The threat actor identified as Storm 0249 is expanding its tactics beyond its previous role as an initial access broker and is now deploying more advanced intrusion methods that include domain spoofing, DLL sideloading, and fileless PowerShell execution. These upgraded techniques are being used to support ransomware operations targeting enterprise networks.
In research shared with SCtoCS, ReliaQuest noted that these evolving techniques help Storm 0249 bypass security controls, achieve persistence, and remain undetected inside victim environments, creating significant challenges for defenders.
Microsoft tracks Storm 0249 as an access broker known for selling unauthorized access to various cybercrime groups. These buyers include ransomware and extortion operators such as Storm 0501. The group was first brought to attention in September 2024.
Earlier this year, Microsoft also detailed a Storm 0249 phishing campaign that used tax themed lures to target users in the United States before the tax filing season. That operation delivered payloads such as Latrodectus and the BruteRatel C4 (BRc4) post exploitation toolkit. The purpose of these infections was to secure long term access within enterprise systems, which Storm 0249 then sold to ransomware gangs looking for ready to exploit victims.
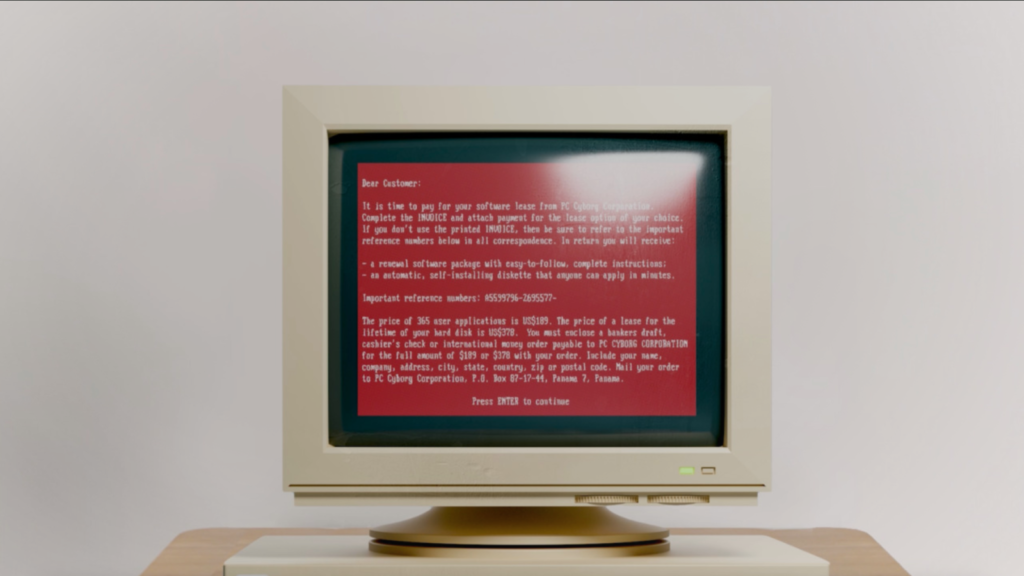
ReliaQuest’s latest analysis shows that Storm 0249 is now adopting the ClickFix method, a socially engineered tactic that deceives users into executing malicious commands through the Windows Run dialog while believing they are resolving a technical error.
In this incident, victims were prompted to run a command that used the legitimate “curl.exe” utility to download a PowerShell script from a URL designed to mimic a Microsoft domain (“sgcipl[.]com/us.microsoft.com/bdo/”). Once executed, the script ran entirely in memory, enabling a fileless attack that avoided traditional detection.
The PowerShell script executed a malicious MSI installer with SYSTEM level privileges. This installer placed a modified DLL linked to SentinelOne’s security solution (“SentinelAgentCore.dll”) into the user’s AppData directory along with the valid “SentinelAgentWorker.exe” file. When the legitimate process launched, it loaded the trojanized DLL, successfully sideloading it without triggering alerts. The rogue DLL then established encrypted contact with its command and control (C2) server.
Storm 0249 was also seen using trusted Windows utilities like reg.exe and findstr.exe to extract identifiers such as MachineGuid, information commonly used in preparing ransomware attacks. Since these commands run under the trusted “SentinelAgentWorker.exe” process and use living off the land techniques, they blend into normal system behavior and evade most security monitoring.
Researchers say this shift reflects a move away from broad phishing campaigns toward more targeted intrusions that leverage trusted, signed processes for stealth and resilience.
“This is more than reconnaissance, it is preparation designed to support ransomware partners,” ReliaQuest stated. They added that groups including LockBit and ALPHV often use MachineGuid to bind encryption keys to individual systems.
By linking the encryption key directly to MachineGuid, attackers ensure that even if defenders obtain the ransomware binary or analyze the encryption method, they still cannot decrypt the compromised files without the attacker controlled key.
Found this article interesting? Follow us on Twitter , Facebook, Blue sky and LinkedIn to read more exclusive content we post.