A highly capable South Asian Advanced Persistent Threat (APT) group has launched a coordinated cyber-espionage campaign aimed at military personnel and defense organizations across Sri Lanka, Bangladesh, Pakistan, and Turkey.
The attackers are using a multi-layered strategy that combines targeted phishing with custom Android malware to compromise the smartphones of individuals connected to military institutions.
This campaign highlights exceptional operational security and technical expertise, leveraging trusted cloud services and modified open-source tools to avoid detection.

The attack begins with carefully crafted phishing emails containing malicious PDFs disguised as official military documents.
A notable example, titled “Coordination of the Chief of Army Staff’s Visit to China.pdf” (MD5: cf9914eca9f8ae90ddd54875506459d6), illustrates the group’s sophisticated social engineering methods.
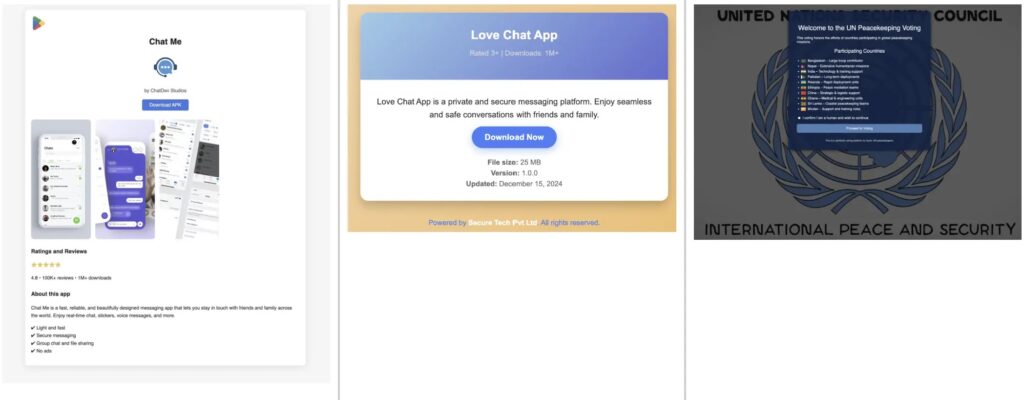
These PDFs direct victims to credential-harvesting pages hosted on compromised Netlify domains such as mail-mod-gov-bd-account-conf-files.netlify.app and coordination-cas-visit.netlify.app, which closely resemble authentic government and military portals.
Analysts at StrikeReady traced the attackers’ infrastructure by examining shared code patterns and domain registration details.
Researchers uncovered over 50 malicious domains impersonating various South Asian military and government entities, including the Bangladesh Air Force, Directorate General of Defence Purchase (DGDP), and Turkish defense firms such as Roketsan and Aselsan.
Modified Android Malware for Persistent Access
The group’s most alarming tool is a customized Android Remote Access Trojan (RAT) based on the open-source Rafel RAT framework.
Distributed through APKs like Love_Chat.apk (MD5: 9a7510e780ef40d63ca5ab826b1e9dab), the malware pretends to be legitimate chat apps while providing continuous backdoor access to compromised devices.
Decompiled analysis shows the malware can exfiltrate multiple types of sensitive documents to command-and-control (C2) servers.
Android RAT Infrastructure
This Android RAT marks a significant advancement in the attackers’ capabilities, demonstrating sophisticated mobile malware development.
The group altered the original Rafel RAT code, removed attribution credits, and created custom C2 communications via domains like quickhelpsolve.com and kutcat-rat.com.
The malware requests dangerous permissions including ADD_DEVICE_ADMIN, READ_EXTERNAL_STORAGE, MANAGE_APP_ALL_FILES_ACCESS_PERMISSION, and READ_CONTACTS, allowing full device control.
Its C2 infrastructure uses base64-encoded communication, with the main command endpoint at https://quickhelpsolve.com/public/commands.php.
This centralized control enables the operators to execute commands, gather stolen data, and maintain persistent access to the victim’s network.
Security researchers confirmed that military personnel across multiple countries were compromised, with exfiltrated data including SMS messages, contact lists detailing military ranks and duty locations, and sensitive organizational documents.


