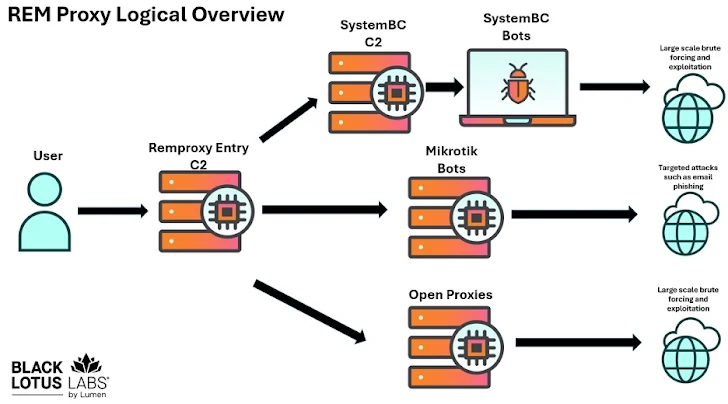
A malware-based proxy network called REM Proxy is driven by SystemBC, providing roughly 80% of the botnet’s capacity to its users, according to the latest research from Black Lotus Labs at Lumen Technologies.
“REM Proxy is a large-scale network that also offers access to about 20,000 Mikrotik routers and multiple open proxies discovered online,” the report shared with The Hacker News stated. “It is a preferred service among threat actors like those behind TransferLoader, linked to the Morpheus ransomware group.”
SystemBC is a malware written in C that converts infected machines into SOCKS5 proxies, enabling them to communicate with a command-and-control (C2) server and download further payloads. First identified by Proofpoint in 2019, it targets both Windows and Linux systems.
Earlier this January, ANY.RUN reported that the Linux version of the SystemBC proxy implant appears designed for internal corporate networks, targeting corporate servers, cloud infrastructures, and IoT devices.
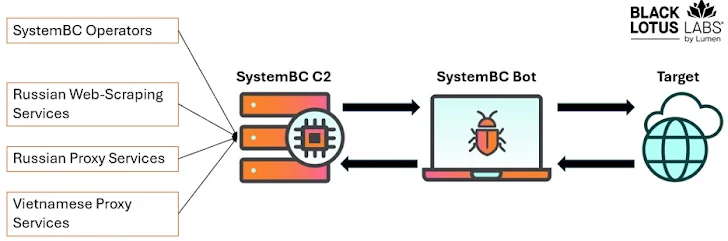
Typically, REM Proxy users connect to SystemBC C2 servers over high-numbered ports, which then route traffic through the infected victims before reaching the final destination.
According to Lumen, the SystemBC botnet runs over 80 C2 servers with an average of 1,500 daily victims, almost 80% of which are compromised virtual private servers (VPS) from major providers. Notably, around 300 of these victims are also part of another botnet, GoBruteforcer (GoBrut).
Nearly 40% of these infected VPS machines maintain long-lived infections exceeding 31 days. Most victim servers are vulnerable to multiple known security flaws, averaging 20 unpatched CVEs and at least one critical CVE, with one U.S.-based VPS in Atlanta exposed to over 160 unpatched CVEs.
“The compromised servers act as proxies that handle large volumes of malicious traffic for various criminal threat groups,” Lumen noted. “By exploiting VPS systems rather than residential IPs, SystemBC provides proxies with high bandwidth and extended uptime.”
Besides REM Proxy, other SystemBC clients include at least two Russia-based proxy networks, a Vietnamese proxy service called VN5Socks (aka Shopsocks5), and a Russian web scraping service.
A critical element for the malware’s operations is IP 104.250.164[.]214, which hosts malware artifacts and is used to recruit new victims. Infected machines are dropped with a shell script to install the malware automatically.
The botnet operates aggressively without prioritizing stealth, aiming to maximize the number of infected devices. SystemBC actors themselves use the network to brute-force WordPress credentials, which are often sold on underground forums to other cybercriminals who inject malicious code into targeted sites.
“SystemBC has maintained continuous activity and resilience over multiple years, evolving from ransomware campaigns to providing custom botnet assembly and sales,” Lumen explained.
“This model allows widespread reconnaissance, spam distribution, and other activities while reserving selective proxy resources for targeted attacks based on gathered intelligence.”