Malicious Python and npm Packages Uncovered in Supply Chain Attacks
Cybersecurity researchers have uncovered a malicious package on the Python Package Index (PyPI) that introduced harmful behavior through a hidden dependency, enabling persistence and remote code execution.
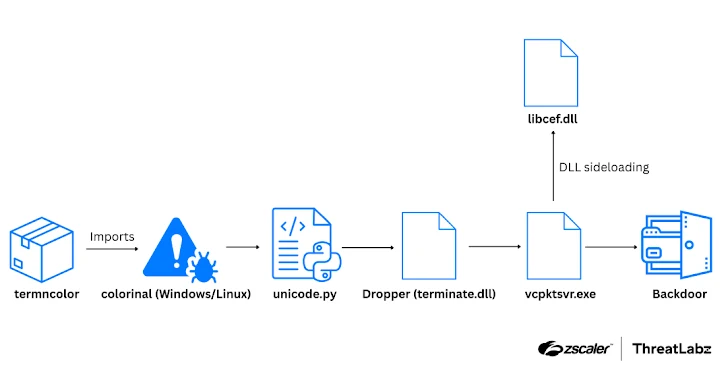
The package, named termncolor, achieved its malicious activity via a dependency called colorinal, as detailed by Zscaler ThreatLabz. Termncolor was downloaded 355 times, while colorinal had 529 downloads before both were removed from PyPI.
According to researchers Manisha Ramcharan Prajapati and Satyam Singh, the attack leveraged DLL side-loading to decrypt data, establish persistence, and perform command-and-control (C2) communication, eventually resulting in remote code execution.
Once executed, termncolor imported colorinal, which then loaded a rogue DLL. This DLL decrypted and launched the next-stage payload.
Malware Execution Process
The payload deployed a legitimate binary (vcpktsvr.exe) alongside a malicious DLL (libcef.dll) through DLL side-loading. This DLL collected system information and secretly communicated with a C2 server using Zulip, an open-source chat application, to remain hidden.
Persistence was achieved by adding a Windows Run registry entry, ensuring the malware automatically launched at startup.
Researchers also confirmed that the malware could target Linux systems by dropping a shared object file named terminate.so, delivering similar functionality.
Further investigation of Zulip logs showed that the attackers had three active accounts within an organization, exchanging over 90,692 messages since July 10, 2025.
Zscaler emphasized that the case highlights the growing importance of monitoring open-source ecosystems to defend against software supply chain attacks.
npm Supply Chain Threats
Meanwhile, researchers at SlowMist revealed that cybercriminals are also targeting developers through fake job assessments, tricking them into cloning GitHub repositories that contain booby-trapped npm packages. These packages are designed to harvest iCloud Keychain data, browser information, and cryptocurrency wallet details, then send the stolen data to external servers.
These npm packages can also download and run Python scripts, capture system details, scan for sensitive files, log keystrokes, steal credentials, take screenshots, and monitor clipboard activity.
The identified malicious npm packages (now removed) included:
- redux-ace (163 downloads)
- rtk-logger (394 downloads)
In recent months, several npm packages have been observed targeting cybersecurity professionals, delivering malware for data theft and cryptocurrency mining. Attackers often disguise these packages as proof-of-concept (PoC) exploits or kernel patches, a tactic linked to the threat actor MUT-1244, according to Datadog researchers Christophe Tafani-Dereeper and Matt Muir.
Risks of Automated Dependency Updates

A separate report from ReversingLabs highlighted the risks of automated dependency upgrades when compromised projects are used by thousands of applications.
This issue was illustrated by the compromise of the eslint-config-prettier npm package, which attackers poisoned using a phishing attack. They managed to upload malicious versions directly to the npm registry without GitHub commits or pull requests.
Security researcher Karlo Zanki explained that since eslint-config-prettier is only a development tool for code formatting, it should be listed as a devDependency rather than a regular dependency. Incorrect categorization allowed Dependabot to automatically merge updates without review, spreading the malicious versions widely.
ReversingLabs concluded that while tools like Dependabot are meant to reduce dependency risks, they can ironically introduce larger threats if attackers compromise trusted packages.


