A large-scale advertising and click fraud scheme known as SlopAds has been uncovered, involving 224 Android applications with a combined 38 million downloads across 228 countries and territories.
According to the Satori Threat Intelligence and Research Team at HUMAN, these malicious apps employ steganography and create hidden WebViews to secretly connect to attacker-controlled websites, generating fake ad impressions and fraudulent clicks.
The term “SlopAds” reflects both the mass-produced nature of the apps and their connection to AI-related services such as StableDiffusion, AIGuide, and ChatGLM, which the operators hosted on their command-and-control (C2) infrastructure.
At its peak, the campaign was responsible for 2.3 billion daily bid requests, with the majority of fraudulent traffic coming from the United States (30 percent), India (10 percent), and Brazil (7 percent). Google has since removed all affected apps from the Play Store, disrupting the fraud network.
Conditional Fraud Execution
What makes this operation particularly advanced is the conditional activation of fraud. When a SlopAds-linked app is installed, it checks through a mobile marketing attribution SDK whether the installation came from an organic download (direct from Play Store) or a non-organic download (via ad click).
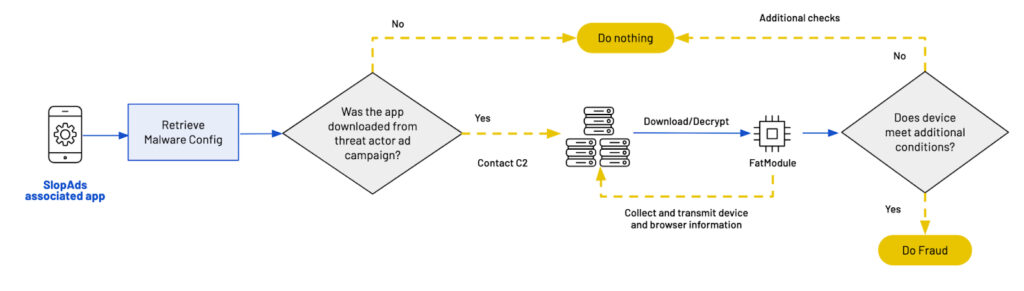
Fraudulent behavior is triggered only when the installation follows an ad click. In such cases, the app downloads an ad fraud module called FatModule from the C2 server. However, if the app was installed organically, it functions normally as described on the Play Store page.
Advanced Obfuscation
HUMAN researchers highlighted that SlopAds demonstrates the growing complexity of mobile ad fraud. The apps were built to commit fraud only in specific conditions while layering multiple levels of obfuscation, making detection more difficult.
This strategy ensures that fraudulent activity blends seamlessly with legitimate advertising data, allowing threat actors to evade researcher scrutiny while maximizing profits.
FatModule Delivery
The FatModule is delivered through four PNG image files, which secretly hide the APK. Once decrypted and reassembled, the APK gathers device and browser information and launches hidden WebViews to perform ad fraud.
Another monetization tactic involves directing users to HTML5 (H5) game and news websites owned by the attackers. Since these sites are loaded within hidden WebViews, they display numerous ads without user awareness, generating revenue through repeated impressions and clicks before the WebView closes.
Infrastructure and Connections
Investigators found that domains promoting SlopAds apps were linked to ad2[.]cc, a Tier-2 C2 server. Overall, about 300 related domains have been identified as part of the scheme.
This discovery comes just two months after HUMAN exposed another fraud campaign involving 352 Android apps, known as IconAds.
Expert Insight
“SlopAds demonstrates the evolving sophistication of mobile ad fraud, with stealthy conditional execution and the ability to scale rapidly,” said Gavin Reid, CISO at HUMAN.