A severe security weakness found in the Sneeit Framework plugin for WordPress is currently being abused across live sites, based on information shared by Wordfence.
The flaw, tracked as CVE-2025-6389 with a CVSS rating of 9.8, affects every version up to 8.3. Developers fixed the issue in version 8.4 released on August 5, 2025. The plugin is installed on more than 1,700 active websites.
Wordfence explained that the issue occurs because the function [sneeit_articles_pagination_callback()] accepts user supplied input and forwards it through call_user_func(), allowing an attacker without authentication to execute commands on the server. This capability can be abused to plant backdoors or generate new administrative accounts on the website.
In practice, attackers can trigger arbitrary PHP functions, including wp_insert_user(), to secretly add a malicious admin account. After gaining entry, they can modify the website, redirect users to fraudulent sites, or distribute malicious code and spam.
Large Scale Exploitation Observed
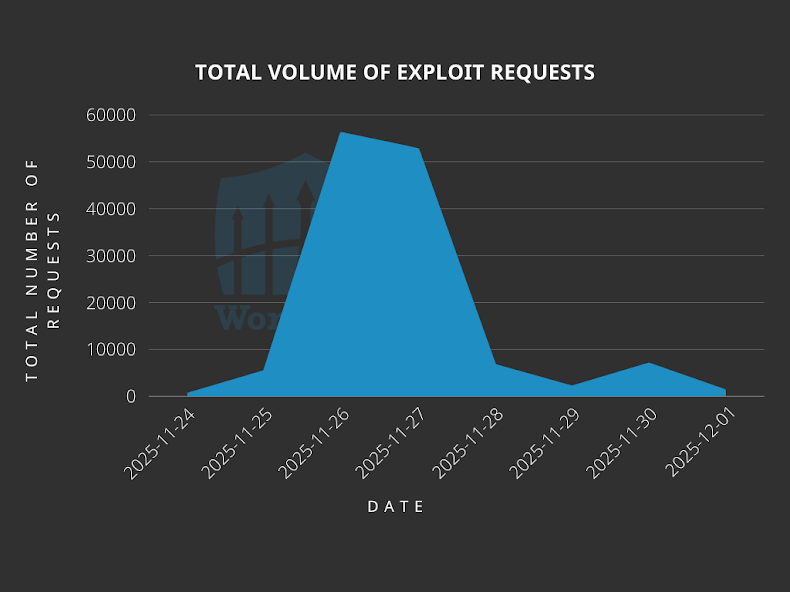
Wordfence confirmed that exploitation began on November 24, 2025, the same day the vulnerability became public. More than 131,000 attack attempts have been blocked so far, with 15,381 of those attempts recorded during the most recent 24 hour period.
Several attacks involved sending crafted HTTP requests to the path “/wp-admin/admin-ajax.php” to generate an admin account named “arudikadis” and upload a backdoor file called “tijtewmg.php.”
The attacks have originated from these IP addresses:
185.125.50[.]59
182.8.226[.]51
89.187.175[.]80
194.104.147[.]192
196.251.100[.]39
114.10.116[.]226
116.234.108[.]143
Wordfence also observed harmful PHP files capable of scanning directories and reading, editing, or deleting files. These files included “xL.php”, “Canonical.php”, “.a.php”, and “simple.php.”
According to Wordfence, the “xL.php” shell is downloaded through a file named “up_sf.php,” which triggers the vulnerability. The same file fetches an “.htaccess” file from “racoonlab[.]top” and places it on the compromised server.
István Márton noted that the “.htaccess” file is designed to ensure access to specific file types on Apache servers, especially in cases where other configuration files block script execution in upload folders.
ICTBroadcast Vulnerability Used to Deploy Frost DDoS Botnet
In a separate development, researchers at VulnCheck reported new attacks involving a critical ICTBroadcast flaw identified as CVE-2025-2611 with a CVSS score of 9.3. The attack chain targeted honeypot systems to download a shell script that retrieves several architecture specific builds of a malware program named “frost.”
Each downloaded version is executed and later removed along with the stager script to erase evidence of the intrusion. The final purpose of this operation is to conduct distributed denial of service attacks on selected targets.
Jacob Baines from VulnCheck stated that the “frost” malware combines DDoS attack features with propagation logic, containing fourteen exploits tied to fifteen CVEs. The malware does not attack every target blindly. Instead, it checks for predefined indicators before launching any exploit attempt.
For example, the program only exploits CVE-2025-1610 after detecting two specific HTTP headers. The first header must contain “Set-Cookie: user=(null)” followed by another that includes “Set-Cookie: user=admin.” If these values do not appear, the malware remains inactive. The attack traffic observed by VulnCheck originated from the IP address 87.121.84[.]52.
Although several botnets have abused these vulnerabilities in the past, researchers believe the current activity is limited and more targeted. Fewer than 10,000 systems are exposed to these issues, which naturally restricts the size of any resulting botnet.
Baines added that the ICTBroadcast exploit used in this attack does not appear inside the frost malware itself, indicating that the threat actor has more tools and capabilities than what is visible so far.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


