A malicious extension discovered in the Open VSX registry poses a significant threat to developers by embedding a remote access trojan named SleepyDuck. What makes this threat particularly resilient is its innovative use of the Ethereum blockchain to maintain contact with its command server, ensuring it can survive traditional takedown efforts.
The Malicious Extension and Its Deployment Strategy
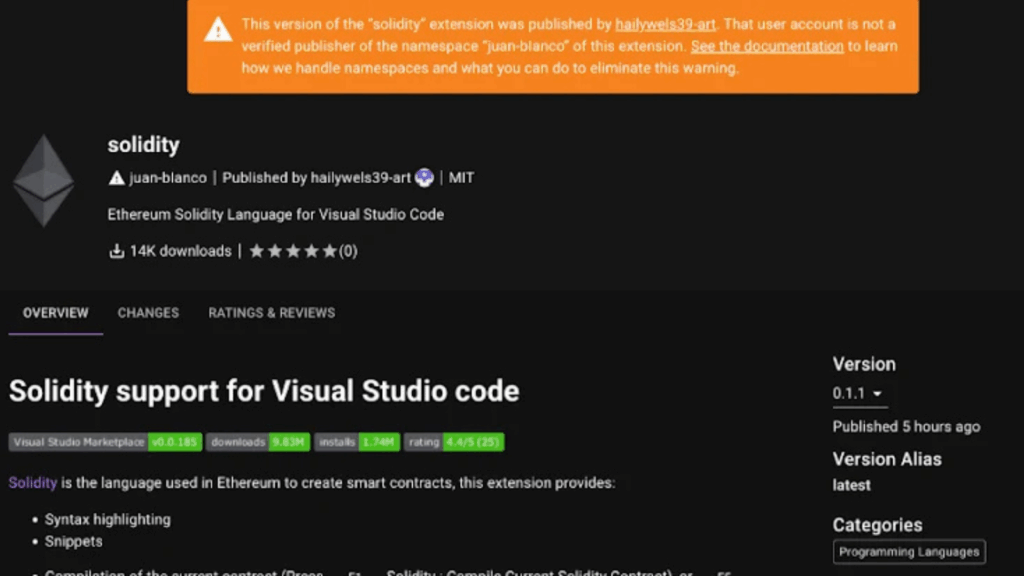
The malicious extension, identified as juan-bianco.solidity-vlang, was first published on October 31, 2025. Its initial version (0.0.7) was completely harmless, a tactic likely used to build trust and avoid immediate detection. After amassing over 14,000 downloads, the attacker updated it to version 0.0.8 on November 1, injecting it with malicious capabilities.
This pattern of targeting Solidity developers with rogue extensions is not new. In a similar incident in July 2025, a Russian developer lost $500,000 in cryptocurrency after installing a malicious extension through the Cursor editor.
SleepyDuck’s Sophisticated Attack Mechanism
The malware activates when a developer opens a new code editor window or selects a .sol (Solidity) file. Its execution involves a multi-stage, evasive process:
- Sandbox Evasion: The payload first employs techniques to detect if it’s running in a security sandbox, terminating itself to avoid analysis.
- Ethereum RPC Connection: It finds the fastest available Ethereum RPC provider to connect to the blockchain.
- C2 Communication: It reads a specific, hardcoded Ethereum contract address (
0xDAfb81732db454DA238e9cFC9A9Fe5fb8e34c465) to retrieve the location of its command-and-control (C2) server, which was initiallysleepyduck[.]xyz. - Persistent Polling: It starts a loop that checks this C2 server for new commands every 30 seconds, allowing for near real-time control of the infected machine.
The malware also collects system information (hostname, username, MAC address, timezone) and sends it back to the attacker.
The Ethereum Blockchain as a Resilient Fallback Mechanism
The most notable feature of SleepyDuck is its use of decentralized technology for resilience. If the sleepyduck[.]xyz domain is seized or taken down by authorities, the malware does not become inert. Instead, it has a built-in backup plan:
- It contacts a predefined list of Ethereum RPC providers.
- It queries the same hardcoded Ethereum contract.
- The attacker can update this contract with a new C2 server address via a blockchain transaction.
- The malware then retrieves this new address and re-establishes communication.
This means that as long as the Ethereum blockchain exists and the contract is funded, the attacker can redirect the infected machines to a new server with minimal effort, making a complete takedown extremely difficult.
A Separate Campaign: Cryptojacking Extensions on VS Code Marketplace
In a related discovery, five other malicious extensions were found on the official VS Code Marketplace, published by a user named “developmentinc.” These included a Pokémon-themed extension that acted as a cryptojacker.
- Upon installation, the extension immediately downloaded a batch script from
mock1[.]su. - The script attempted to gain administrator privileges and configured Microsoft Defender to exclude all drive letters (C: to Z:) from scans.
- It then downloaded and executed a Monero cryptocurrency miner, hijacking the victim’s computing resources for profit.
The malicious extensions have since been removed, but their names were:
developmentinc.cfx-lua-vsdevelopmentinc.pokemondevelopmentinc.torizon-vsdevelopmentinc.minecraftsnippetsdevelopmentinc.kombai-vs