A recent study conducted by OMICRON has uncovered serious cybersecurity shortcomings within operational technology networks used across substations, power plants, and control centers globally. The assessment, which analyzed more than 100 real world energy installations, reveals repeated technical, organizational, and functional weaknesses that continue to expose critical infrastructure to cyber threats.
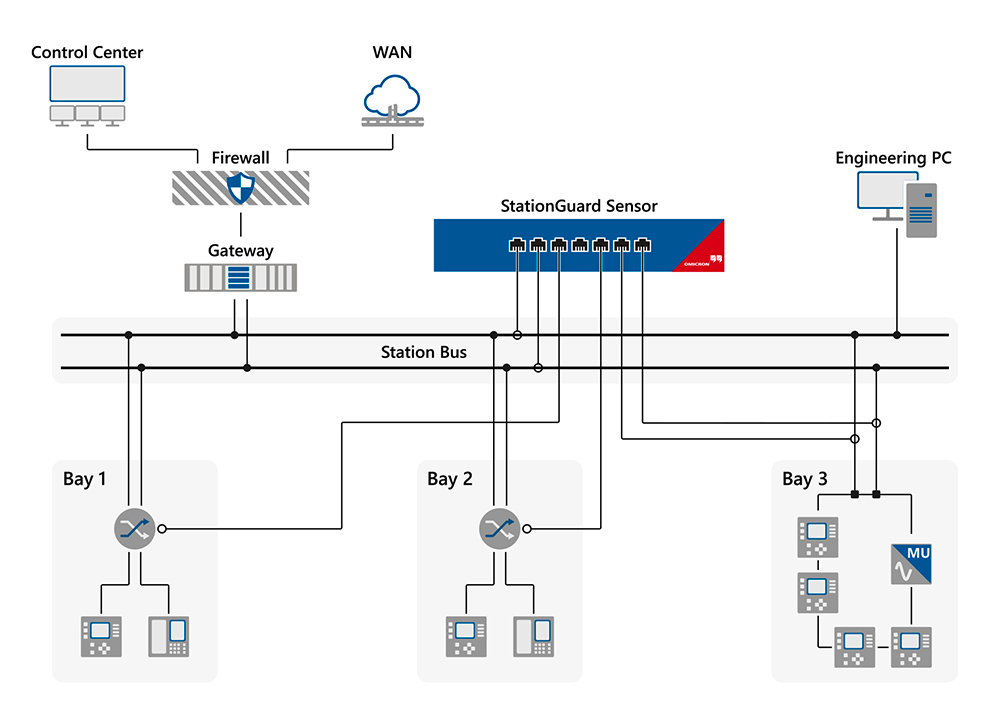
The research is based on multiple years of deploying OMICRON’s intrusion detection system, StationGuard, across protection, automation, and control environments. This passive monitoring technology provided detailed insight into live OT networks, highlighting how expanding attack surfaces and aging systems are increasing risk across the energy sector.
Security Gaps Discovered Within Minutes
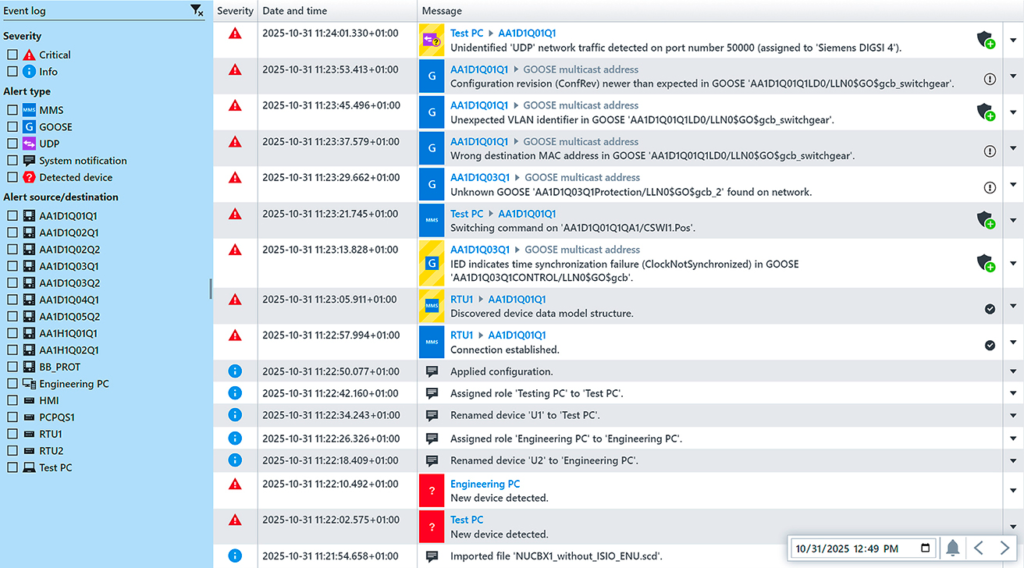
Many StationGuard deployments were performed as part of security audits. In numerous cases, serious vulnerabilities were identified within the first 30 minutes of network visibility. These included outdated firmware, insecure external connections, poor network segmentation, and incomplete or inaccurate asset inventories.
Alongside cybersecurity risks, operational issues were also detected, such as VLAN configuration errors, synchronization problems, and weaknesses in network redundancy. These findings emphasize that cybersecurity and operational reliability are closely linked in OT environments.
Organizational challenges further compound the problem. Unclear ownership of OT security, limited staffing, and strict separation between IT and OT teams remain common. As IT and OT systems increasingly converge, many utilities struggle to adapt their security strategies fast enough to match the evolving risk landscape.
Why Intrusion Detection Is Essential for OT Networks
Incident detection is a core requirement in major cybersecurity frameworks such as the NIST Cybersecurity Framework, IEC 62443, and ISO 27000 standards. However, most OT devices in substations and power plants do not support traditional endpoint security software due to their specialized hardware and firmware.
