A cyber espionage cluster previously identified in large-scale campaigns across Africa, Asia, North America, South America, and Oceania has now been assessed as a Chinese state-sponsored threat group.
Threat intelligence firm Recorded Future, which earlier tracked this activity under the identifier TAG-100, has elevated the group’s status and assigned it the name RedNovember. Microsoft is also monitoring the same actor under the designation Storm-2077.
According to a report shared with The Hacker News, the group conducted extensive campaigns between June 2024 and July 2025, targeting perimeter appliances belonging to high-profile organizations worldwide. During these intrusions, they leveraged the Go-based backdoor Pantegana along with Cobalt Strike to gain persistence and move laterally within networks.
The targeting scope has expanded significantly, including government institutions, defense and aerospace sectors, space organizations, and law firms. Likely victims include:
- A ministry of foreign affairs in Central Asia
- A state security agency in Africa
- A European government directorate
- A Southeast Asian government
- Two U.S. defense contractors
- A European engine manufacturer
- A Southeast Asian intergovernmental trade-focused organization
Exploitation Methods
RedNovember has been exploiting vulnerabilities in widely used internet-facing perimeter appliances. These include products from:
- Check Point (CVE-2024-24919)
- Cisco
- Citrix
- F5
- Fortinet
- Ivanti
- Palo Alto Networks (CVE-2024-3400)
- SonicWall
Their focus on VPNs, firewalls, load balancers, virtualization systems, and email servers reflects a broader pattern among Chinese-backed groups, who rely on these techniques to maintain long-term access and evade detection.
Tools and Tradecraft
A distinguishing trait of RedNovember is its reliance on open-source tools, particularly Pantegana and Spark RAT. By repurposing public tools, the group complicates attribution efforts while reducing development overhead, a strategy frequently observed in state-sponsored espionage.
The attacks also feature a modified version of LESLIELOADER, a Go-based loader, to deploy Spark RAT or Cobalt Strike Beacons on infected endpoints.
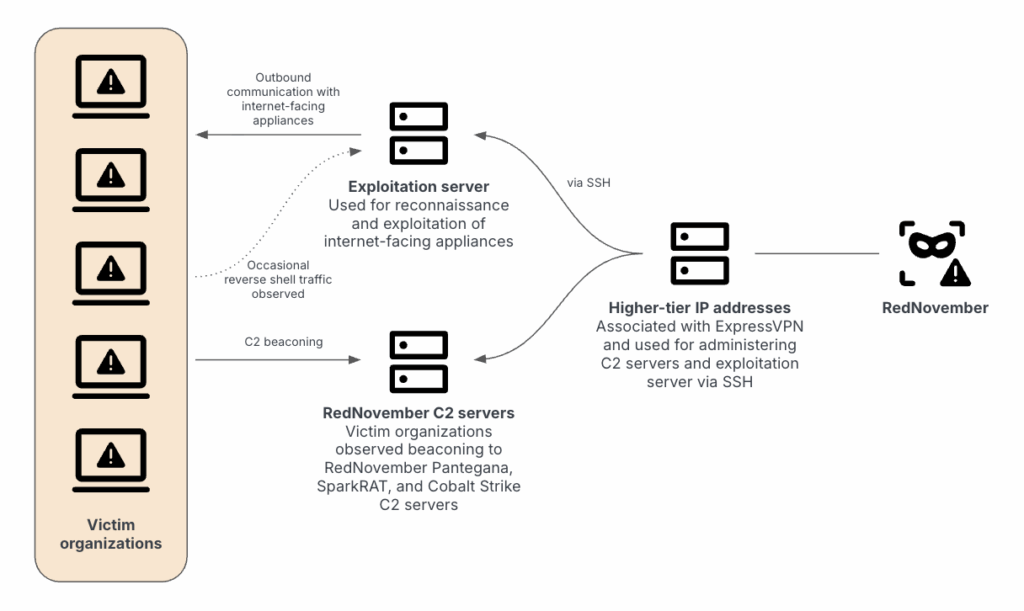
For command-and-control operations, RedNovember uses VPN services such as ExpressVPN and Warp VPN. These services enable the group to manage infrastructure, exploit vulnerable devices, and maintain communication with their deployed payloads.
Between June 2024 and May 2025, RedNovember focused heavily on Panama, the U.S., Taiwan, and South Korea. As recently as April 2025, they targeted Ivanti Connect Secure appliances belonging to a U.S.-based newspaper and a defense contractor.
Recorded Future also reported attempted intrusions against Microsoft Outlook Web Access (OWA) portals linked to a South American nation just before its state visit to China.
Global Targeting Strategy
Recorded Future’s findings highlight the group’s shifting objectives and extensive operational reach. RedNovember’s campaigns span across the U.S., Southeast Asia, the Pacific region, and South America, pointing to diverse and evolving intelligence requirements.
The adoption of public tools, aggressive targeting of perimeter devices, and global victim set demonstrate that RedNovember is among the more adaptive and persistent Chinese state-sponsored hacking groups.


