Cybersecurity researchers have uncovered a newly developed banking malware named VENON, which specifically targets users in Brazil. The malware is written in Rust, marking a notable shift from the traditional Delphi-based malware families commonly associated with the Latin American cybercrime landscape.
The malicious program, designed to infect Windows systems, was discovered recently and analyzed by the Brazilian cybersecurity firm ZenoX.
A New Evolution in Latin American Banking Malware
VENON stands out because it mirrors behavioral patterns seen in well-known regional banking trojans such as:
- Grandoreiro banking trojan
- Mekotio banking trojan
- Coyote banking trojan
These malware families are known for features like banking overlays, monitoring active windows, and manipulating system shortcuts to redirect victims.
Despite these similarities, VENON has not yet been linked to any previously identified cybercrime group or campaign.
Possible AI-Assisted Malware Development
Researchers discovered traces suggesting that the malware developer may have relied on generative AI tools to recreate and expand existing banking trojan capabilities in Rust.
The analysis revealed file paths within the malware that pointed to a development machine using the username “byst4”, for example:
C:\Users\byst4\...
According to ZenoX, the structure of the Rust code indicates that the developer likely understood the functionality of existing Latin American malware frameworks but used AI assistance to rewrite and extend those capabilities.
Infection Method and Delivery Chain
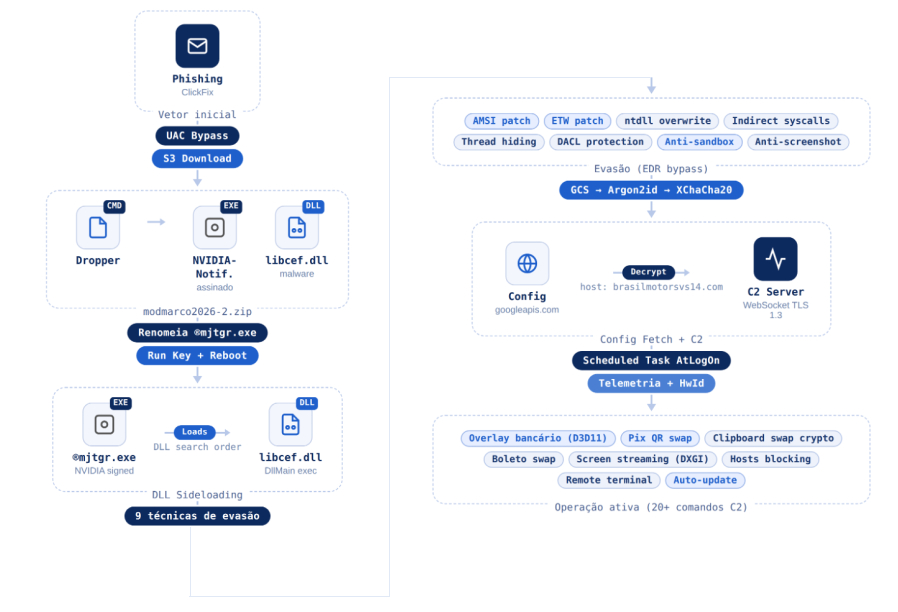
The VENON campaign uses a multi-stage infection process designed to evade detection. The attack begins with social engineering techniques that trick users into downloading a ZIP archive containing malicious files.
One suspected tactic is ClickFix, where victims are encouraged to execute a PowerShell command that downloads the malware payload.
The attack chain includes DLL side-loading, allowing a malicious dynamic link library to run alongside legitimate software components.
Advanced Evasion Techniques
Before initiating malicious activity, VENON performs several defensive evasion checks, including:
- Anti sandbox verification
- Indirect system calls
- Event Tracing for Windows (ETW) bypass
- Antimalware Scan Interface (AMSI) bypass
Once these checks are completed, the malware retrieves configuration data from a Google Cloud Storage link. It then creates a scheduled task and establishes a WebSocket connection with its command and control (C2) server.
Shortcut Hijacking and Banking Credential Theft
Embedded within the malicious DLL are two Visual Basic Script components responsible for a shortcut hijacking technique targeting the **Itaú banking application.
These scripts replace legitimate application shortcuts with modified ones that redirect victims to attacker controlled phishing pages.
Interestingly, the malware also includes an uninstall feature that restores the original shortcuts. This capability suggests that attackers can remotely remove traces of the compromise after completing their objectives.
Targeting 33 Financial Institutions
VENON monitors active application windows and browser domains on infected systems. When the malware detects that a victim is accessing any of the 33 targeted banks or cryptocurrency services, it launches credential stealing overlays that imitate legitimate login interfaces.
This technique allows attackers to collect sensitive authentication details without raising immediate suspicion.
WhatsApp Based Malware Distribution Campaigns
At the same time, researchers observed another attack campaign exploiting WhatsApp to spread a worm called SORVEPOTEL worm.
The worm spreads through previously authenticated chat sessions on the messaging platform’s desktop version. Victims receive malicious messages that lead them into multi stage infection chains.
These infections ultimately deploy banking malware such as:
- Maverick banking malware
- Casbaneiro banking trojan
- Astaroth malware
Researchers noted that even a single malicious message delivered through a compromised messaging session could initiate the entire attack chain.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