As a result, monitoring must occur at the network level. StationGuard is typically deployed using mirror ports or Ethernet TAPs, allowing passive observation of all communications without disrupting operations. Beyond threat detection, the system offers several operational advantages:
- Clear visualization of network communication
- Identification of unnecessary services and risky connections
- Automated asset discovery and inventory creation
- Vulnerability identification based on detected devices
How the Assessment Was Conducted
The findings are drawn from several hundred IDS installations conducted since 2018 across dozens of countries. Each deployment focused on high value network locations, including gateways and critical entry points, to capture essential traffic flows.
The results were categorized into three main areas:
- Technical cybersecurity risks
- Organizational security weaknesses
- Operational and functional problems
In most environments, critical issues were visible almost immediately after IDS activation.
Asset Blind Spots and Hidden Devices
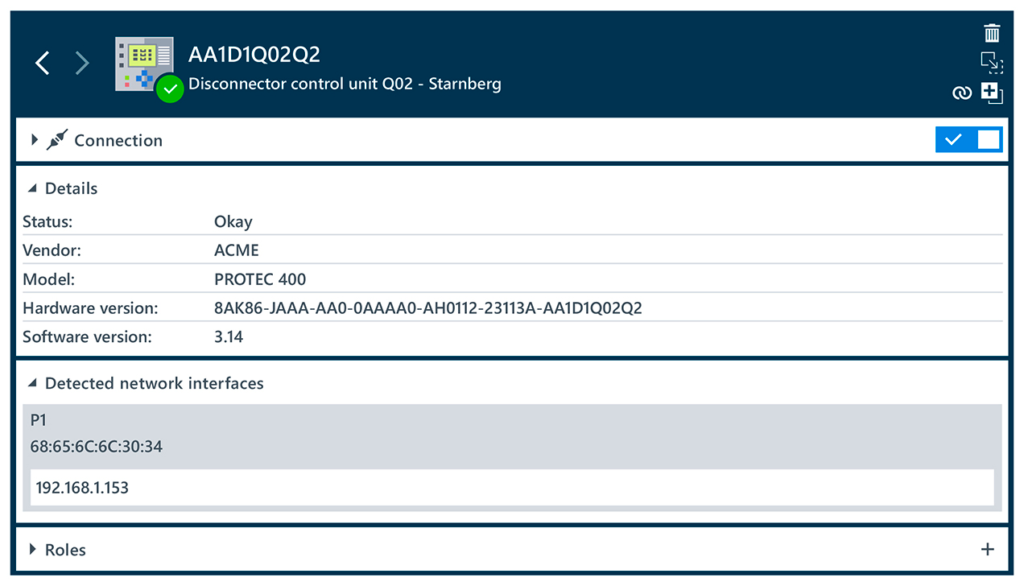
Accurate asset visibility remains a major challenge in energy systems. Manual inventory processes are often outdated and incomplete. To address this, OMICRON used both passive and active asset discovery techniques.
Passive identification relied on IEC 61850 SCD files, which describe system configurations. However, these files often lack details such as firmware versions. Active discovery using the MMS protocol allowed retrieval of detailed device information, including manufacturer data, model numbers, firmware levels, and hardware identifiers. Together, these methods delivered a more reliable and complete asset inventory.
Common Technical Cybersecurity Risks Identified
The analysis revealed several recurring technical vulnerabilities across energy OT networks:
Outdated PAC devices
Many devices were running firmware with known vulnerabilities. One example is CVE-2015-5374, which enables denial of service attacks on protective relays using a single UDP packet. Despite available patches, many systems remain unprotected.
Unsafe external connectivity
Multiple sites contained undocumented TCP or IP connections, in some cases exceeding 50 persistent external connections within a single substation.
Unnecessary insecure services
Unused services such as NetBIOS, IPv6, privileged license services, and exposed PLC debugging functions were frequently observed.
Poor network segmentation
Flat network designs allowed unrestricted communication between hundreds of devices. In extreme cases, corporate IT networks were reachable from remote substations.
Unknown devices
Unregistered IP cameras, printers, and automation equipment appeared on OT networks without documentation, creating serious monitoring blind spots.
Organizational Challenges Increase Cyber Risk
OMICRON also identified recurring human and organizational issues that weaken OT security efforts. These include strict separation between IT and OT teams, lack of dedicated OT security specialists, and limited budgets for security improvements.
In many utilities, IT departments remain solely responsible for OT cybersecurity, a model that often fails to address the specialized requirements of energy infrastructure environments.
Operational Failures Affect Reliability
Beyond cybersecurity, the IDS deployments uncovered operational problems that impact system availability and resilience:
- VLAN misconfigurations affecting GOOSE message delivery
- RTU and SCD mismatches disrupting SCADA communication
- Time synchronization errors caused by misconfigured clocks or incorrect time zones
- Network redundancy failures involving RSTP loops and switch misconfigurations
These issues not only reduce reliability but also increase the potential impact of cyber incidents.
Key Takeaways for Energy Utilities
The study highlights an urgent need for security solutions specifically designed for operational technology environments. Traditional IT security tools alone are insufficient for protecting critical energy systems.
With deep protocol awareness and detailed asset visibility, the StationGuard solution enables utilities to detect anomalies, enforce allowlisting, and identify known threats in real time. Its support for both IT and OT protocols, including IEC 104, MMS, and GOOSE, allows comprehensive monitoring across all network layers.
Features such as automated asset inventories, role based access control, and seamless integration with existing security workflows help organizations improve resilience without disrupting operations.

Found this article interesting? Follow us on X (Twitter) , Facebook, Blue sky and LinkedIn to read more exclusive content we post.


