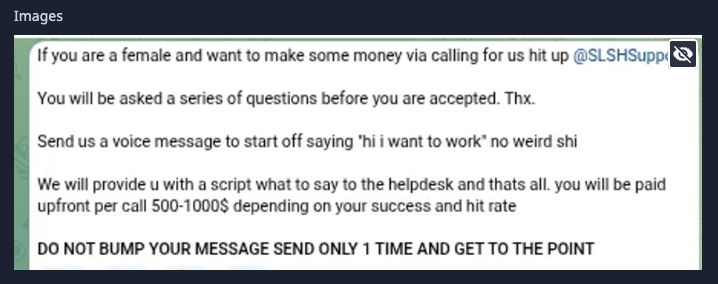
The cybercrime collective Scattered LAPSUS$ Hunters (SLH) has been reported recruiting women to execute voice phishing (vishing) attacks against IT help desks. According to Dataminr, the group is offering $500–$1,000 per call and supplying pre-written scripts to maximize the chances of success.
The initiative reflects a shift in social engineering tactics, leveraging the assumption that female voices may be perceived as less threatening and thereby more effective for impersonation. This recruitment drive specifically targets IT support personnel to bypass multi-factor authentication (MFA) and gain privileged access.
Attack Methods
SLH and its associated supergroups, including LAPSUS$, Scattered Spider, and ShinyHunters, have a history of sophisticated social engineering attacks:
- Vishing for Credential Access: Attackers pose as employees to request password resets or installation of remote monitoring tools.
- MFA Bypass: Techniques include MFA prompt bombing and SIM swapping.
- Lateral Movement: After initial access, they navigate virtualized environments to escalate privileges and exfiltrate sensitive corporate data.
- Use of Legitimate Tools: Residential proxies like Luminati and OxyLabs, tunneling services such as Ngrok and Teleport, and file-sharing platforms like file.io and mega.nz help attackers blend in.
- Cloud Exploitation: Scattered Spider has targeted Microsoft Azure environments via Graph API and performed Active Directory reconnaissance using tools like ADRecon.
Unit 42 of Palo Alto Networks has tracked these operations, describing the group as highly skilled in manipulating human psychology for identity compromise.
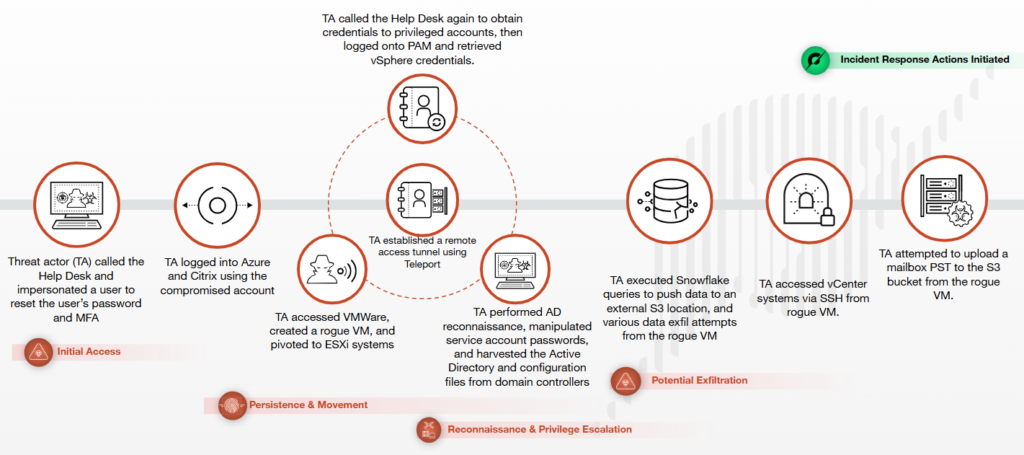
Case Example
In September 2025, Scattered Spider reportedly:
- Called an IT help desk to obtain privileged credentials.
- Created and deployed a virtual machine (VM) for reconnaissance.
- Attempted to exfiltrate Outlook mailbox data and Snowflake database exports.
By leveraging legitimate infrastructure and pre-written scripts, attackers maintain stealth and persistence while reducing the likelihood of detection.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


