Researchers from the CISPA Helmholtz Center for Information Security in Germany have revealed a newly discovered hardware vulnerability in AMD processors that weakens the security guarantees of confidential virtual machines.
The flaw, named StackWarp, affects AMD Zen 1 through Zen 5 architectures and allows a malicious host with administrative privileges to execute unauthorized code inside protected virtual machines. This directly compromises the integrity protections offered by AMD Secure Encrypted Virtualization with Secure Nested Paging (SEV-SNP).
How StackWarp Breaks Confidential VM Isolation
According to the researchers, StackWarp enables a hostile virtual machine host to manipulate the stack pointer of a guest virtual machine. By doing so, attackers can redirect program execution or alter sensitive data inside a confidential VM.
This manipulation makes it possible to achieve both remote code execution and privilege escalation within an environment that is explicitly designed to be isolated from the hypervisor. The attack bypasses SEV-SNP safeguards without requiring access to decrypted memory.
AMD Classification and Affected Products
AMD has assigned the issue the identifier CVE-2025-29943 and rated it as a medium severity vulnerability with a CVSS v4 score of 4.6. The company describes it as an improper access control flaw that allows privileged attackers to interfere with CPU pipeline configuration, ultimately corrupting the stack pointer inside SEV-SNP guests.
The vulnerability impacts multiple enterprise-grade processor families, including:
- AMD EPYC 7003 Series
- AMD EPYC 8004 Series
- AMD EPYC 9004 Series
- AMD EPYC 9005 Series
- AMD EPYC Embedded 7003 Series
- AMD EPYC Embedded 8004 Series
- AMD EPYC Embedded 9004 Series
- AMD EPYC Embedded 9005 Series
Abuse of the Stack Engine Optimization
SEV-SNP is designed to encrypt virtual machine memory and prevent the hypervisor from tampering with guest execution. However, CISPA researchers demonstrated that StackWarp bypasses this protection by exploiting a microarchitectural feature known as the stack engine, which accelerates stack-related CPU operations.
The attack relies on a previously undocumented control bit accessible to the hypervisor. By running a malicious hyperthread alongside the target VM, an attacker can influence stack pointer behavior inside the protected environment.
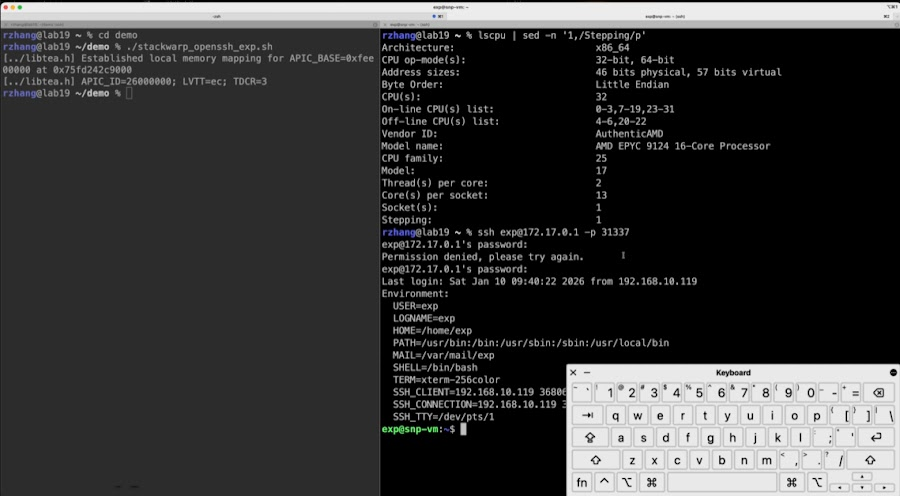
This capability allows adversaries to extract secrets and compromise workloads running in AMD-based cloud environments. In a proof-of-concept scenario, researchers were able to recover an RSA-2048 private key from a single faulty signature. This effectively bypasses OpenSSH authentication and sudo password checks, ultimately leading to kernel-level code execution inside the VM.
Mitigations and Patch Status
AMD has already released microcode updates addressing StackWarp in July and October 2025. Additional AGESA firmware patches for EPYC Embedded 8004 and 9004 processors are scheduled for release in April 2026.
Security experts recommend that operators of SEV-SNP environments review their system configurations immediately. Disabling hyperthreading for workloads with high integrity requirements can reduce exposure until all relevant updates are applied.
Relation to Previous AMD SEV-SNP Attacks
StackWarp builds upon earlier academic research into AMD SEV-SNP weaknesses. In 2023, CISPA disclosed CacheWarp, another hardware-based attack that enabled control-flow hijacking and privilege escalation inside encrypted virtual machines.
Both attacks highlight how subtle CPU microarchitectural behaviors can undermine system-level security guarantees, even in environments designed for confidential computing.
Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


