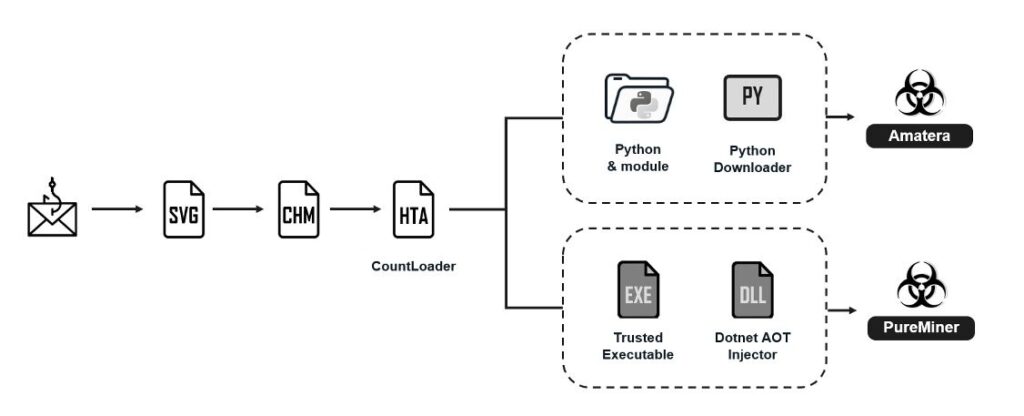
Researchers have uncovered a new phishing campaign that impersonates Ukrainian government organizations to distribute CountLoader, which subsequently delivers Amatera Stealer and PureMiner.
According to Fortinet FortiGuard Labs researcher Yurren Wan, “The phishing emails carry malicious Scalable Vector Graphics (SVG) files designed to deceive recipients into opening dangerous attachments.”
In the attack scenarios analyzed by cybersecurity experts, these SVG files trigger the download of a password-protected ZIP archive containing a Compiled HTML Help (CHM) file. When opened, the CHM file initiates a series of actions that ultimately deploy CountLoader. The emails are disguised as notifications from the National Police of Ukraine.
CountLoader, recently studied by Silent Push, is known to drop various payloads including Cobalt Strike, AdaptixC2, and PureHVNC RAT. In this particular campaign, it acts as a delivery mechanism for Amatera Stealer, a variant of ACRStealer, and PureMiner, a stealthy .NET-based cryptocurrency miner.
Both PureHVNC RAT and PureMiner are components of a larger malware suite created by an actor known as PureCoder. Other malware products from the same developer include:
- PureCrypter: Crypter for Native and .NET applications
- PureRAT (aka ResolverRAT): Successor to PureHVNC RAT
- PureLogs: Information stealer and logger
- BlueLoader: Malware capable of acting as a botnet for downloading and executing remote payloads
- PureClipper: Clipboard malware that replaces cryptocurrency addresses with attacker-controlled wallets to steal funds
Fortinet reports that Amatera Stealer and PureMiner are deployed as fileless threats. The malware executes through .NET Ahead-of-Time (AOT) compilation with process hollowing or is loaded directly into memory using PythonMemoryModule.
Once executed, Amatera Stealer collects system data, files with specific extensions, and information from Chromium- and Gecko-based browsers, as well as applications such as Steam, Telegram, FileZilla, and various crypto wallets.
“This phishing campaign illustrates how a malicious SVG file can act as an HTML substitute to initiate an infection chain,” Fortinet said. The attackers targeted Ukrainian government offices by sending emails with SVG attachments containing embedded HTML code that redirects victims to a download site.
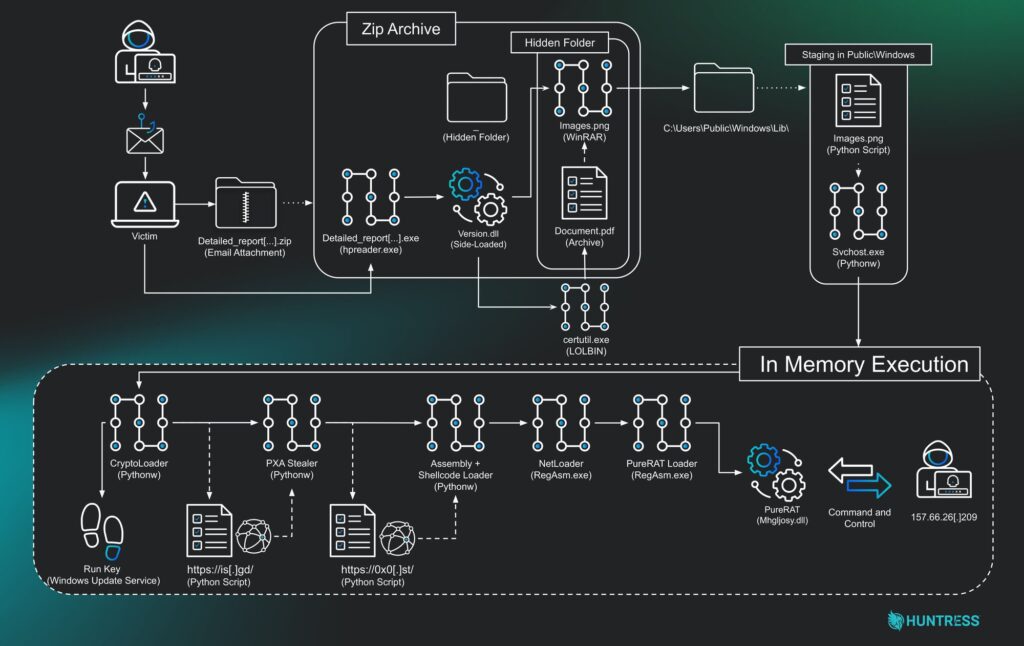
Huntress researchers have also discovered a likely Vietnamese-speaking threat group using phishing emails themed around copyright infringement notices. These emails trick users into opening ZIP archives that deploy PXA Stealer, eventually leading to a multi-stage infection that delivers PureRAT.
Security researcher James Northey stated, “This campaign shows a deliberate progression: starting with a basic phishing lure, escalating through in-memory loaders, defense evasion, and credential theft. The final payload, PureRAT, is a modular backdoor giving attackers full control over compromised systems.”
He added, “Their evolution from simple Python payload obfuscation to leveraging commodity malware like PureRAT demonstrates persistence and the traits of a professional, maturing threat actor.”


