A newly disclosed maximum severity vulnerability in React Server Components has raised significant alarm across the web development ecosystem. The flaw, assigned CVE-2025-55182 and nicknamed React2shell, allows attackers to execute code remotely without authentication simply by sending a specially crafted request to a Server Function endpoint.
Nature of the Vulnerability
The React Team stated that the issue arises from a flaw in how React decodes payloads sent to React Server Function endpoints. Even applications that do not directly implement Server Function endpoints may be exposed if they support React Server Components.
Cloud security analysts from Wiz explained that the problem is rooted in logical deserialization. Unsafe processing of RSC payloads allows an attacker to deliver an adversarial request that React subsequently deserializes into arbitrary JavaScript code, resulting in direct server side execution.
Aikido added that the vulnerability relates to unsafe handling of serialized payloads within the React Flight protocol. Malformed payloads can influence server logic in unintended ways. Updated React versions now include reinforced validation and safer deserialization routines.
Affected Versions
The flaw impacts versions 19.0, 19.1.0, 19.1.1, and 19.2.0 of the following npm packages:
react server dom webpack
react server dom parcel
react server dom turbopack
Patches have been released in versions 19.0.1, 19.1.2, and 19.2.1.
Security researcher Lachlan Davidson from New Zealand discovered and reported the issue to Meta on November 29, 2025. React had recently transitioned from Meta to the React Foundation in October 2025.
Impact on Next.js and Other Frameworks
The same weakness affects Next.js installations using the App Router. The issue was originally recorded as CVE-2025-66478 but later marked as a duplicate of CVE-2025-55182. Affected Next.js versions include:
versions greater than or equal to 14.3.0 canary 77
versions 15 and above
versions 16 and above
Patched versions include 16.0.7, 15.5.7, 15.4.8, 15.3.6, 15.2.6, 15.1.9, and 15.0.5.
Any environment that bundles RSC may also be vulnerable. This includes Vite RSC plugin, Parcel RSC plugin, React Router RSC preview, RedwoodJS, and Waku.
Ease of Exploitation
Endor Labs, Miggo Security, and VulnCheck highlighted that no special permissions or configurations are required to weaponize the flaw. Because the attack requires no login and works through standard HTTP, any accessible endpoint becomes a potential target.
According to Endor Labs, an attacker only needs network access to send a malicious request. Default framework configurations are vulnerable without additional triggers, which means standard production deployments are directly exposed.
Mitigation and WAF Protections
Until patches can be applied, experts recommend enabling Web Application Firewall rules, monitoring HTTP activity for malformed payloads, and restricting access temporarily if possible.
Cloudflare has deployed automated WAF rules to block exploitation attempts. The company said all users, whether free or paid, are protected as long as their React traffic is proxied through Cloudflare services. AWS, Akamai, Fastly, and Google Cloud have also issued similar safeguards.
Wiz reported that around 39 percent of cloud environments contain at least one instance vulnerable to CVE-2025-55182 or its duplicate identifier.
Large Scale Exposure
Justin Moore from Unit 42 at Palo Alto Networks noted that more than 968,000 servers running modern frameworks such as React and Next.js are publicly reachable. He described the flaw as a master key exploit because it abuses the trust within the framework rather than disrupting it.
New Technical Insights into CVE-2025-55182
A recent report from OX Security confirmed that the weakness originates from unsafe deserialization of React Flight reply payloads. Searchlight Cyber developed an HTTP request pattern that can help identify vulnerable systems.
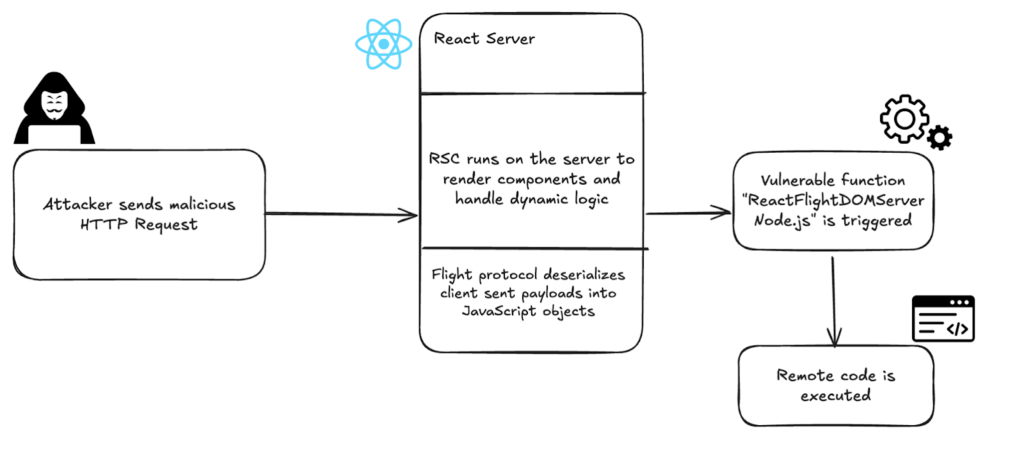
Upwind researchers Avital Harel and Guy Gilad traced the root of the flaw to the requireModule function within React server dom webpack. This function loads server side modules that clients request to call. A malicious HTTP POST request containing a crafted payload can trigger a server action that React executes through vm.runInThisContext, enabling full remote code execution with Node.js level privileges.
The researchers also noted that React itself does not expose the vulnerable endpoint, but Next.js does, making the attack surface reachable from any browser. Since these endpoints accept structured Flight payloads directly, attackers can send their own Flight streams and rely on Next.js to pass them into the vulnerable deserializer.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


