The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive to federal agencies, calling for immediate patching of a critical React vulnerability amid escalating global exploitation. Agencies have now been instructed to apply fixes by December 12, 2025, underscoring the growing severity of the threat.
The flaw, tracked as CVE-2025-55182 with a CVSS score of 10.0, impacts the React Server Components Flight protocol. The issue stems from unsafe deserialization, allowing attackers to inject malicious logic that executes in a privileged server context. Multiple frameworks are affected, including Next.js, Waku, Vite, React Router, and RedwoodSDK.
Cloudflare’s threat intelligence division, Cloudforce One, warned that a single specially crafted HTTP request is enough to exploit the flaw. No authentication, user interaction, or elevated privileges are required, enabling attackers to execute arbitrary JavaScript with high-level permissions on vulnerable servers.
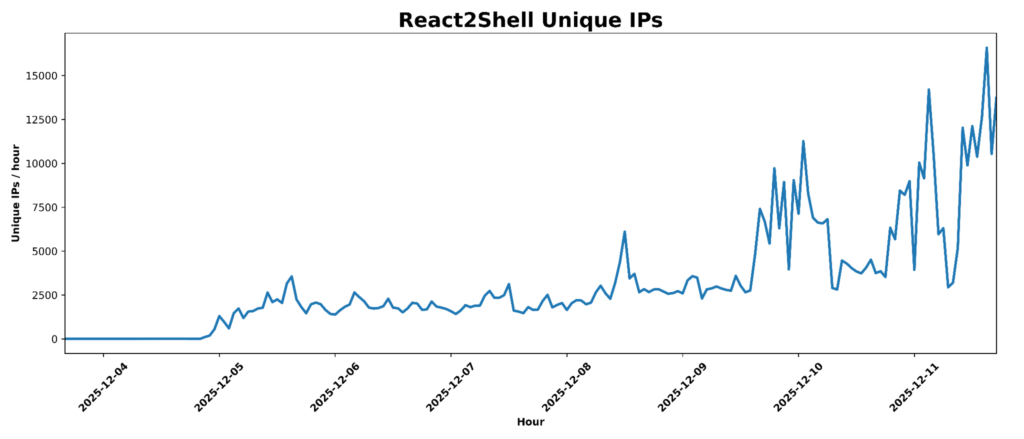
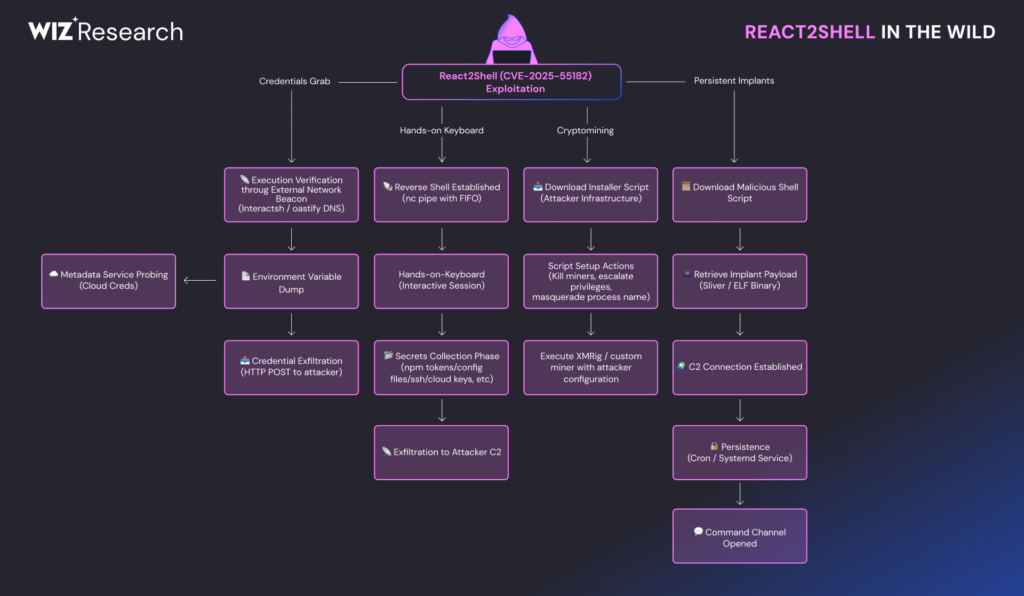
Since its public disclosure on December 3, 2025, the vulnerability has been rapidly adopted by multiple threat actors. Campaigns observed so far range from reconnaissance to the deployment of diverse malware families across exposed environments.
The urgency of the situation led CISA to add the flaw to its Known Exploited Vulnerabilities catalog. While agencies were initially given until December 26 to remediate, the deadline was shortened to December 12, reflecting the speed and scale of real-world attacks.
Wiz reported a rapid surge of opportunistic exploitation attempts, with most attacks focusing on internet-facing Next.js applications. Many of these targets run inside containerized environments such as Kubernetes clusters and managed cloud platforms.
Cloudflare has also confirmed active exploitation, noting that attackers are using large-scale scanning and asset discovery tools to locate exposed React and Next.js services. Some reconnaissance campaigns deliberately excluded Chinese IP ranges, a tactic often associated with geopolitical intelligence operations.
According to Cloudflare, the highest concentration of probing activity was observed in Taiwan, Xinjiang Uyghur, Vietnam, Japan, and New Zealand. In addition, attackers selectively targeted government domains, academic institutions, and critical infrastructure operators, including a national authority overseeing uranium, rare metals, and nuclear fuel imports and exports.
Other notable attack patterns include prioritizing high-sensitivity technology services such as enterprise password managers and secure vault platforms, likely in preparation for supply chain attacks. Edge-facing SSL VPN appliances with React-based administrative interfaces were also probed. Early exploitation attempts were traced back to IP addresses historically linked to Asia-aligned threat clusters.
Independent analysis from Kaspersky revealed more than 35,000 exploitation attempts in a single day on December 10, 2025. Initial commands such as whoami were often followed by the deployment of cryptocurrency miners, Mirai and Gafgyt botnet variants, and the RondoDox malware.
Additional payloads observed include Cobalt Strike beacons, Sliver, Fast Reverse Proxy, a monitoring tool known as Nezha, Node.js malware designed to harvest sensitive files, and Go-based backdoors with reconnaissance and command-and-control capabilities.
Research from VulnCheck indicates that more than 140 proof-of-concept exploits are circulating in the wild. Roughly half are broken or misleading, while functional samples demonstrate capabilities such as in-memory web shell deployment, automated scanning, and even lightweight web application firewall installation to block rival attackers.
Security researcher Rakesh Krishnan also identified an open directory hosting exploit scripts alongside target lists containing tens of thousands of domains. Several high-profile brands were included, suggesting active and automated targeting across the internet.
Coalition compared the incident to the 2021 Log4Shell crisis, describing it as a systemic cyber risk aggregation event with far-reaching implications.
According to the latest data from The Shadowserver Foundation, more than 137,200 internet-exposed IP addresses were running vulnerable code as of December 11, 2025. Over 88,900 of these systems are located in the United States, followed by Germany, France, and India.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


