A previously unknown hacking group, codenamed “SmudgedSerpent,” has been uncovered targeting American academics and foreign policy specialists. This cyber espionage campaign, which occurred between June and August 2025, aligns with a period of significantly heightened tensions between Iran and Israel, pointing to a clear intelligence-gathering motive.
Deceptive Lures and Established Playbooks
The threat actor, identified as UNK_SmudgedSerpent, employed sophisticated social engineering tactics. According to Proofpoint security researcher Saher Naumaan, the hackers used politically relevant lures, including topics like societal changes within Iran and investigations into the Islamic Revolutionary Guard Corps (IRGC).
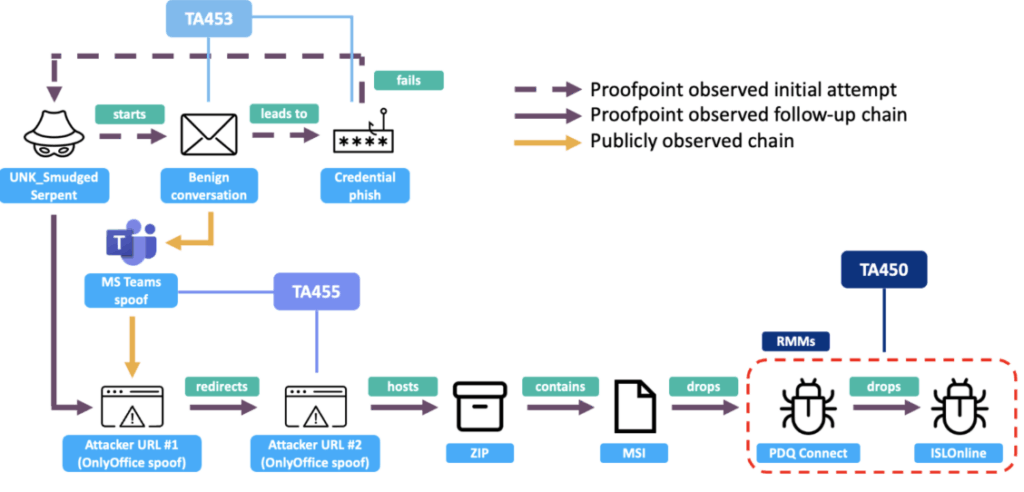
Enterprise security firm Proofpoint noted strong tactical similarities between this campaign and known Iranian state-sponsored groups, including TA453 (Charming Kitten), TA450 (MuddyWater), and TA455. The attacks mirrored the classic “Charming Kitten” approach, where attackers build rapport with targets through harmless conversations before launching credential-phishing attempts.
A Multi-Layered Attack Strategy
The campaign’s methodology was varied and adaptive. Some malicious emails contained URLs that led to a fake Microsoft Teams installer. This installer, an MSI file, ultimately deployed legitimate Remote Monitoring and Management (RMM) software like PDQ Connect—a signature technique of the MuddyWater group.
To enhance credibility, the attackers impersonated well-known U.S. foreign policy figures from prestigious think tanks such as the Brookings Institution and the Washington Institute. This deception was designed to build trust and increase the success rate of their phishing efforts.
The Phishing Conversation Unpacked
The targets included over 20 Iran-focused subject matter experts from a U.S. think tank. In one documented exchange, the hacker displayed a cautious approach, insisting on verifying the target’s identity before any collaboration.
The initial email stated: “I am reaching out to confirm whether a recent email expressing interest in our institute’s research project was indeed sent by you. The message was received from an address that does not appear to be your primary email, and I wanted to ensure the authenticity before proceeding further.”
After establishing contact, the attackers sent a link to what they claimed were meeting documents. Clicking this link directed victims to a fraudulent landing page crafted to steal their Microsoft account credentials. In another variant, the link mimicked a Microsoft Teams login page with a “Join now” button.
Evolution and Adaptation in Real-Time
Proofpoint observed the hackers dynamically adapting their methods. When one target expressed suspicion, the adversary promptly removed the password requirement from their phishing page. Instead, the target was sent directly to a spoofed OnlyOffice login page hosted on a seemingly unrelated domain, “thebesthomehealth[.]com.”
Naumaan highlighted that “UNK_SmudgedSerpent’s reference to OnlyOffice URLs and health-themed domains is reminiscent of TA455 activity,” which has recently shifted from aerospace-themed domains to health-related ones.
The fake OnlyOffice site hosted a ZIP archive containing an MSI installer that launched PDQ Connect. Evidence suggests the attackers then used this access to manually install a second RMM tool, ISL Online, though the reason for using two different RMM programs remains unclear.
Broader Campaign and Strategic Implications
The campaign also targeted a U.S.-based academic and another individual, with lures centered on investigating the IRGC and researching “Iran’s Expanding Role in Latin America and U.S. Policy Implications.”
Proofpoint concluded that these operations are aligned with Iran’s strategic intelligence goals, focusing on Western policy analysis and academic research. The sophistication and blending of tactics from different Iranian groups hint at an evolving cooperation within Iran’s espionage ecosystem, marking a significant shift in its cyber operations.


