A new wave of the Shai Hulud supply chain attack has now moved beyond the npm ecosystem and into Maven, exposing thousands of sensitive credentials and widening the reach of one of the most impactful attacks of the year. Security researchers have confirmed that the second phase of the operation has compromised more than 830 npm packages and has now surfaced in at least one Maven package, signaling a significant escalation.
Attack Expands Into Maven
The Socket Research Team reported discovering a Maven Central package, org.mvnpm, which contains the same two malicious components found in Shai Hulud infections on npm. These include the loader file setup_bun.js and the primary payload bun_environment.js. Investigators noted that this is the only Java artifact identified so far that contains the Shai Hulud v2 payload.
The affected Maven package is not officially published by PostHog. Instead, it was created through an automated mvnpm process that rebuilds npm packages into Maven artifacts. Maven Central stated that it has removed all mirrored copies as of November 25, 2025, 22:44 UTC, and is preparing additional security measures to block re publishing of compromised npm components.
A Stealthy and Aggressive Supply Chain Threat
The renewed attack wave targets developers around the world and focuses on stealing API keys, cloud access credentials, and tokens for npm and GitHub. Researchers noted that this updated version is more silent, scalable, and destructive than the original September outbreak.
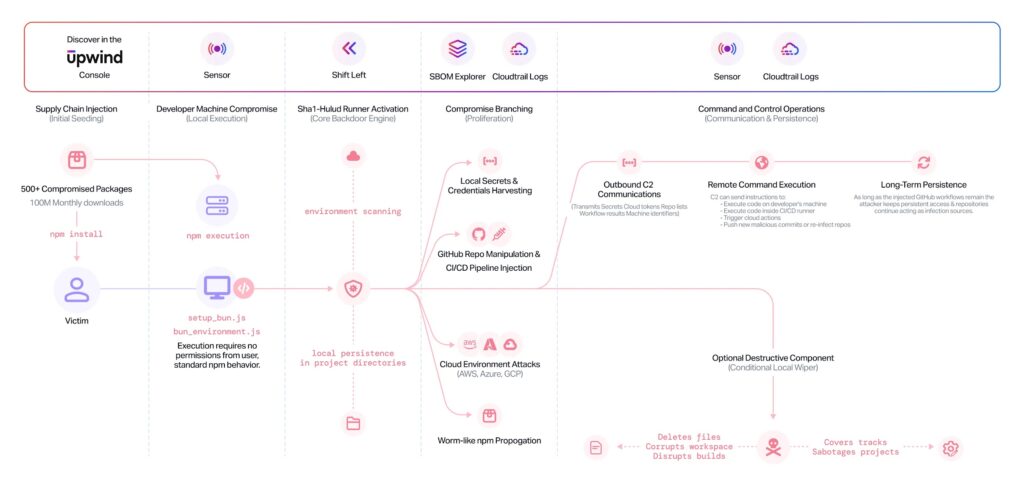
Shai Hulud v2 infects projects by taking over npm maintainer accounts and distributing trojanized packages. When unsuspecting developers install these packages, the included malware backdoors their systems, searches for sensitive secrets, and exfiltrates the data to GitHub using stolen tokens.
The malware deploys two malicious GitHub workflows. One workflow registers the victim machine as a self hosted runner, enabling remote command execution whenever a GitHub Discussion is opened. The second workflow systematically gathers secrets from the repository. More than 28,000 repositories have been affected so far.

Technical Evolution of the Attack
Researchers from Cycode highlighted that Shai Hulud v2 uses the Bun runtime to conceal core malicious logic and increases its infection limit from 20 to 100 packages. It also switches its exfiltration method by sending stolen data to randomly generated public GitHub repositories instead of a single hard coded destination.
Further investigation by Aikido revealed that attackers abused CI pipeline weaknesses, particularly misconfigurations in pull_request_target and workflow_run, to infiltrate major projects including AsyncAPI, PostHog, and Postman. According to security researcher Ilyas Makari, a single flawed workflow was enough to turn a repository into ground zero for a rapidly spreading attack.
A Broader Campaign With Severe Impact
The current activity is linked to a wider chain of attacks that began with the S1ngularity campaign in August 2025, which targeted Nx packages on npm. According to researchers from Apiiro, Shai Hulud v2 stands out because of its mix of stealth, credential theft, scale, and fallback destructive behavior.
Data collected by GitGuardian, OX Security, and Wiz shows the campaign has leaked hundreds of GitHub tokens along with cloud credentials for AWS, Google Cloud, and Microsoft Azure. More than 5,000 files containing sensitive secrets were uploaded to GitHub. A review of 4,645 repositories identified 11,858 unique secrets, with 2,298 still valid as of November 24, 2025.


