A recently addressed security flaw in Microsoft Windows Server Update Services, also known as WSUS, is being actively abused by attackers to deploy the advanced ShadowPad malware. According to a report from the AhnLab Security Intelligence Center, the threat actors used CVE 2025 59287 as the initial entry point into targeted Windows servers.
Attackers Use WSUS Flaw to Install ShadowPad
ASEC explained that the attackers targeted servers running WSUS and exploited the critical deserialization vulnerability to gain remote code execution with system privileges. Once inside, the operators used PowerCat, an open source PowerShell version of Netcat, to obtain a system level command shell.
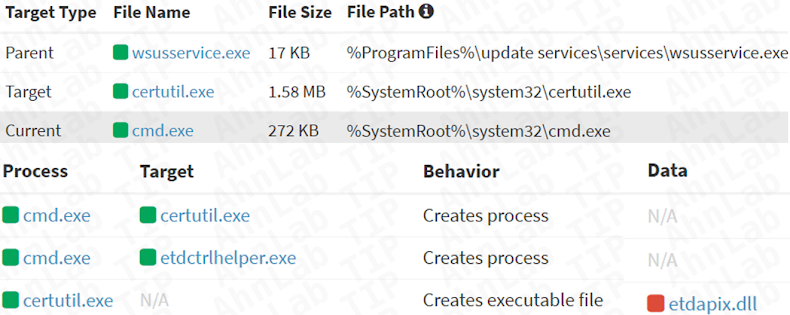
The attackers then executed a sequence of commands that included the use of certutil and curl to download and install ShadowPad from an external server identified as 149.28.78[.]189:42306.
ShadowPad is viewed as the successor to PlugX and is widely linked to Chinese state sponsored groups. The backdoor first appeared in 2015 and has been described by security analysts as one of the most sophisticated privately distributed malware families used in espionage operations.
Critical Vulnerability Faces Heavy Exploitation
Microsoft patched CVE 2025 59287 last month. Since the release of the proof of concept exploit code, threat actors rapidly weaponized the flaw to compromise publicly accessible WSUS servers. Attackers were seen performing reconnaissance, dropping legitimate tools such as Velociraptor, and preparing the system for deeper compromise.
In the incident documented by ASEC, the operators used Windows utilities like curl.exe and certutil.exe to fetch the malicious payload. ShadowPad was then deployed through a DLL side loading technique that used a legitimate binary, ETDCtrlHelper.exe, to load a malicious DLL named ETDApix.dll. This DLL acted as a memory based loader that launched the ShadowPad backdoor.
ShadowPad Features Modular Capabilities and Strong Persistence
Once installed, ShadowPad runs a core component that loads additional plugins embedded in the shellcode. The malware contains various anti detection features and persistence techniques designed to maintain long term access.
So far, this campaign has not been attributed to a specific threat group. However, ASEC warned that the rapid adoption of the exploit highlights the severity of the vulnerability.
Security Analysts Warn of Serious Impact
AhnLab stated that the release of public exploit code accelerated attacks involving ShadowPad distribution through WSUS servers. The company emphasized that the flaw is critical because it allows remote code execution with full system permission, increasing the potential impact across organizations that rely on WSUS for updates.