A powerful open-source command-and-control (C2) framework named AdaptixC2 is rapidly being adopted by a wide range of cybercriminals, with strong links to Russian ransomware operations. This trend highlights the ongoing weaponization of legitimate security tools by threat actors to conduct more advanced and evasive attacks.
What is AdaptixC2?
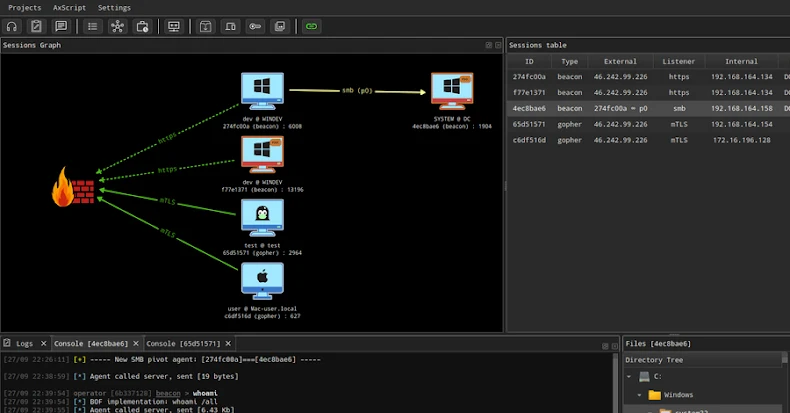
AdaptixC2 is an emerging, extensible post-exploitation framework originally designed for penetration testing and adversarial emulation. Its architecture is built for cross-platform compatibility, featuring a server component written in Golang and a graphical user interface (GUI) client developed in C++ QT.
The framework boasts a comprehensive set of features, including:
- Fully encrypted communications.
- Remote command execution.
- Integrated credential and screenshot managers.
- A built-in remote terminal.
The project was initially released to the public in August 2024 by a GitHub user known as “RalfHacker,” who self-identifies as a penetration tester, red team operator, and “MalDev” (malware developer).
Adoption by Malicious Actors
Despite its ethical origins, AdaptixC2 has quickly attracted the attention of cybercriminals. In recent months, it has been observed in the toolkits of:
- Threat actors associated with the Fog and Akira ransomware operations.
- An initial access broker who used it in conjunction with CountLoader to deploy additional post-exploitation tools.
Palo Alto Networks Unit 42 has described AdaptixC2 as a “modular and versatile framework” capable of granting attackers comprehensive control over compromised machines. It has been deployed in various attack vectors, including fake help desk support scams over Microsoft Teams and through AI-generated PowerShell scripts.
The Developer’s Ambitions and Criminal Links
Cybersecurity firm Silent Push initiated an investigation after noting the developer’s “MalDev” bio. Their probe uncovered several email addresses linked to the GitHub account owner and a Telegram channel named “RalfHackerChannel” with over 28,000 subscribers, where content from a dedicated AdaptixC2 channel is shared.
In a message from August 2024, the developer expressed a desire to create a “public C2, which is very trendy right now,” hoping it would become as influential as “Empire,” another famous post-exploitation framework.
While there is no direct evidence linking RalfHacker to ongoing malicious campaigns, the connections are concerning. Silent Push stated, “Their ties to Russia’s criminal underground, via the use of Telegram for marketing and the tool’s subsequent uptick in utilization by Russian threat actors, all raise significant red flags.”
A Familiar Pattern: The Abuse of Red-Teaming Tools
The exploitation of AdaptixC2 follows a well-established pattern in the cybercrime world. Other legitimate red-teaming tools like Havoc, Mythic, and Sliver are frequently repurposed by attackers. Furthermore, cracked and illicit copies of commercial frameworks like Cobalt Strike and Brute Ratel C4 have been massively abused in recent years, providing threat actors with sophisticated capabilities without the development cost.