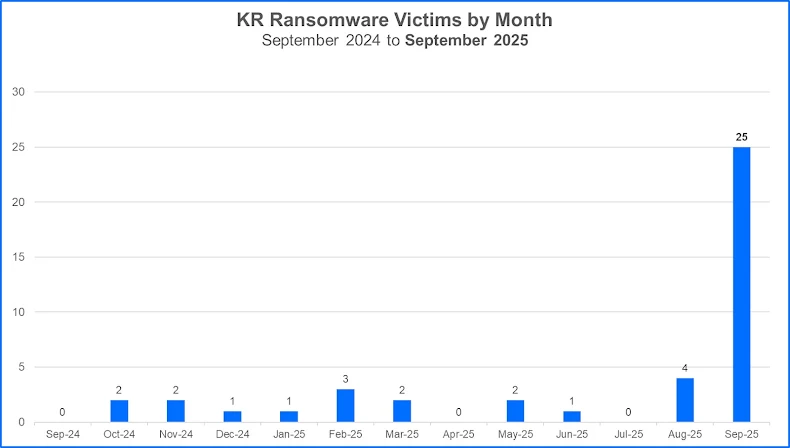
Bitdefender began a deeper investigation after identifying a sudden surge in South Korean victims during September 2025. The country recorded 25 ransomware cases that month, compared to a previous average of only two per month. All affected organizations were linked to Qilin, and 24 of them were part of the financial industry. The threat actors themselves referred to the campaign as Korean Leaks.
Although Qilin is believed to be of Russian origin, its operators frequently portray themselves as political activists. The group runs a typical affiliate based model, recruiting independent hackers and sharing profits, often keeping up to twenty percent of ransom payments.
One known affiliate is Moonstone Sleet, a North Korean threat group documented by Microsoft. In early 2024, the group deployed a custom ransomware named FakePenny against a defense technology company. By February 2025, researchers observed a shift, with the group beginning to distribute Qilin ransomware in limited intrusions. While direct involvement in the latest attacks has not been definitively proven, the focus on South Korean entities aligns with North Korean cyber objectives.
Three Waves of Data Exposure
The Korean Leaks campaign unfolded in three publication waves, revealing more than one million files and approximately two terabytes of stolen data linked to 28 victims. Four additional listings were removed from the ransomware data leak site, which suggests possible ransom settlements or internal policy actions.
The publication timeline included
• Wave 1, ten victims from financial management sectors posted on September 14 2025
• Wave 2, nine victims published between September 17 and 19 2025
• Wave 3, nine victims posted between September 28 and October 4 2025
A notable characteristic of this campaign was its tone. Rather than applying traditional extortion pressure, the attackers used political messaging and public claims of exposing corruption. Early posts threatened to release documents allegedly tied to stock market manipulation or linked to well known public figures in South Korea.
Later waves heightened the warnings, stating that leaked documents could destabilize the national financial market. Attackers also urged regulators to investigate the compromised firms, referring to strict data protection laws in the country.
The third wave initially maintained the political narrative before switching to more familiar financially motivated extortion language associated with Qilin. Bitdefender believes the shifting tone reflects the involvement of Qilin’s central operators, who reportedly maintain an internal writing team to craft posts and assist affiliates during ransom negotiations.
MSP Breach Enabled Mass Compromise
Bitdefender stated that the attackers gained entry by breaching a single upstream MSP, using its privileged access to infect multiple clients. On September 23 2025, the Korea JoongAng Daily reported that more than twenty asset management companies were hit with ransomware after the compromise of the IT services provider GJTec.
Mitigation Measures
Security experts highlight that the Korean Leaks incident illustrates the severe risks associated with third party service providers. To reduce exposure, organizations are urged to enforce multi factor authentication, limit user privileges, segment sensitive systems, and harden their attack surfaces.
Bitdefender emphasized that targeting MSPs offers cybercriminals a practical method to reach multiple victims at once. The incident serves as a reminder that vendor compromise remains a critical blind spot in modern cybersecurity strategies.


