In a highly targeted cyber espionage campaign uncovered in October 2025, threat actors have been deploying a sophisticated SSH-Tor backdoor by disguising it within weaponized military documents. The attack, aimed at defense personnel, demonstrates a significant evolution in combining social engineering with advanced technical stealth to maintain persistent access to compromised systems.
The Lure: A Deceptive Military Document
The campaign uses a clever social engineering lure. The initial attack vector is a ZIP archive file containing a document titled “ТЛГ на убытие на переподготовку.pdf” (which translates to “TLG for Departure for Retraining”). This document is specifically crafted to appear as a legitimate Belarusian military file, designed to attract the attention of Special Operations Command personnel, particularly those specializing in unmanned aerial vehicle (UAV) operations.
The Sophisticated SSH-Tor Backdoor
Upon successful execution, the malware establishes a powerful backdoor on the victim’s system. Its core components include:
- OpenSSH for Windows: Deploys a secure shell (SSH) server on the compromised Windows machine.
- Custom Tor Hidden Service: Sets up a Tor hidden service with obfs4 obfuscation, a technique designed to disguise Tor traffic and make it difficult to detect or block.
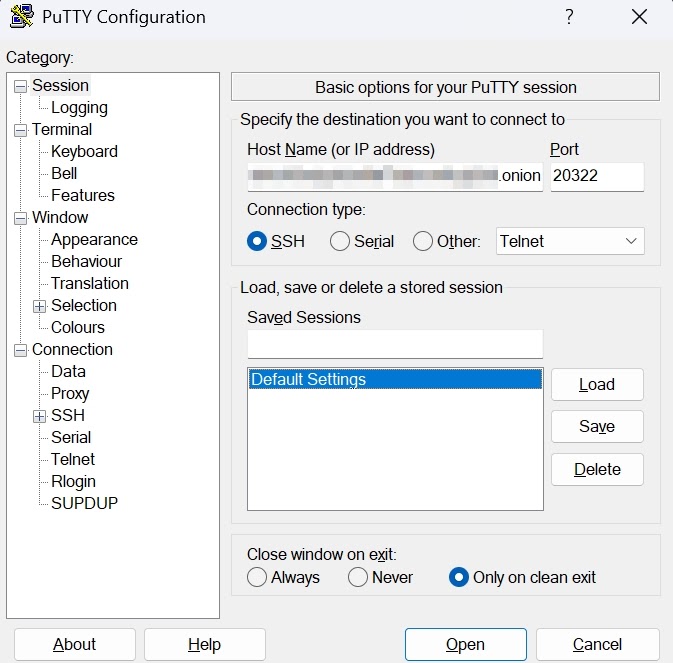
This combination grants the threat actors anonymous, persistent access to the victim’s system. They can remotely use protocols like SSH, RDP (Remote Desktop), SFTP, and SMB, effectively giving them full control. Researchers from Cyble confirmed the backdoor’s functionality by successfully connecting to it via SSH.
Attribution and Connection to Known Threat Actors
Analysis of the tactics, infrastructure, and methods points with moderate confidence to UAC-0125, also known as Sandworm or APT44. This is a Russian-state-linked advanced persistent threat (APT) group infamous for its campaigns against Ukrainian military and critical infrastructure since 2013. The attack mirrors the group’s known patterns from the December 2024 “Army+” campaign, showing a continuous refinement of their techniques.
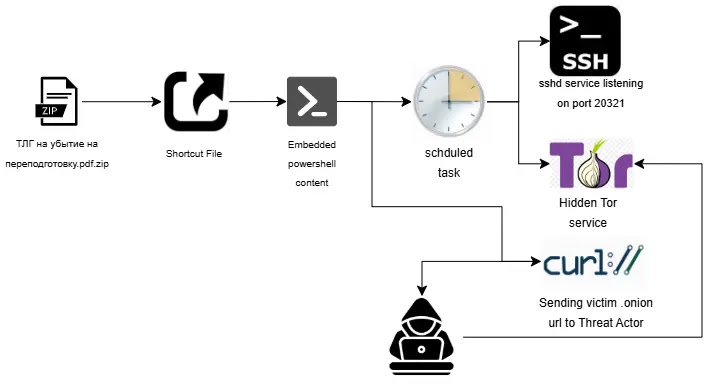
A Multi-Layered and Evasive Infection Chain
The attack uses a sophisticated, multi-stage process to avoid detection.
Nested Archives: The initial ZIP file contains an LNK (shortcut) file disguised as a PDF and a hidden directory named FOUND.000.
The Hidden Payload: This hidden directory contains another archive, persistentHandlerHashingEncodingScalable.zip, which holds the core malicious components.
LNK File Execution: When the victim double-clicks the fake PDF (which is actually the LNK file), it executes a series of embedded PowerShell commands.
Payload Retrieval and Execution: These commands extract the nested archive into the %appdata%\logicpro directory and retrieve obfuscated PowerShell scripts for the next stage.
Advanced Anti-Analysis and Persistence
The second-stage PowerShell script contains clever anti-analysis checks to evade automated security systems (sandboxes). It performs two key validations:
- It checks if at least 10 recently used LNK files exist on the system.
- It verifies that the number of running processes is greater than 50.
These conditions are typically met on a real user’s workstation but are rarely found in sterile sandbox environments. If the checks fail, the malware terminates, avoiding detection by automated analysis tools.
If the checks pass, the script:
- Displays a Decoy: Opens the legitimate-looking PDF document to maintain the victim’s belief that the file is authentic.
- Establishes Persistence: Creates scheduled tasks configured to run at user logon and daily at 10:21 AM UTC, ensuring the backdoor remains active on the system indefinitely.


