Cybersecurity researchers have revealed a cross site scripting vulnerability in the web based administration panel used by operators of the StealC information stealing malware, enabling analysts to observe and collect intelligence on one of the threat actors actively running the operation.
CyberArk researcher Ari Novick stated that exploitation of the flaw allowed researchers to collect system fingerprints, track active sessions, and retrieve cookies from the same infrastructure designed to steal user data. The findings were published in a report released last week.
StealC first appeared in January 2023 and operates under a malware as a service model, allowing affiliates to deploy the stealer in exchange for a fee. One of its earliest and most notable distribution strategies relied on YouTube, where attackers promoted the malware as cracked versions of popular software. This method later became known as the YouTube Ghost Network.
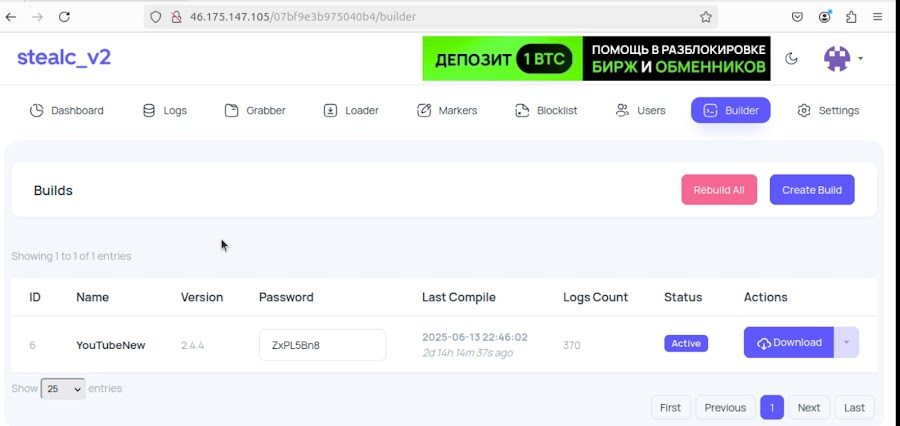
Over the past year, StealC has expanded its delivery techniques to include malicious Blender Foundation files and a social engineering method known as FileFix. At the same time, the malware itself evolved, introducing Telegram bot alerts, improved payload deployment features, and a redesigned control interface. This upgraded version was labeled StealC V2.
Shortly after these changes, the source code for the StealC administration panel was leaked online. This incident enabled researchers to examine the backend infrastructure and extract identifying details about operators, including approximate location indicators, hardware characteristics, and active session cookies tied to the attackers’ own systems.
Specific technical details about the XSS vulnerability were intentionally withheld to prevent the malware developers from quickly fixing the issue or enabling copycat groups to misuse the leaked panel code.
Cross site scripting vulnerabilities are a type of client side injection flaw that occurs when applications fail to properly validate and encode user input. Such weaknesses allow malicious JavaScript to run inside a victim’s browser, leading to cookie theft, session impersonation, and unauthorized access to sensitive information.
Novick noted the irony of the situation, explaining that despite StealC being centered around large scale cookie theft, its developers failed to implement basic cookie security protections such as httpOnly flags. As a result, their own session cookies were exposed through a standard XSS attack.
CyberArk also detailed activity linked to a StealC customer known as YouTubeTA, short for YouTube Threat Actor. This individual heavily abused YouTube to distribute the malware by advertising cracked versions of Adobe Photoshop and Adobe After Effects. The campaign resulted in more than 5,000 infection logs, containing approximately 390,000 stolen passwords and over 30 million cookies, the majority of which were tracking or non sensitive cookies.
Researchers believe these stolen credentials were used to hijack legitimate YouTube accounts, which were then repurposed to promote malicious content, creating a continuous self propagating infection cycle. Evidence also suggests the use of fake CAPTCHA techniques similar to ClickFix, indicating StealC distribution was not limited to YouTube alone.
Further analysis revealed that the StealC panel supports multiple user roles, allowing separation between administrators and standard users. In the case of YouTubeTA, only a single administrator account was present. That account appeared to be accessed from a system running on an Apple M3 processor, configured with both English and Russian language settings.
An operational security mistake exposed the threat actor’s location in mid July 2025, when they accessed the panel without using a VPN. This revealed a real IP address associated with TRK Cable TV, a Ukrainian internet provider. Based on these findings, researchers assess that YouTubeTA is likely a lone actor operating from an Eastern European region where Russian is widely spoken.
The research highlights both the efficiency and the risks of the malware as a service ecosystem. While it enables rapid scaling of cybercrime operations, it also exposes threat actors to the same security flaws faced by legitimate software platforms.
CyberArk concluded that weaknesses in StealC’s panel code and cookie handling allowed researchers to gather extensive intelligence about its users. If similar vulnerabilities exist across other malware platforms, security researchers and law enforcement agencies may be able to use them to identify and disrupt criminal operations.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


