A new cyber espionage campaign has been uncovered, showing the continuous evolution of the SideWinder advanced persistent threat (APT) group. The operation, which took place in September 2025, targeted a European embassy in New Delhi and multiple organizations across Sri Lanka, Pakistan, and Bangladesh. Researchers from Trellix, Ernesto Fernández Provecho and Pham Duy Phuc, have reported a significant shift in the group’s tactics and techniques, particularly with the adoption of a PDF and ClickOnce-based attack chain alongside their older Microsoft Word exploits.
Evolution of SideWinder’s Attack Techniques
According to Trellix’s findings, SideWinder executed a series of spear-phishing campaigns between March and September 2025, delivering malicious attachments designed to install ModuleInstaller and StealerBot malware families. These tools were used to collect sensitive data and execute further malicious operations on compromised systems.
- ModuleInstaller acts as a downloader for additional payloads.
- StealerBot, a .NET-based implant, can open a reverse shell, execute new malware, and steal data such as screenshots, keystrokes, passwords, and files.
Both malware variants were previously reported by Kaspersky in October 2024, when SideWinder was seen attacking high-value entities in the Middle East and Africa.
By May 2025, Acronis also documented similar campaigns targeting government institutions in Sri Lanka, Bangladesh, and Pakistan, using malware-laden Microsoft Office documents exploiting known vulnerabilities.
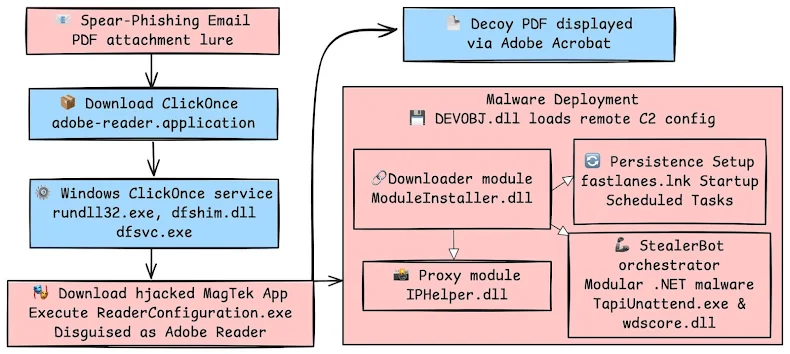
ClickOnce-Based Infection Chain
Trellix’s latest observations, post-September 2025, highlight phishing emails aimed at Indian embassies. These emails carried malicious attachments like “Inter-ministerial meeting Credentials.pdf” or “India-Pakistan Conflict – Strategic and Tactical Analysis of the May 2025.docx” and were sent from the spoofed domain “mod.gov.bd.pk-mail[.]org”, impersonating Pakistan’s Ministry of Defense.
The infection begins when the victim opens a PDF or Word file that appears unreadable or contains a fake prompt urging them to update Adobe Reader. Clicking the button triggers the download of a ClickOnce application hosted on “mofa-gov-bd.filenest[.]live”.
This application sideloads a malicious DLL file (DEVOBJ.dll) while simultaneously opening a decoy PDF to distract the victim. The ClickOnce app itself is a legitimate executable from MagTek Inc. (ReaderConfiguration.exe) and is signed with a valid certificate to avoid detection.
Communication with the command-and-control (C2) server is restricted to South Asian regions, and the payload path is dynamically generated, making analysis and detection more complex.
Malware Execution and Objectives
Once executed, the rogue DLL decrypts and launches the ModuleInstaller loader, which profiles the victim’s machine and deploys StealerBot for data theft and persistence. This method demonstrates SideWinder’s refined use of side-loading techniques and region-specific infrastructure to evade detection.