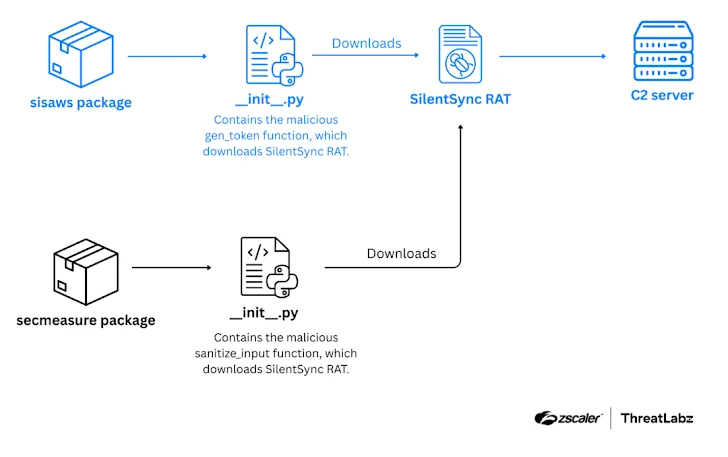
Both packages pose as useful developer libraries, however, they contain hidden functionality that fetches and runs additional Python code, which implants SilentSync. The trojan supports remote command execution, file theft, and screen capture, and it specifically targets browser data such as saved credentials, history, autofill information, and cookies from Chrome, Brave, Edge, and Firefox, according to Zscaler researchers Manisha Ramcharan Prajapati and Satyam Singh.
How sisaws works, technical details
The sisaws package imitates the legitimate sisa library associated with Argentina’s SISA health system, a classic typosquatting tactic. Inside its initialization file, init.py, there is a function called gen_token(), which behaves as a downloader for a second-stage payload. When a developer imports sisaws and calls gen_token(), the function decodes a hexadecimal string that reveals a curl command. That curl command fetches a Python script hosted on PasteBin, the script is written to a temporary file named helper.py, and then executed. This secondary script is the one that brings SilentSync onto the host.
How secmeasure delivers SilentSync
Secmeasure claims to be a utility for string cleaning and security related helpers, but it embeds functionality to drop the same SilentSync RAT. Both malicious packages rely on an exchange of tokens, where a hard coded token is sent and a static secondary token is returned, mimicking legitimate API behavior to avoid immediate detection.
Command and control, persistence mechanisms, and cross platform notes
After obtaining the secondary token, the packages make an HTTP GET request to a hard coded endpoint at 200.58.107[.]25 to retrieve Python code that is executed in memory. The malware supports these server endpoints, listed as, /checkin, to verify connectivity, /comando, to request commands, /respuesta, to send status messages, /archivo, to transmit command output or stolen files.
Although SilentSync currently focuses on Windows targets, it includes cross platform capabilities. On Windows it makes Registry changes for persistence, on Linux it alters crontab entries to run at startup, and on macOS it registers a LaunchAgent to achieve the same effect. The payload can execute arbitrary shell commands, capture screenshots, compress and exfiltrate files or full directories as ZIP archives, and then remove local artifacts to reduce forensic traces.
Why this matters, supply chain and developer hygiene implications
This incident highlights the growing risk of supply chain compromises in public package repositories. By abusing typosquatting and impersonating legitimate packages, threat actors can trick developers into importing malicious libraries, which in turn gives attackers a path to steal personally identifiable information, credentials, and proprietary code. Developers who test or run packages locally, or include them in build pipelines, may inadvertently introduce SilentSync into developer workstations, CI runners, or production systems.
Mitigations, best practices for Python developers and organizations
- Verify package provenance before importing, including author names and project metadata, and prefer pinned versions from trusted sources.
- Use virtual environments and isolated build systems, to limit blast radius if a package is malicious.
- Scan dependencies with software composition analysis tools and malware detectors, and monitor for unusual network activity to unknown endpoints such as 200.58.107[.]25.
- Avoid running third party package code with elevated privileges, and treat any package that performs network requests at import time as suspicious.
- For CI or production, use reproducible builds, vendor dependencies when possible, and apply allowlists for approved packages.